U.S. Institutions and the Dark Web: What’s Being Sold and Who’s Buying?
The modern Dark Web has evolved from a fragmented collection of independent hackers into a highly sophisticated, industrialized economy. The Dark Web market features established business practices, including specialized labor (such as or developers), escrow systems, vendor reputation scores, and commission structures. This professionalized supply chain underpins a global cybercrime economy.
U.S. institutions remain the most frequent targets for this economy. This is largely due to the United States’ position as a global economic and technological powerhouse. The U.S. houses the world’s largest corporations, government agencies, and financial institutions, meaning they hold vast amounts of high-value sensitive data, financial assets, and intellectual property. Furthermore, U.S. critical infrastructure, educational institutions, and federal agencies are increasingly targeted not just for profit, but for strategic pre-positioning, espionage, and influence operations by hostile nation-states. You can check out our for more information
What Is Being Sold from the U.S. Institutions?
Stolen Databases and Personal Records
- Customer databases and Personally Identifiable Information (PII): U.S. organizations are the prime target for data compromises, with customer PII (such as Social Security Numbers, addresses, and dates of birth) being exposed in more than half of all data breaches.
- Healthcare and insurance records: Healthcare data is an exceptionally valuable “forever commodity” because, unlike credit cards, medical histories and patient identities cannot be canceled or altered.
Corporate and Government Access
- VPN, RDP, and admin credentials: Initial Access Brokers (IABs) specialize in selling unauthorized footholds into corporate and government networks, with Remote Desktop Protocol (RDP) and access being the most frequently traded.
- Cloud and enterprise SaaS accounts: Threat actors are increasingly targeting cloud environments by stealing session cookies and OAuth tokens, which allow them to to access enterprise SaaS applications like Salesforce, Microsoft 365, and Cloud Consoles.
- Privileged internal network access: Access is tiered by privilege. Basic user or VPN access provides an entry point into a corporate network and enables initial exploration. Domain Admin or Cloud Admin access is more critical because it provides control over identity systems and infrastructure across the environment.
Financial Data and Payment Assets
- Credit card dumps: Standard U.S. credit card details (including CVV) are highly commoditized due to their higher acceptance rates.
- Bank login credentials: The price for direct access to online bank accounts also scales with the country they belong to.
- Payment gateway and Crypto access: Credentials for payment platforms like Stripe or cryptocurrency exchange accounts (such as Coinbase or Kraken) are highly prized for immediate, untraceable fund transfers.
Intellectual Property and Internal Documents
- Corporate files and contracts: Hackers frequently exfiltrate internal corporate data, such as supply chain logistics, product development IP, and internal contracts, to leverage for extortion or sell to competitors.
- Research data and trade secrets: Educational institutions and research centers are heavily targeted for their information which are highly sensitive aerospace, medical, and artificial intelligence research data. This intellectual property is highly sought after by state-sponsored actors for geopolitical and commercial advantages.
- Government internal documents: Federal and state systems are breached to steal sensitive operational data, ranging from government contracts to highly sensitive law-enforcement surveillance records and federal court data that could expose confidential informants.
Corporate Credentials from Stealer Logs
- Browser credentials, session cookies, and Email/SSO access: (like , , and Stealc) covertly harvests saved browser passwords, corporate email logins, single sign-on (SSO) credentials, and active session cookies. Because stolen session cookies can bypass MFA entirely, they command a significant premium.
Which U.S. Sectors Appear Most Frequently?
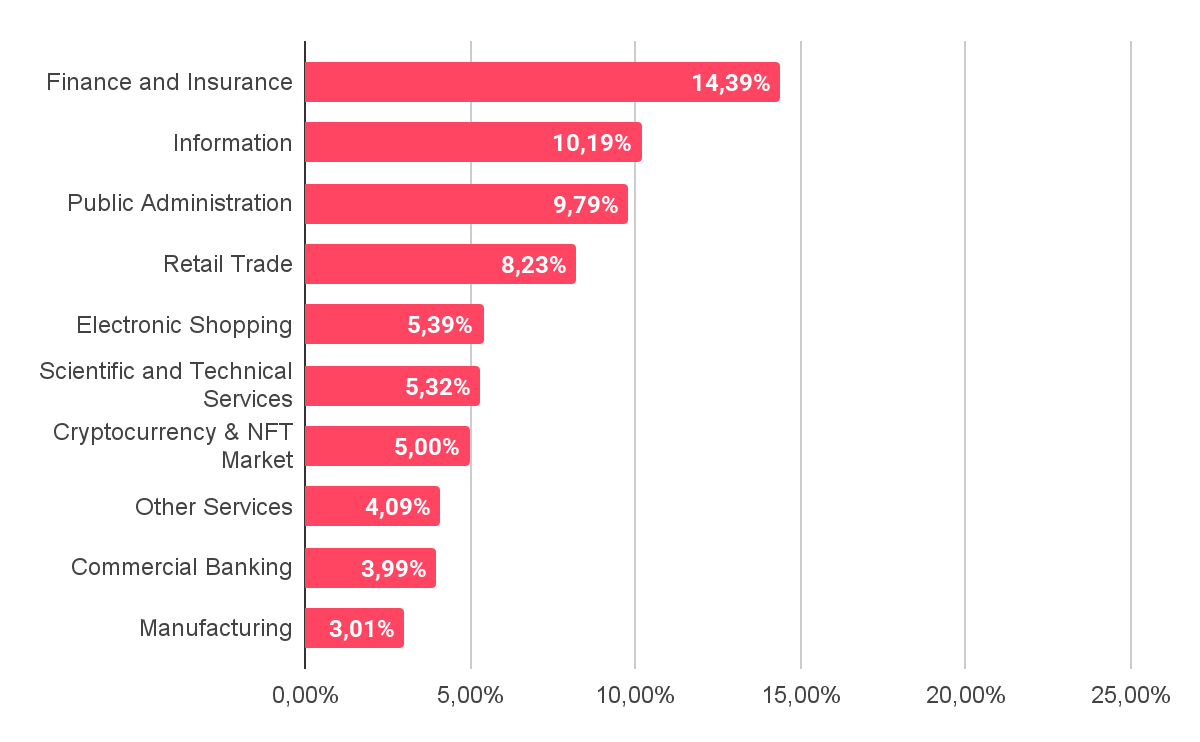
Distribution of Dark Web Threats by Industry,
Finance and Insurance
The financial sector remains one of the most targeted industries. Attackers focus on payment platforms, banking credentials, and financial service accounts because they provide direct access to funds. Compromised payment and banking accounts are widely traded in underground markets. Verified accounts on cryptocurrency exchanges are also valuable because they allow criminals to move funds quickly while bypassing identity checks.
Technology and SaaS Providers (Information)
Technology providers have become strategic targets because they support large digital ecosystems. A breach of one provider can expose many downstream organizations. Several major incidents show how attacks on widely used software or services can affect thousands of companies. Threat actors also focus on enterprise cloud accounts. Stolen OAuth tokens and session cookies allow attackers to bypass authentication controls and access platforms such as Microsoft 365, Salesforce, and other cloud services.
Government and Public Administration
Government systems remain high-value targets for both cybercriminals and state-linked actors. Breaches often expose large citizen databases that contain sensitive personal data such as Social Security Numbers. This information has long-term value because it cannot easily be changed.
Threat actors also seek identity records and official documents that can support fraud or identity abuse.
Federal and state networks are also targeted for strategic access. Incidents involving law enforcement data and judicial systems show how attackers use these environments for espionage or disruption.
Who Is Buying the Data and Access?
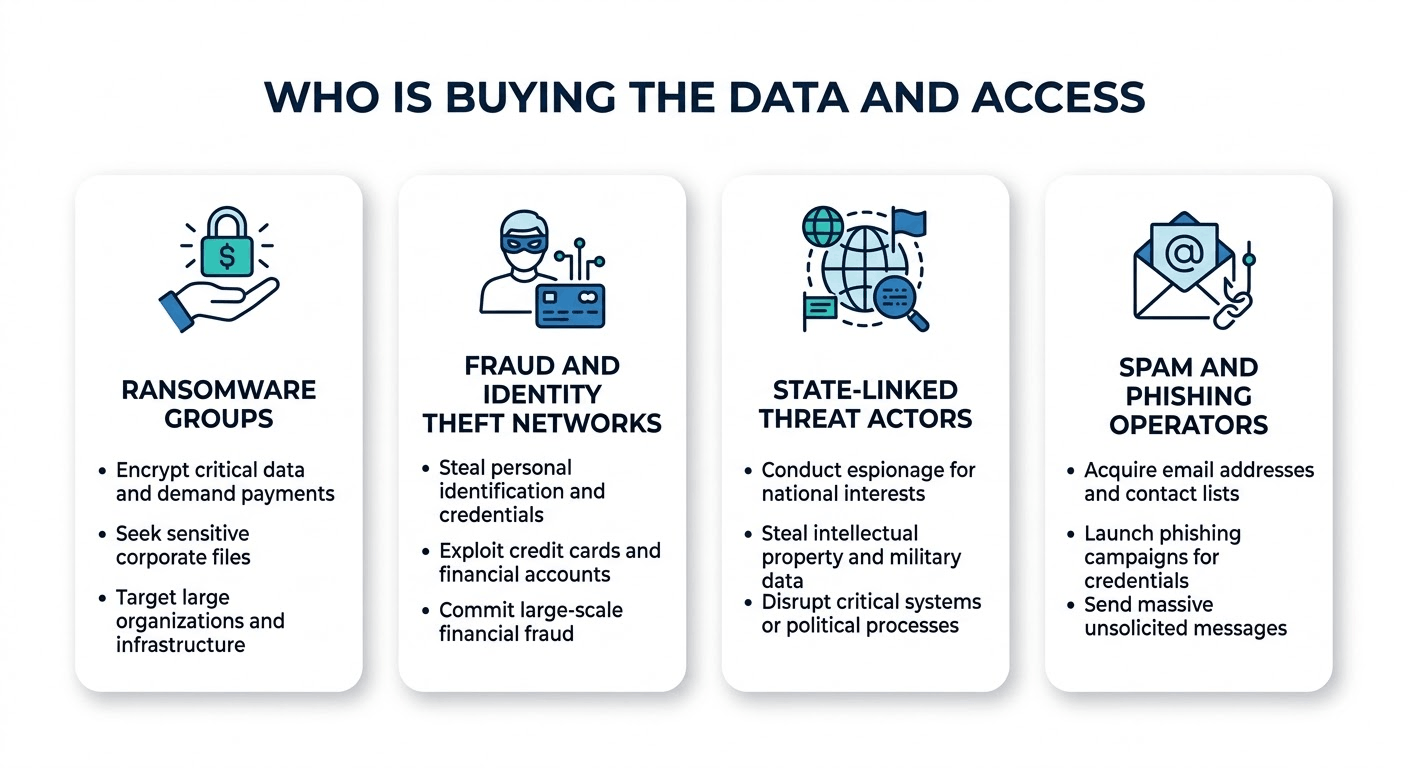
Various threat actors are looking for your data
Ransomware Groups
operators and their affiliates are the primary consumers of Initial Access Broker (IAB) services, purchasing pre-established network footholds to rapidly deploy extortion campaigns.
Instead of wasting time identifying and exploiting vulnerabilities themselves, these financially motivated criminals buy “ready-to-use” access into corporate, healthcare, or government networks to execute attacks within days. This division of labor allows ransomware gangs to focus exclusively on . Furthermore, these groups increasingly utilize double, triple, and quadruple extortion models.
Before deploying ransomware, they exfiltrate highly sensitive files and use the threat of releasing this stolen data on Dark Web leak sites to force victim organizations into paying massive settlements.
Fraud and Identity Theft Networks
Individual fraudsters and organized networks scour and to purchase PII, “Fullz” (complete identity packages), and payment data.
These stolen assets are weaponized for immediate financial theft through account takeovers, utilizing purchased bank logins and verified cryptocurrency accounts to execute untraceable fund transfers. Fraudsters also purchase complete medical records since they are also highly valued as “forever commodities” that are used to conduct complex insurance fraud and blackmail.
State-Linked Threat Actors
from countries like China, Russia, Iran, and North Korea are some of the most sophisticated customers in the Dark Web economy.
While they conduct their own advanced operations, state-sponsored groups increasingly purchase zero-day exploits and network access from IABs to blur the lines between cybercrime and cyber espionage.
They specifically seek access to educational institutions and technology providers to steal highly sensitive aerospace, defense, and artificial intelligence intellectual property. Additionally, these actors buy access to U.S. telecommunications, energy grids, and water treatment facilities not for immediate financial profit, but for strategic purposes.
Spam and Phishing Operators
Spam and operators rely heavily on underground markets to purchase massive credential dumps, stealer logs, and sophisticated Phishing-as-a-Service (PhaaS) kits. These operators purchase compromised corporate email accounts and session cookies to bypass Multi-Factor Authentication (MFA) and infiltrate organizations.
Once inside, they frequently use the trusted, compromised email accounts to launch , manipulating email threads to send convincing phishing links and fraudulent payment instructions to the victim’s partners and supply chain.
A prime example of the evolution of these buyers is a recently uncovered by SOCRadar’s Threat Hunting Team, attributed to a financially-motivated threat actor known as GS7.
This group has spent years targeting Fortune 500 companies and their customers by combining precision brand impersonation, custom phishing infrastructure, and the abuse of legitimate remote management tools to establish persistent access to victim systems.
Between December 2025 and January 2026, GS7 conducted extensive campaigns impersonating major financial institutions and technology companies, including Wells Fargo, USAA, Navy Federal Credit Union, Fidelity Investments, Microsoft, and Citibank. The operation amassed hundreds of malicious domains following consistent infrastructure patterns that reveal a highly automated deployment capability.

Defensive Measures for U.S. Organizations
Dark Web Monitoring and Threat Intelligence
Organizations must maintain continuous visibility into both traditional Tor-based Dark Web forums and messaging apps like Telegram to establish an effective early warning system. By utilizing predictive threat intelligence, security teams can surface exposed data such as employee email addresses, domain names, or proprietary product information before it can be monetized in an attack.
Credential Exposure Detection
If a company’s credentials appear in an illicit dump, even a single hit should trigger immediate automated responses.
- Forcing immediate password resets for all affected users.
- Invalidating active user sessions to neutralize the threat of stolen session cookies bypassing authentication.
- Scanning affected devices for infostealer malware.
- Rotating all associated API keys, tokens, and developer secrets.
- Auditing and disabling inactive “ghost” accounts to prevent attackers from targeting stale, unmonitored credentials.
Supply Chain Risk Monitoring
Organizations need to conduct rigorous due diligence before onboarding new vendors and establish comprehensive vendor management policies that demand transparency, security compliance, and prompt incident reporting.
Modern supply chains require modern security. You can extend your security focus beyond your own perimeter and protect your business from . SOCRadar’s module acts as your proactive shield, allowing you to actively assess the security posture of your continuously expanding supply network so you can mitigate risks and ensure business continuity.
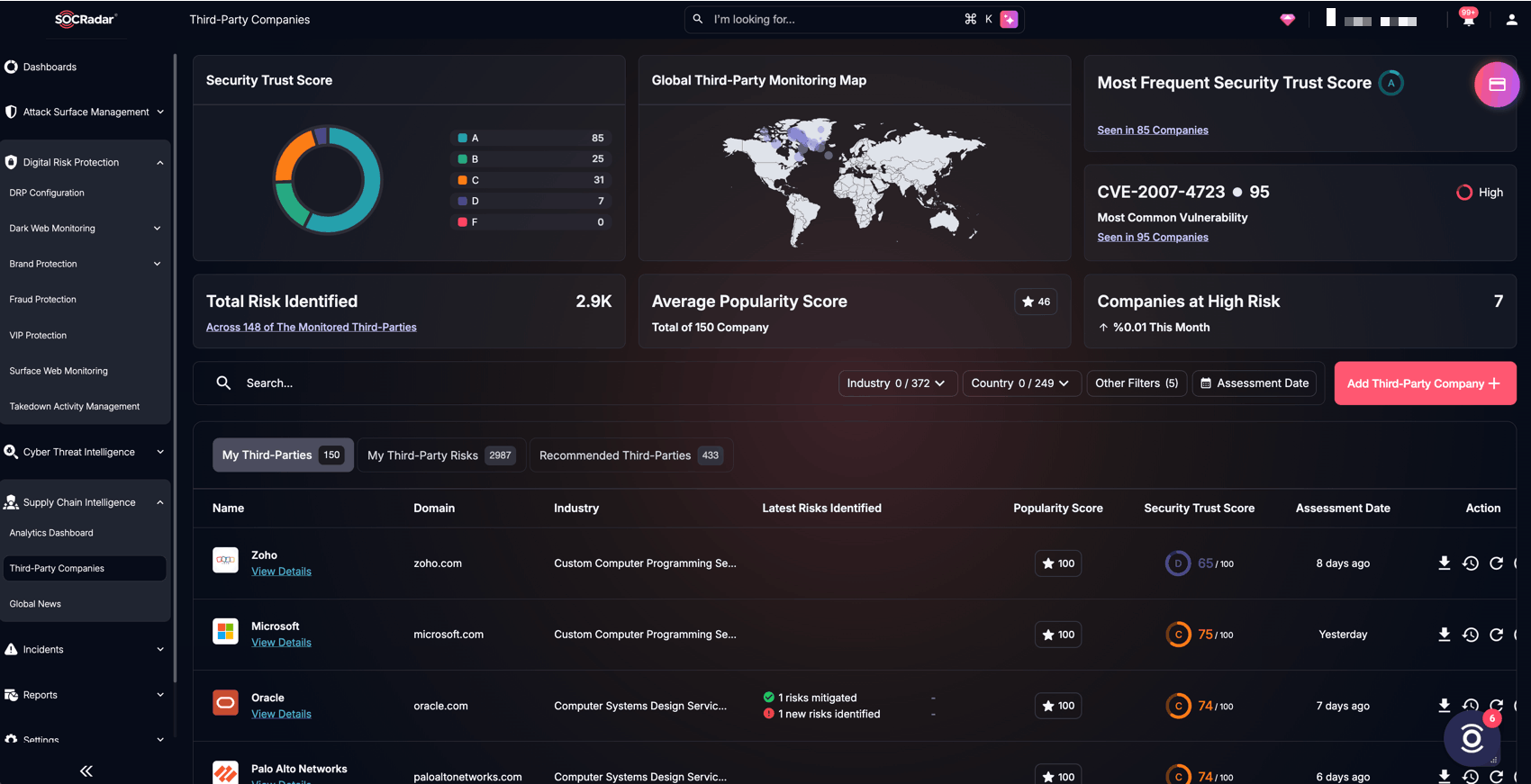
SOCRadar’s Supply Chain Intelligence module’s Third Party Companies
Key Advantages for Your Organization:
- Holistic 360° Visibility: Gain a complete view of your supply chain risk by combining insights from Cyber Threat Intelligence (CTI), Digital Risk Protection (DRP), and Attack Surface Management (ASM).
- Massive Vendor Database: Access intelligence cards for nearly 50 million vendor organizations to instantly evaluate their digital footprint.
- Data-Driven Risk Scoring: Evaluate suppliers using 133 meticulously defined technical assessment checkpoints to receive reliable Security Trust Scores and Popularity Scores.
- Continuous Monitoring & AI Insights: Stay informed with continuous vendor risk monitoring, automated alerts, and an AI Insight Panel that delivers actionable mitigation strategies.
Don’t wait for a disruption to test your resilience. Equip your organization with the tools to proactively identify, prevent, and mitigate security threats across your entire network.
Conclusi̇on
At the center of this illicit ecosystem are U.S. institutions. Particularly within the government, healthcare, financial, and technology sectors, which are heavily targeted due to the immense strategic and financial value of the data they hold.
As explored, cybercriminals are successfully extracting and commoditizing a wide range of assets, including massive databases of Personally Identifiable Information (PII), “forever commodities” like medical records, sensitive intellectual property, and highly privileged corporate network access. The modern cyberattack lifecycle has fundamentally shifted from “breaking in” to “logging in,” driven by a booming market for stolen session cookies, VPN credentials, and authentication logs harvested by infostealer malware.
To survive this landscape, U.S. organizations can no longer rely on static perimeter defenses or reactive measures.
By understanding exactly what is being sold, who is buying it, and how it is monetized, organizations can effectively anticipate threats and harden their most critical vulnerabilities against a sophisticated, collaborative adversary.