U.S. State and Local Government Under Ransomware: 2025–2026 Trend Analysis
U.S. state and local government organizations remain under growing pressure from ransomware, making the issue a major cybersecurity and public service concern in 2025 and 2026. From city administrations and county offices to school districts, courts, and public safety agencies, these institutions rely on connected systems to manage essential services, sensitive records, and day-to-day operations.
As ransomware threats continue to evolve, the impact on the U.S. public sector goes far beyond encrypted files or temporary IT outages. Attacks on state and local government can disrupt payments, delay emergency response functions, interrupt access to records, and create long recovery periods for agencies already working with limited resources. This 2025–2026 trend analysis examines how ransomware is affecting U.S. state and local government, why these organizations remain frequent targets, and what the latest data reveals about the scale and direction of the threat.
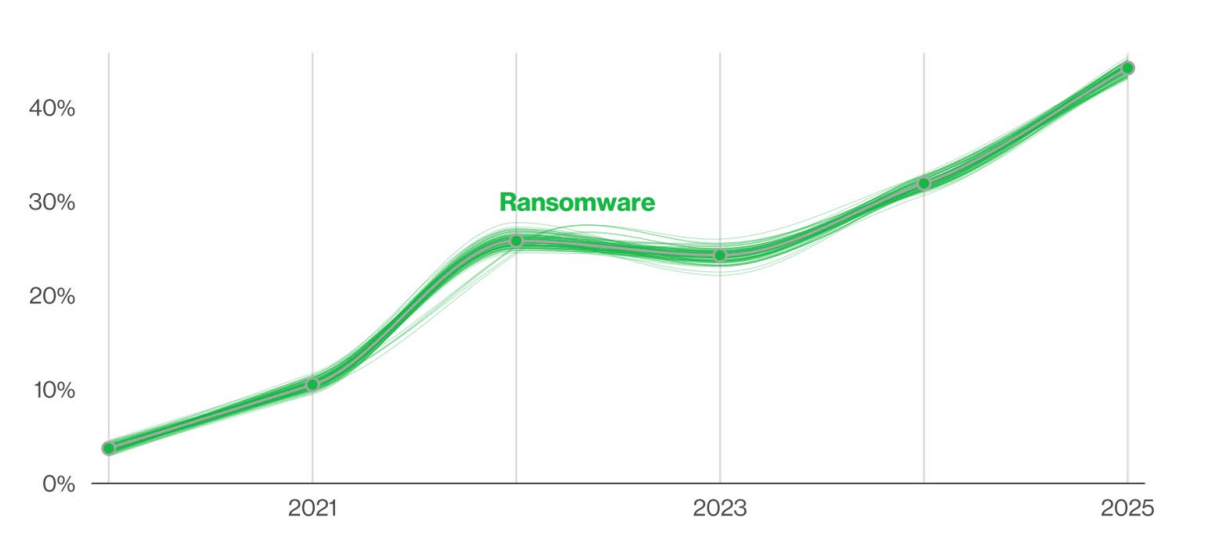
Ransomware growth year by year (Verizon’s 2025 DBIR report)
Verizon’s 2025 DBIR found ransomware in 44% of breaches overall, up from 32% in the previous reporting cycle. In the public sector snapshot tied to the same report, ransomware appeared in 30% of public sector breaches. That makes it clear that government organizations are not just exposed to the wider ransomware trend. They are directly inside it.
SLTT Government Face Persistent Ransomware Risk
State, Local, Tribal, and Territorial government remain attractive ransomware targets because they combine sensitive data, essential public services, and limited operational flexibility. For many SLTT organizations, even a short outage can interrupt payments, delay citizen services, disrupt access to records, and create immediate pressure to restore systems quickly. That urgency gives ransomware actors leverage, especially in environments where downtime directly affects daily public operations.
The risk across SLTT government is also shaped by uneven cybersecurity maturity. One agency may rely on newer cloud-based systems and stronger identity controls, while another still depends on legacy infrastructure, older endpoints, or software that is more difficult to patch and monitor. Third-party providers can expand that exposure further, especially when they support public-facing services, payment systems, or records management.
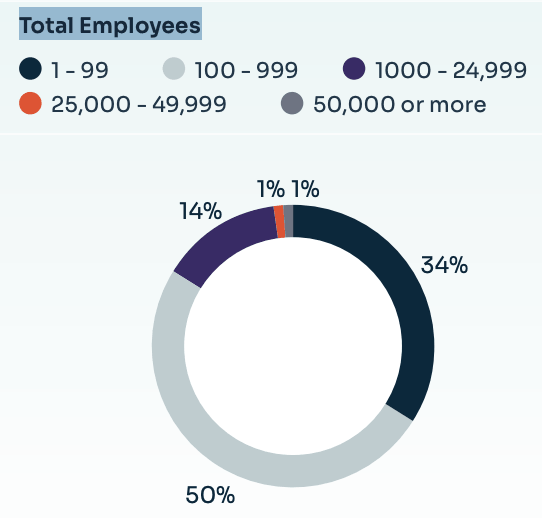
SLTT organizations with fewer than five cybersecurity staff included many with hundreds or thousands of employees (KnowBe4 report)
Staffing constraints make the problem worse. According to KnowBe4 report, more than 80% of participating SLTT organizations said they had fewer than five employees dedicated to cybersecurity, including organizations with workforces of up to 24,999 employees. That is a serious limitation when the same teams are expected to manage patching, access control, vendor risk, backups, monitoring, documentation, and incident response at the same time.
State and Local Government Ransomware Trends in 2025 and 2026
Recent data shows that ransomware pressure on local government is not easing. Verizon found ransomware in 44% of breaches overall and 30% of public sector breaches, while SLTT survey data shows many organizations are still trying to manage that risk with limited resources.
Key figures include:
- 44% of breaches in Verizon’s 2025 DBIR involved ransomware
- 30% of public sector breaches involved ransomware
- More than 80% of surveyed SLTT organizations had fewer than five dedicated cybersecurity staff
- 70% cited insufficient funding as a top security concern
- 64% cited increasing threat sophistication
The Financial Impact of Ransomware on State and Local Government
The ransom demand itself is only part of the damage.
The KnowBe4 report cites a Comparitech study of 525 attacks on government organizations that put the average ransom demand per attack at $872,656. It also notes that the broader cost of downtime and lost services across those incidents exceeded $1.09 billion in total, showing that operational disruption often causes even greater damage than the ransom itself.
Sophos State of Ransomware 2025 provides another useful cost view. Its 2025 ransomware study found that the average cost to recover from a ransomware incident, excluding any ransom payment, was $1.53 million. Median ransom demand fell to $1,324,439 and median ransom payment fell to $1 million, but recovery costs remained heavy. That shows why ransomware is still financially damaging even when agencies do not pay.
How Ransomware Attacks Reach U.S. State and Local Government Networks
Ransomware attacks against government organizations now rely on multiple access methods, not just one mistake or one weak point. In many cases, attackers combine technical exploitation, credential theft, phishing, and data exfiltration within the same intrusion. That makes government ransomware attacks harder to stop with a single control and increases the pressure on state and local agencies once attackers get in.
Recent reporting shows that the most common causes behind ransomware attacks were:
- Exploited vulnerabilities at 32%
- Compromised credentials at 23%
- Malicious email at 19%
- Phishing at 18% (Used Sophos State of Ransomware 2025)
That breakdown shows why a narrow defense strategy is not enough. User training matters, but it does not fix unpatched edge devices. Multi-factor authentication matters, but it does not stop every malware delivery attempt or every exploited system. In practice, government agencies need layered defenses because ransomware actors are using layered intrusion methods.
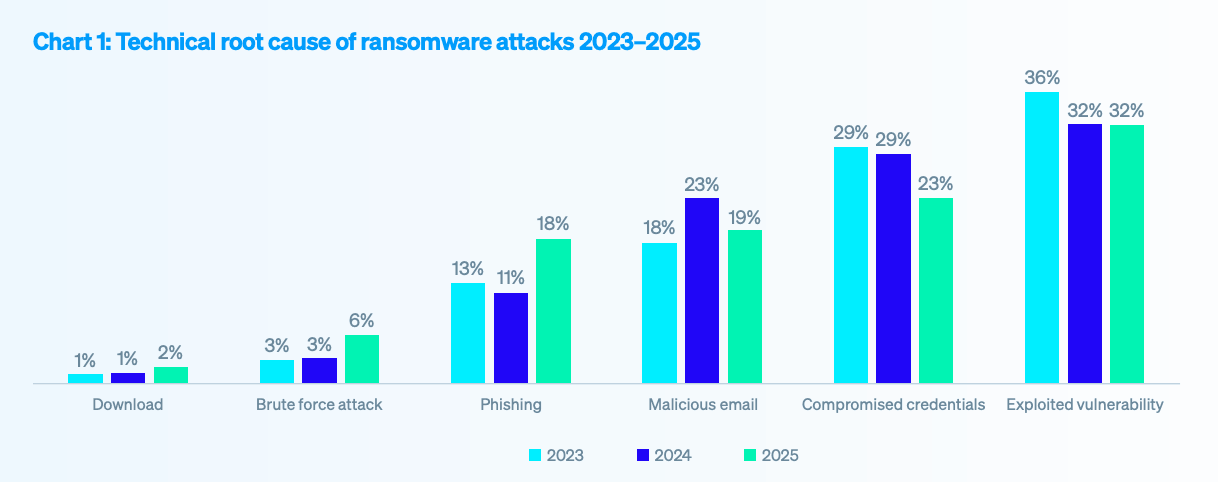
Causes behind ransomware attacks (Sophos State of Ransomware 2025)
Verizon’s 2025 DBIR supports that picture from the initial access side. It found that exploitation of vulnerabilities accounted for 20% of initial access actions, up 34% from the previous year. It also found that edge devices and VPNs represented 22% of targets within exploitation activity. Just as important, only about 54% of edge device vulnerabilities were fully remediated during the year, while the median time to full remediation was 32 days. For government networks with distributed offices, legacy systems, and vendor-connected environments, those are serious exposure points.
Credential Abuse and Data Theft Raise the Pressure
Credential theft remains one of the most effective methods in the ransomware chain because attackers do not always need to break in if they can sign in. Stolen usernames and passwords can give threat actors a quieter way to move through government environments, especially where employees, contractors, and vendors all require access to different systems.
Verizon’s public sector snapshot found that 30% of compromised systems identified in infostealer logs were enterprise-licensed devices. That suggests attackers are stealing credentials from real work devices and later reusing them for broader intrusion activity. In government environments, that can speed up privilege escalation and lateral movement once an attacker gains a foothold.
Ransomware tactics are also changing after access is gained. Sophos report found that data encryption occurred in 50% of attacks, down from 70% the year before. It also found that 28% of victims whose data was encrypted also had data stolen. That means many government ransomware incidents now combine service disruption with data leak pressure, rather than relying only on file encryption.
For state and local government, that creates a wider problem because the stolen data may include:
- employee records
- police reports
- court data
- tax and payment information
- health or benefits records
- resident personally identifiable information
This changes the nature of the incident. A government may restore systems and still face long-term fallout if sensitive data was exfiltrated before encryption. That turns ransomware into both an operational crisis and a privacy crisis, while also increasing the chance that stolen records may later appear in underground spaces monitored through sources such as SOCRadar Dark Web Monitoring.
SOCRadar Dark Web Monitoring can help government organizations strengthen visibility beyond the network perimeter by tracking leaked credentials, exposed personally identifiable information, stealer logs, ransomware-related chatter, and other underground signals that may point to ongoing or upcoming threats.
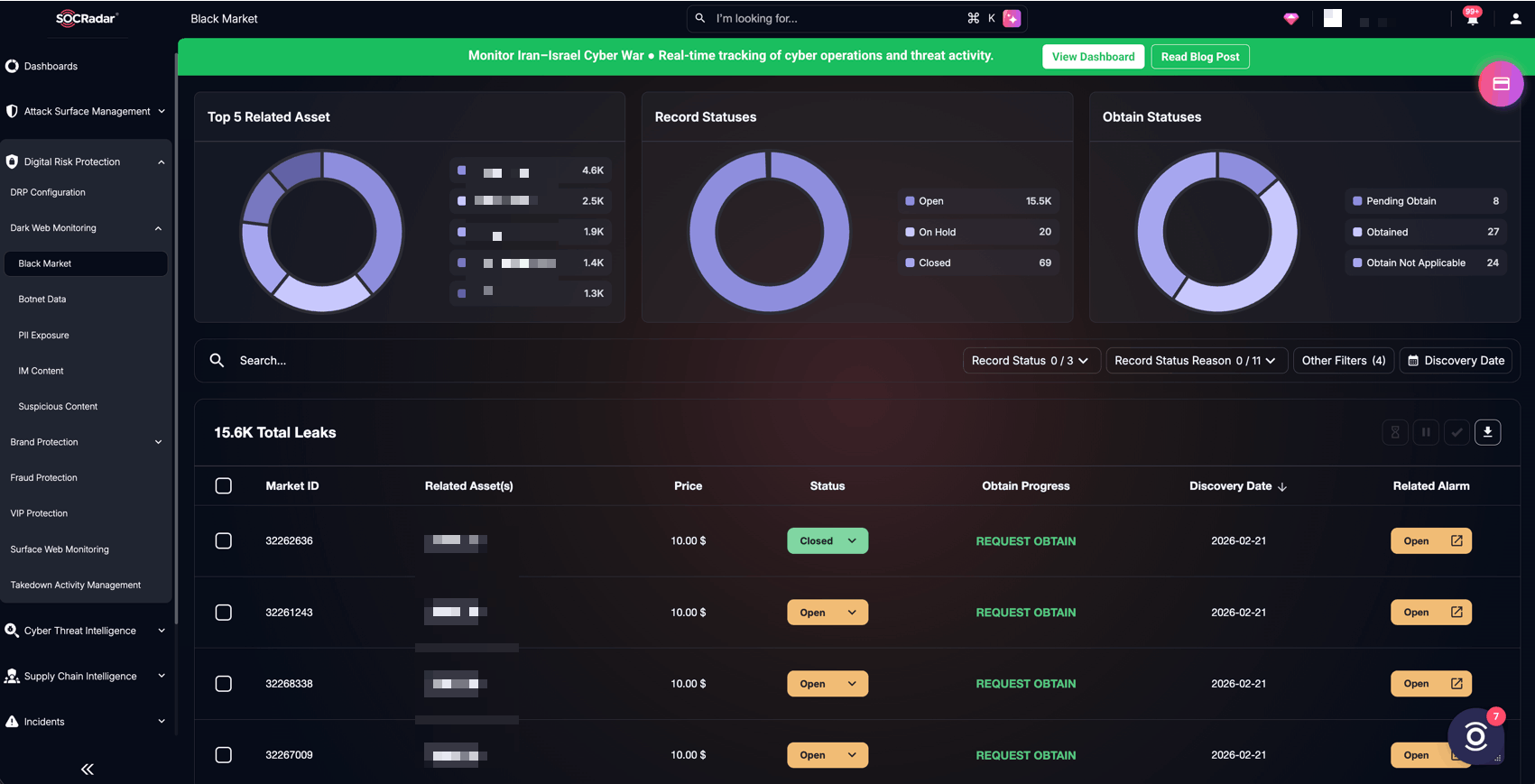
SOCRadar Dark Web Monitoring helps analysts track leaked data, black market listings, and ransomware-related underground activity in one view.
For state and local agencies handling sensitive public records and employee data, that kind of monitoring can support earlier detection, faster investigation, and more informed response when stolen information begins circulating in dark web forums or criminal channels.
Real 2025 Ransomware Incidents Affecting State and Local Government
Public examples from 2025 show how quickly ransomware can disrupt government operations.
New Britain, Connecticut Ransomware Attack, January 2026
A ransomware attack in New Britain, Connecticut, in late January 2026 showed that municipal cyber disruption carried into 2026. The incident affected city network systems for more than 48 hours and forced some departments to rely on manual processes while authorities and outside experts worked to assess and restore affected systems.
Even with the disruption, emergency response and essential city services continued through backup and manual continuity plans. That makes the case especially relevant because it shows how ransomware can still create serious operational strain for local government even when public safety and basic services remain active.
Mission, Texas Ransomware Incident, February 2025
A late February 2025 ransomware incident in Mission, Texas, showed how quickly a cyberattack can affect the daily functioning of a local government. The city reported that its computer network and backup servers were encrypted, cutting off access to a wide range of records, including birth certificates, police reports, contracts, and personnel files. Because the disruption extended across every city department, the incident affected far more than internal IT operations. It limited access to core administrative records and interfered with the city’s ability to carry out normal government processes.
The impact also extended into public safety and service continuity. Some law enforcement functions were disrupted, including tools used to check license plates and support mobile police operations, which added urgency to the response. City officials moved to declare a disaster while systems were being restored, reflecting the scale of the operational interruption.
What Are the Biggest Weaknesses Inside Government Organizations?
The challenge is not only technical. Capacity remains a major issue.
Sophos report found that among ransomware victims:
- 40.2% cited lack of expertise
- 40.1% cited unknown security gaps
- 39.4% cited lack of people or capacity
Those numbers align closely with what many state and local agencies already experience. Security teams are often small, budgets are limited, and modernization takes time. In that environment, even known best practices may be difficult to implement consistently across all departments.
This is one reason ransomware remains so persistent in the public sector. The problem is not lack of awareness. It is lack of time, staff, funding, and operational flexibility.
What Should Agencies Prioritize in 2026?
State and local agencies should focus on practical resilience, not just prevention. Ransomware defense is no longer only about trying to block every attack. It is also about limiting the damage, keeping essential services running, and recovering quickly when systems are disrupted.
In 2026, the strongest government programs will likely be the ones that improve the basics consistently across departments. That includes securing internet-facing systems, tightening access controls, reducing unnecessary vendor exposure, and making sure backups are both protected and regularly tested. Just as important, agencies need better visibility into suspicious activity so they can detect misuse of credentials, unusual movement inside the network, or early signs of system compromise before an incident spreads.
Priority areas should include:
- patching exposed systems and remote access tools quickly
- enforcing multi-factor authentication for privileged and remote users
- limiting unnecessary third-party and vendor access
- maintaining segmented, offline, or otherwise protected backups
- monitoring for suspicious login activity and lateral movement
- testing incident response and recovery plans in advance
Agencies should also treat ransomware readiness as an organization-wide issue rather than only an IT responsibility. Legal teams, communications staff, executive leadership, and operational departments all need to know what their role would be during a disruptive cyber incident. When response planning is shared across the organization, agencies are better positioned to make faster decisions and maintain continuity under pressure.
Awareness training still has value, but it works best as one part of a broader strategy. Employees need to recognize suspicious emails, unusual requests, and risky behavior, but that alone is not enough. More resilient government environments combine user awareness with stronger identity security, clearer asset visibility, tighter vendor oversight, and recovery plans that have been tested before a real crisis occurs.
Conclusion
Ransomware remained a serious and persistent threat to U.S. state and local government throughout 2025 and into 2026. The data shows that these incidents are not isolated disruptions. They are part of a broader pattern affecting public sector organizations that manage essential services, sensitive records, and time-critical operations. For many agencies, the challenge is not only the attack itself, but the combination of limited staffing, uneven cyber maturity, rising recovery costs, and the growing use of credential theft and data exfiltration by attackers.
The examples from Mission and New Britain also show that even when emergency response and core services continue, ransomware can still create major operational strain across departments. That is why the issue should be viewed as more than an IT problem. For state and local government, ransomware is now a continuity, resilience, and public trust issue.
Going into 2026, the most effective response will come from agencies that strengthen the basics, improve visibility, prepare for disruption, and treat cyber readiness as a shared operational responsibility. As ransomware tactics continue to evolve, governments that invest in resilience, coordination, and early detection will be better positioned to reduce impact, protect sensitive data, and keep essential services running when pressure is highest.

