Ransomware 3.0: The Autonomous Threat That Changed Everything
Ransomware has changed a lot over time and gone through major shifts, it’s now “Ransomware 3.0.” The changes across the years explain why the threats in 2026 look very different from what security teams faced ten years ago.
Ransomware 1.0 (1989–2018): Encrypt and Demand
The first era was blunt in its approach: encrypt files, demand payment. Early strains like the AIDS Trojan (1989) used symmetric encryption, and later groups including CryptoLocker (2013–2014) added asymmetric keys and a more sophisticated monetization model. By 2017, WannaCry and Petya/NotPetya introduced worm-like propagation, spreading autonomously across networks and reaching global scale. These attacks remained fundamentally transactional, however: the criminal value proposition was availability disruption and extortion payment.

The infamous WannaCry ransom note
Ransomware 2.0 (2019–2022): Double Extortion and the RaaS Revolution
The second era introduced a structural innovation that permanently escalated the stakes. In 2019, the Maze ransomware group pioneered “double extortion“: rather than only encrypting data, attackers exfiltrated it first and threatened to publish it publicly if ransoms were not paid.
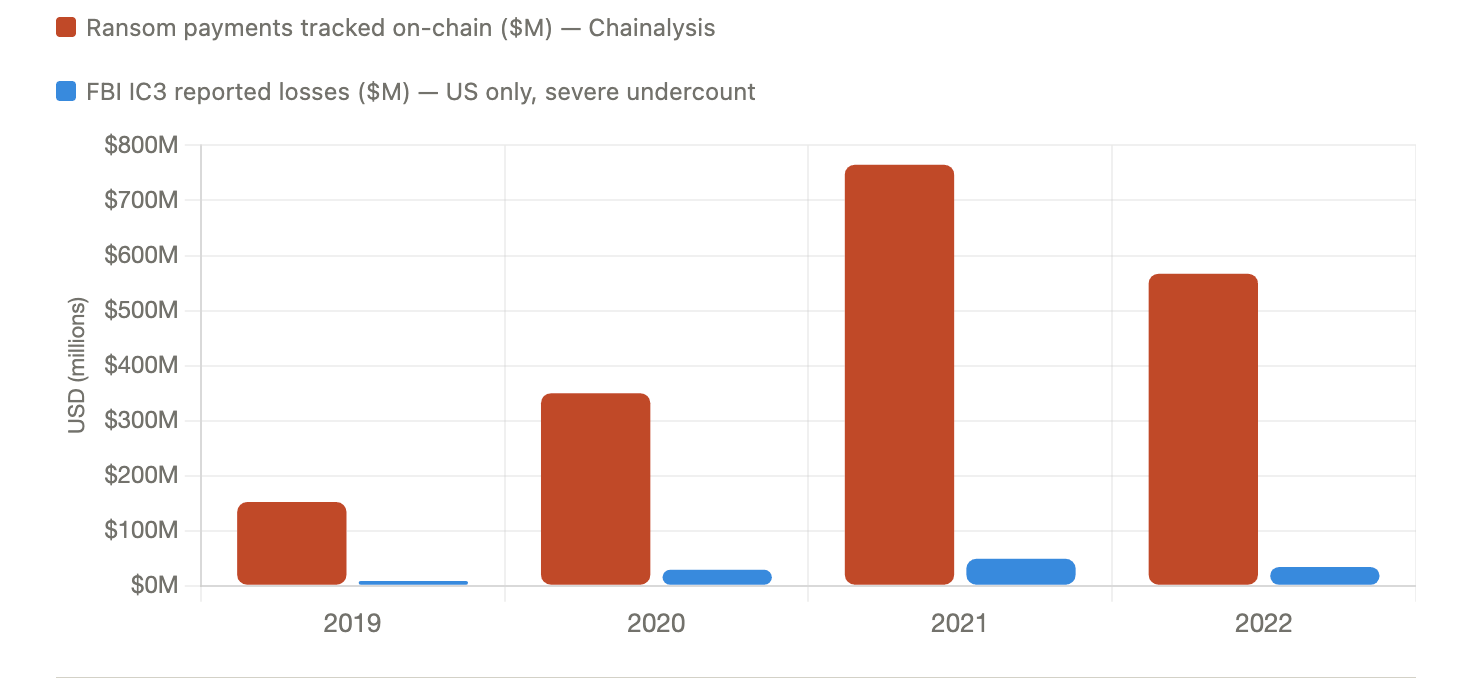
Global ransomware payments surged 5× between 2019 and 2021, peaking at $765M.
This transformed ransomware from a pure availability threat into a combined confidentiality, reputational, and financial attack. The Ransomware-as-a-Service (RaaS) model matured in parallel during this period, democratizing attack capability by allowing less-skilled affiliates to rent complete attack infrastructure. At its peak, LockBit alone was attributed to approximately 44% of all ransomware incidents globally, a market concentration that underscored how industrialized the ecosystem had become.
Ransomware 3.0 (2023–Present): The Autonomous Threat
The third era is categorically different from its predecessors. It integrates agentic artificial intelligence, triple extortion mechanics, decentralized infrastructure, and autonomous self-composition to produce attacks that require no skilled human operator to execute. The scale of this evolution is reflected in the numbers.
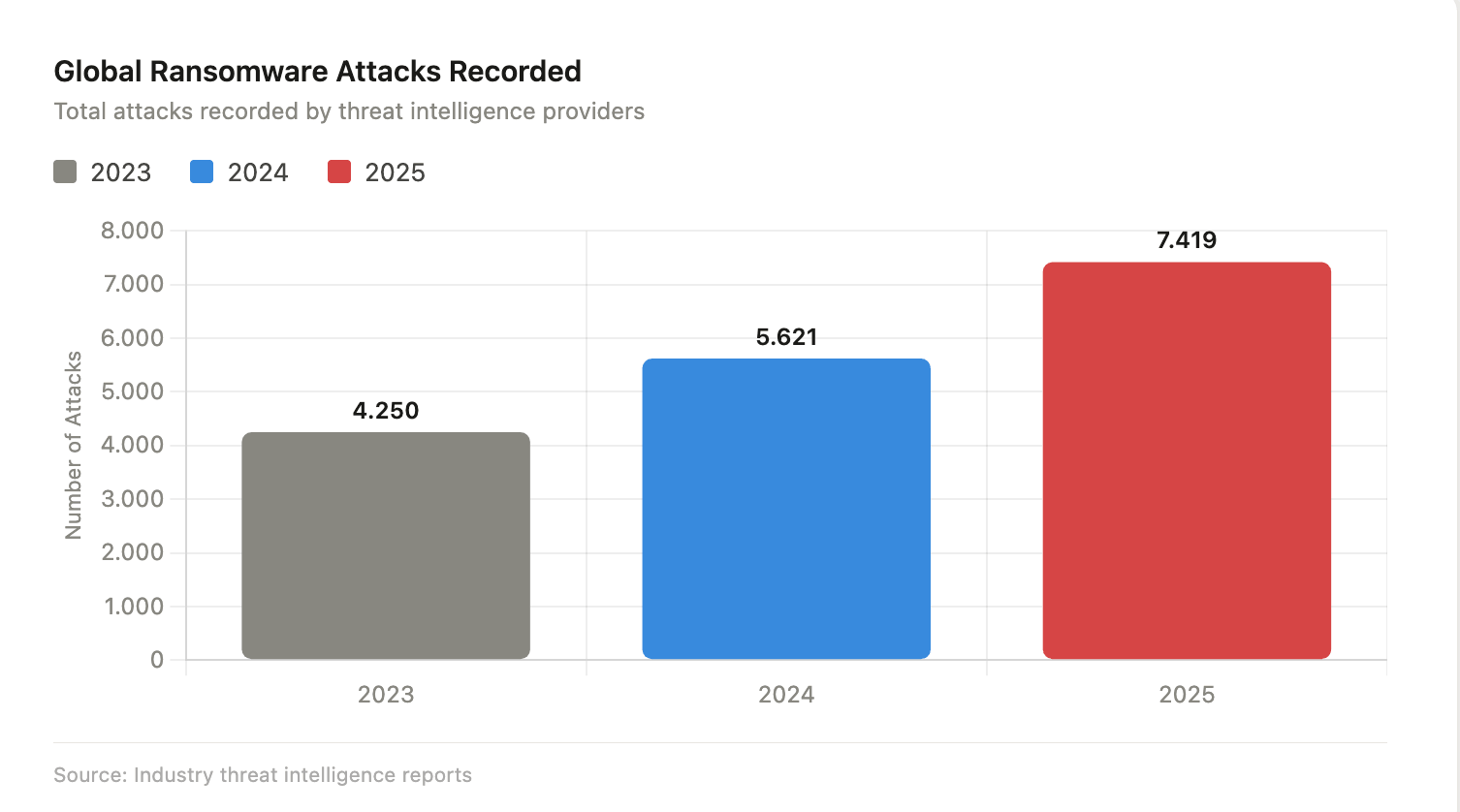
Global ransomware attacks recorded annually. The 32% year-over-year increase to 7,419 incidents in 2025 reflects the accelerating adoption of automated, AI-assisted attack tooling.
Manufacturing has emerged as the hardest-hit sector, suffering a 56% surge in incidents in 2025, driven by the convergence of operational technology (OT) vulnerabilities and the high business-continuity pressure that makes ransomware payments more likely. Healthcare, Financial Services, and Critical ınfrastructure follow closely.
What Is Ransomware 3.0? A Technical Definition
Ransomware 3.0 is best understood as a threat ecosystem, not a single malware family. It is defined by four converging characteristics: autonomous LLM orchestration, triple extortion mechanics, industrialized RaaS infrastructure, and decentralized command-and-control.
“Ransomware 3.0 represents the first threat model and research prototype of LLM-orchestrated ransomware. Unlike conventional malware, the prototype only requires natural language prompts embedded in the binary; malicious code is synthesized dynamically by the LLM at runtime, yielding polymorphic variants that adapt to the execution environment.” — NYU Tandon School of Engineering, August 2025
In August 2025, researchers at NYU Tandon School of Engineering published what is considered the first formal threat model for LLM-orchestrated ransomware. Their research prototype, later discovered on VirusTotal and dubbed “PromptLock” by outside researchers, demonstrated a fully autonomous, closed-loop attack campaign capable of performing reconnaissance, payload generation, and personalized extortion without human involvement.
Industry consensus also encompasses a broader definition that includes the full ecosystem of tactics: EDR-killing tools, supply chain infiltration, AI-powered social engineering, and triple extortion, even where LLM orchestration is not yet present in every deployment.
| Key Characteristic: Four Convergent Properties of Ransomware 3.0
1. Autonomous LLM orchestration — malicious code synthesized at runtime from natural language prompts, producing unique polymorphic payloads on every execution. |
The LLM-Orchestrated Architecture: A Technical Breakdown
The NYU research prototype, implemented in Go for cross-platform compatibility, illustrates the technical anatomy of Ransomware 3.0 at its most advanced.
Binary Structure
The orchestrator binary (approximately 10 MB) contains no pre-compiled malicious code. Instead, it packages a lightweight Lua interpreter, enabling in-memory bytecode execution that never touches disk and leaves no filesystem artifacts, alongside natural language task prompts encoding each attack phase, an HTTP/HTTPS transport module compatible with any OpenAI-compatible LLM API, RSA public keys for wrapping runtime-generated symmetric encryption keys, and an optional C2 server interface for receiving exfiltrated data and generated code.
Lua was specifically chosen for this role because it is embeddable, platform-agnostic, has a minimal footprint, and is commonly found in legitimate software (such as the Apache HTTP Server), significantly reducing suspicion during behavioral analysis.
The Four-Phase Attack Lifecycle
The attack proceeds through four discrete phases, each orchestrated by LLM-generated code at runtime:
Phase 1: Reconnaissance
The LLM generates Lua code that queries the operating system for metadata (OS type, username, hostname, home directory paths) and performs recursive file system enumeration. Output is structured into artifact logs consumed by subsequent phases. Research testing showed near-100% success rates across personal computers, enterprise servers, and embedded industrial controllers.
Phase 2: Leverage
The LLM analyzes the file list and heuristically identifies sensitive targets. It distinguishes high-value files — tax documents, credential exports, production secrets, PLC firmware configurations — from benign ones, and attempts to extract content or metadata for extortion. In testing, a larger 120-billion-parameter research model demonstrated superior sensitivity classification (approximately 69% accuracy) but triggered more policy refusals during extraction attempts; a smaller 20-billion-parameter model was less precise but more compliant, achieving over 90% extraction success rates. This tension between model capability and safety alignment is a defining dynamic of the LLM-ransomware research space.
Phase 3: Payload Launch
A decision-making task selects environment-appropriate payloads. The system maps execution context to consequence: personal computer environments are targeted for exfiltration (identity theft and privacy leverage); enterprise servers for encryption (financial extortion); and embedded industrial controllers for destructive payload delivery (denial-of-service or sabotage). Encryption payloads implement a SPECK-128 cipher entirely in LLM-generated Lua code; exfiltration uses HTTP POST uploads; destruction performs multi-pass file overwriting before deletion to resist forensic recovery.
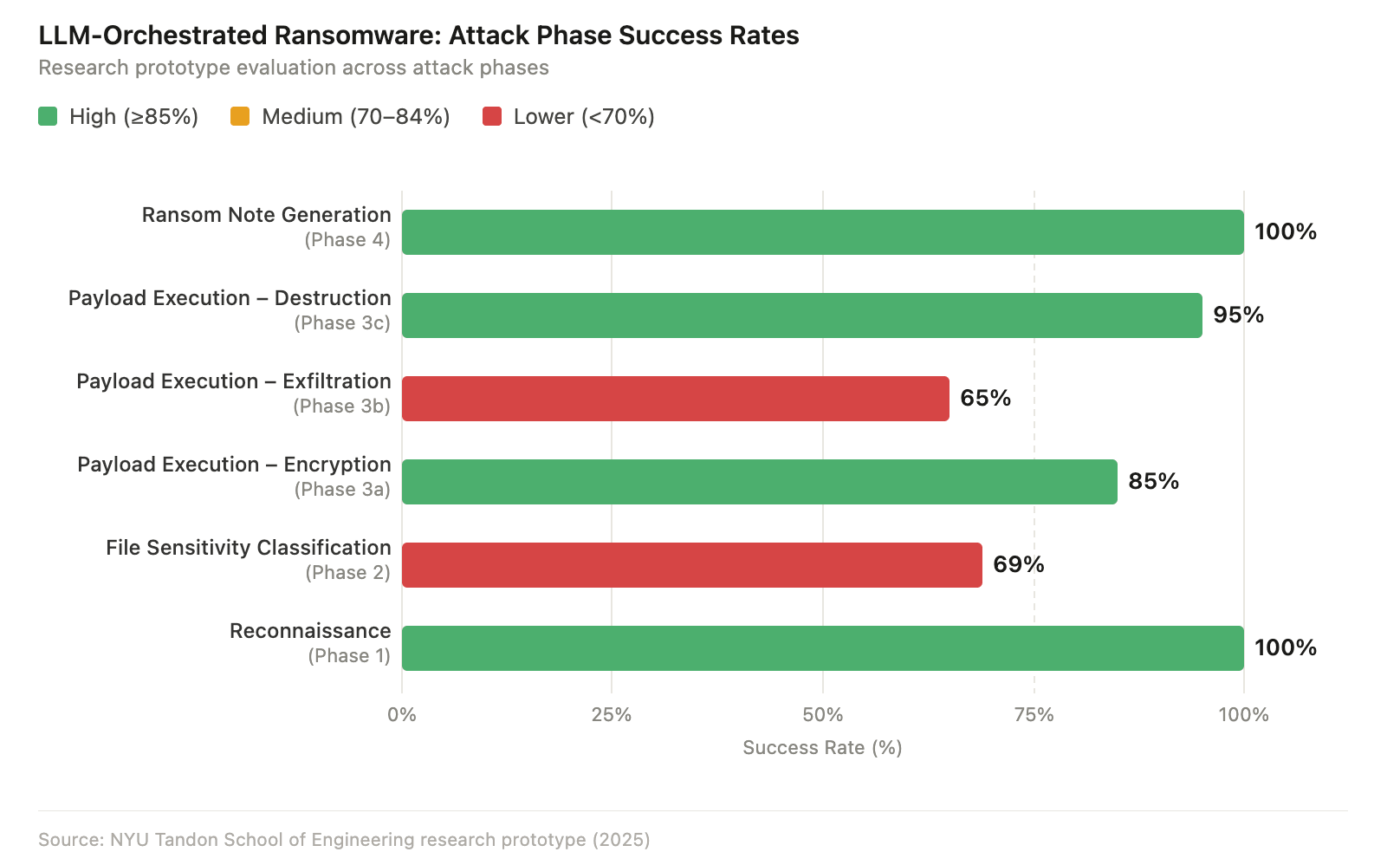
Success rates by attack phase across 30 test runs. Notably, ransom note generation (Phase 4) achieved 100% success, while exfiltration remains the most variable phase — reflecting policy friction with larger, more safety-aligned models.
Phase 4: Notification
The LLM generates a personalized ransom note that references specific files discovered on the victim’s system, named individuals, and contextual details harvested during earlier phases. This psychological targeting represents a distinct departure from the generic ransom messages of earlier ransomware generations. Both tested model sizes achieved 100% success in this phase, making personalized extortion one of the most reliably automated elements of the Ransomware 3.0 attack chain.
Polymorphism and Detection Evasion
Because malicious code is synthesized fresh at every execution, identical prompts produce different Lua code on each run. This runtime polymorphism means no two executions share the same binary footprint, file hashes, or behavioral indicators of compromise. Traditional signature-based detection is structurally ineffective against this approach. The behavioral telemetry produced is deliberately minimal: low CPU and disk I/O during reconnaissance, and network traffic patterns indistinguishable from normal HTTPS API calls.
The broader Ransomware 3.0 ecosystem also deploys dedicated EDR killer tooling. In August 2025, Sophos X-Ops revealed a highly obfuscated, kernel-level EDR-killer tool actively deployed by at least eight ransomware groups — including Blacksuit, Medusa, Qilin, RansomHub, and INC. These tools exploit legitimately signed but vulnerable Windows drivers using Bring Your Own Vulnerable Driver (BYOVD) techniques to terminate Defender, SentinelOne, Sophos, and other endpoint agents at the kernel level — often within the first 30 minutes of intrusion. The proliferation of RansomHub’s custom EDRKillShifter tool to Play, BianLian, and Medusa affiliates represents cross-group capability sharing that accelerates the adoption of these evasion techniques across the criminal ecosystem.
In real-world deployments, Ransomware 3.0 actors also exploit Living-off-the-Land (LoTL) techniques — using PowerShell, WMI, RDP, and legitimate administrative toolchains — to blend malicious activity into normal operational noise, further complicating behavioral detection.
Triple Extortion: The Multi-Vector Pressure Model
Triple extortion is the defining commercial strategy of Ransomware 3.0, operating across three simultaneous pressure vectors that collectively overwhelm victims’ response capabilities.
Layer 1: Encryption
Data is encrypted using strong asymmetric/symmetric hybrid schemes. Decryption keys are withheld pending payment. Critically, unlike Ransomware 1.0, modern encryption is applied after data exfiltration — ensuring leverage even if victims restore operations from backups. The “backup defense” that sufficed against earlier ransomware generations is structurally insufficient against this model.
Layer 2: Data Extortion
Sensitive files are exfiltrated before encryption and published — or threatened to be published — on leak sites hosted on the Dark Web. This transforms ransomware from a pure availability threat into a combined confidentiality and reputational attack. AI is now used to classify exfiltrated data by leverage value: contracts, intellectual property, HR records, and credentials are prioritized for maximum extortion potential.
Layer 3: Escalation Pressure
Attackers add further coercion through DDoS attacks against victim infrastructure, direct contact with customers and business partners, and threats of regulatory disclosure to relevant authorities such as the SEC, FCA, or data protection supervisory bodies. Some groups engage in “doxing” — releasing personal information of executives or employees to intensify psychological pressure on decision-makers. AI enhancements to this layer are significant: attackers now deploy deepfake audio and video impersonating executives in negotiation calls, and use hyper-personalized spear-phishing generated by AI to target employees identified through LinkedIn and GitHub reconnaissance.
The Industrialized RaaS Infrastructure
Ransomware 3.0 runs on a mature cybercriminal business model. RaaS platforms allow technically unskilled affiliates to rent complete attack infrastructure — ransomware builders, negotiation portals, affiliate dashboards, and customer support — in exchange for a revenue split, typically 70–80% to the affiliate and 20–30% retained by the platform operator.
Decentralized technology has made this infrastructure resistant to law enforcement action. Research has demonstrated how IPFS (InterPlanetary File System) and Ethereum smart contracts can host ransomware payloads and automate victim payment workflows in a way that is practically impossible to remove. In January 2026, security researchers documented a ransomware group using Polygon smart contracts to conceal and rotate its command-and-control infrastructure, illustrating how blockchain technology is being weaponized as anti-takedown infrastructure.
This industrialization has produced a fragmented but prolific threat landscape. According to SOCRadar’s 2026 U.S. Threat Landscape Report, Qilin, Akira, and PLAY together represent approximately 33% of ransomware activity, with dozens of smaller groups comprising the majority — a long-tail distribution that makes the ecosystem highly resilient to the disruption of any single group.
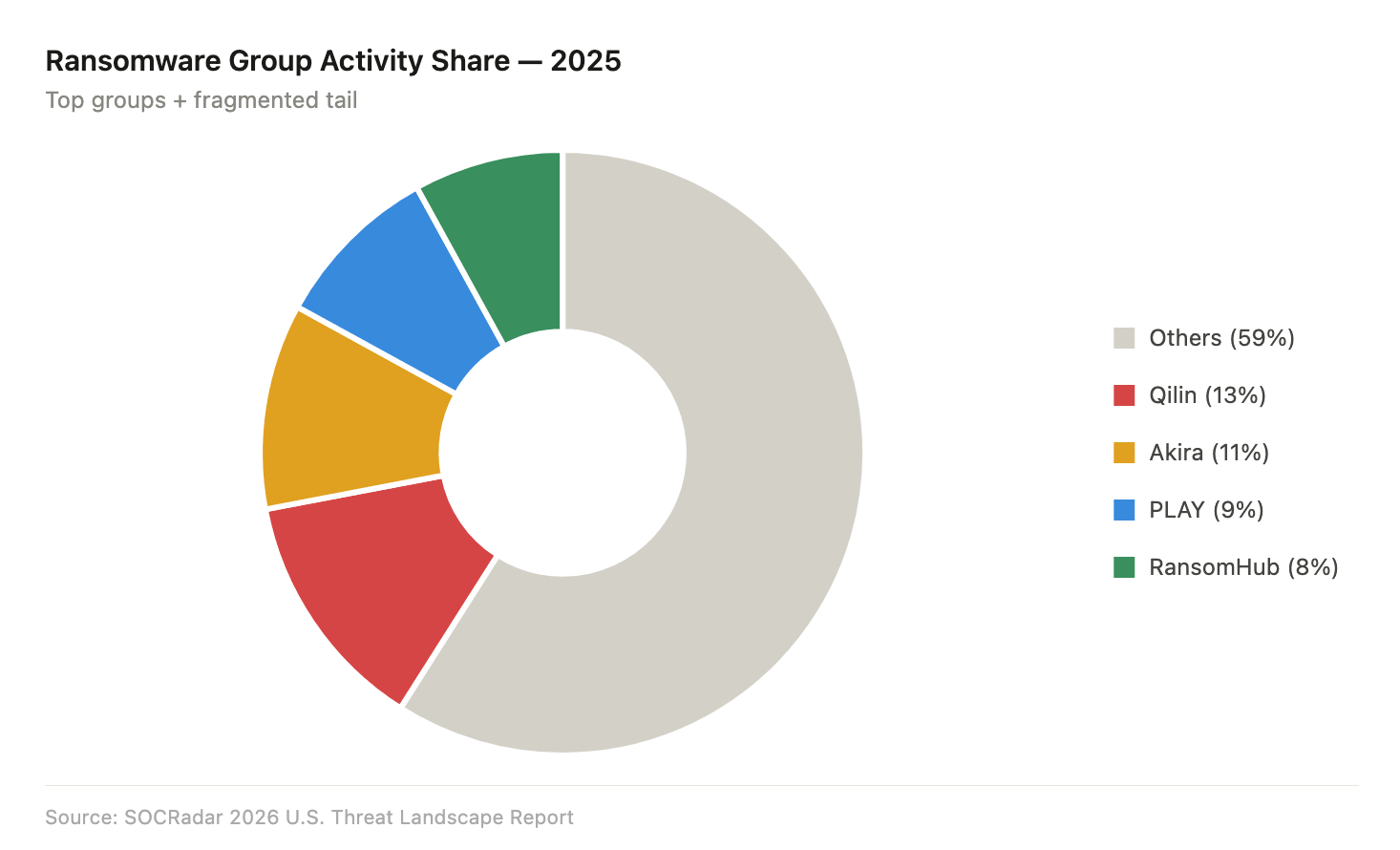
Ransomware group activity distribution, 2025. No single group dominates — the long tail of smaller operators makes ecosystem-wide disruption extremely difficult.
Supply chain attacks have emerged as one of the fastest-growing vectors within the Ransomware 3.0 landscape, with a 93% year-over-year increase in 2025 representing an unprecedented acceleration.
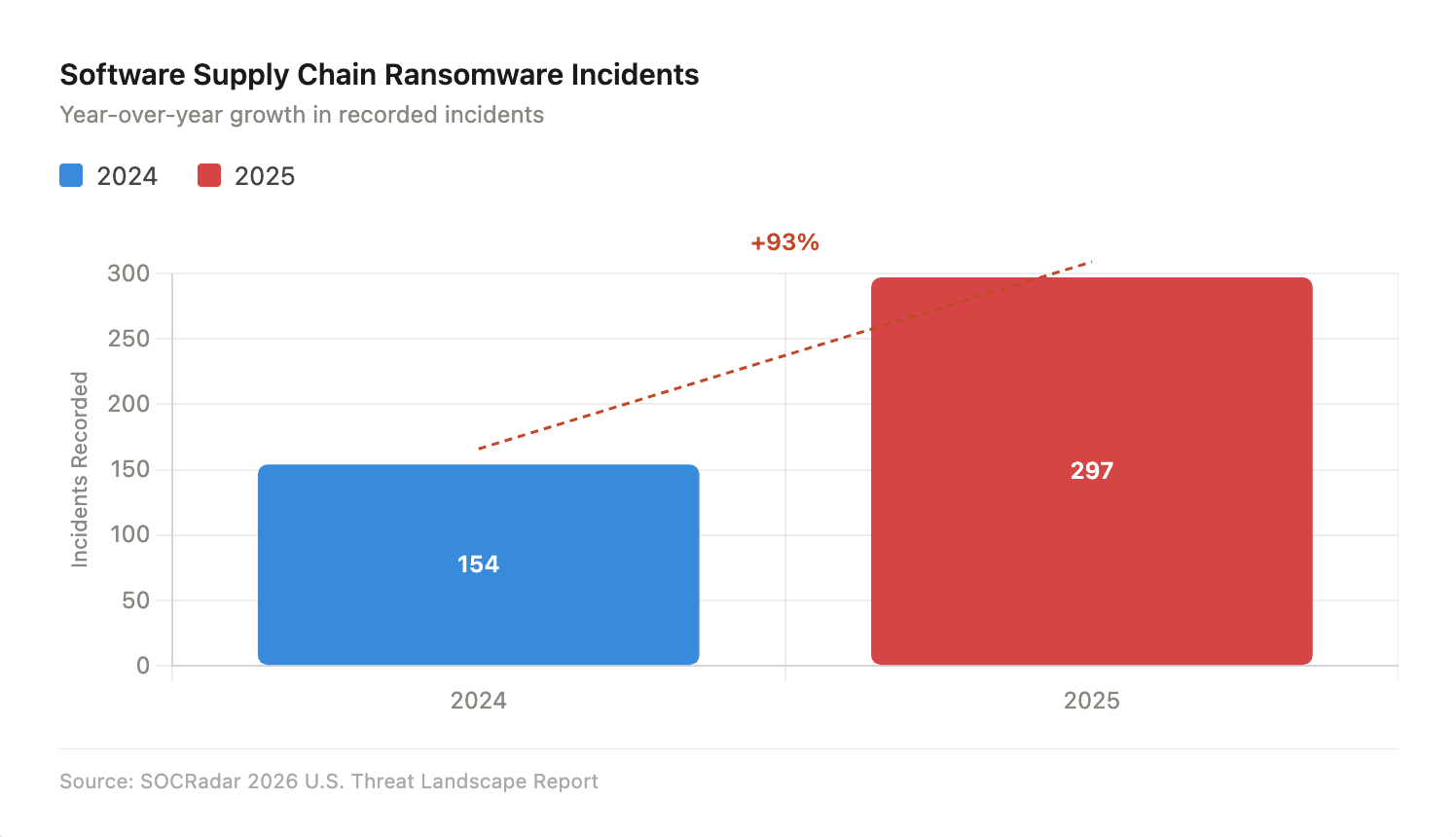
Software supply chain ransomware incidents, 2024 vs. 2025. Every industry sector was impacted by at least one software supply chain attack in 2025.
Threat Landscape: By the Numbers (2025–2026)
| Metric | Finding |
|---|---|
| Total ransomware attacks (2025) | 7,419 — a 32% increase over 2024 |
| Hardest-hit sector | Manufacturing — 56% surge in incidents |
| Supply chain incidents (2025 vs. 2024) | 297 vs. 154 — a 93% increase |
| Top 3 groups’ market share | Qilin, Akira, PLAY — approximately 33% combined |
| LockBit peak market share | ~44% of all global ransomware incidents |
| AI variant cost on Dark Web | $400–$1,200 per variant (no coding required) |
| LLM API cost per attack run | ~$0.70 at scale (NYU research prototype) |
| Ransom note generation success rate | 100% across all tested LLM configurations |
| Sectors with supply chain exposure | All industry sectors — 100% coverage in 2025 |
Attack Economics and the Democratization of Ransomware
One of the most alarming shifts in Ransomware 3.0 is the dramatic reduction in both attack cost and skill requirements. The NYU research demonstrated that a closed-loop LLM-orchestrated ransomware campaign can be executed at approximately $0.70 per run at scale — a cost barrier so low it removes the economic constraints that previously limited sophisticated attacks to well-resourced criminal organizations.
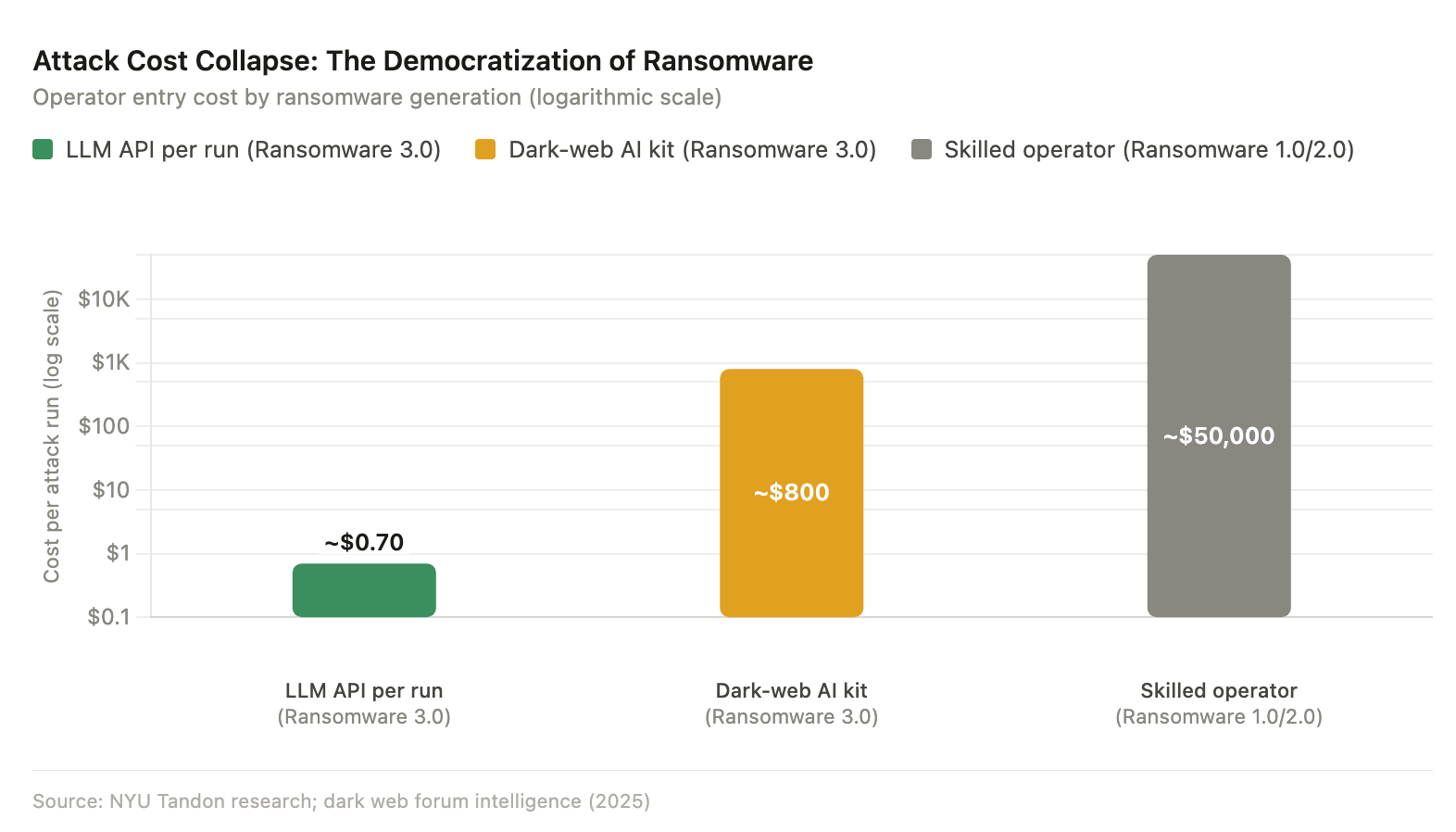
The collapse of attack economics across ransomware generations (log scale). The democratization of LLM API access has reduced the entry cost for sophisticated attacks by several orders of magnitude.
In documented 2025 cases, AI-generated ransomware variants were available on Dark Web forums for $400–$1,200 per variant, created by individuals with no advanced programming knowledge. This has structurally expanded the attacker population across three distinct categories.
Opportunistic individuals with commodity hardware and a commercial LLM API subscription now represent a credible threat. Organized cybercriminal groups continue to operate RaaS platforms at industrial scale, with the sophistication gap between operators and affiliates shrinking as AI tooling automates the most technically demanding aspects of attack construction. State-aligned actors targeting critical infrastructure for sabotage rather than financial extortion represent a third category, one for which the destructive payload path identified in the NYU research — targeting embedded industrial controllers — is particularly relevant.
Critical Evaluation: Capabilities, Limitations, and What’s Next
What Ransomware 3.0 Has Achieved
Proof-of-concept research confirms that fully autonomous, closed-loop ransomware campaigns are technically viable today. Open-source LLMs can generate functional malicious code without jailbreaking. Polymorphic payloads break traditional signature-based detection. Personalized extortion notes increase psychological pressure on victims. And EDR-killing tooling reliably neutralizes endpoint defenses before encryption begins.
Current Limitations
Larger, more safety-aligned LLMs refused extraction-related tasks 68–86% of the time in research settings, creating a tension between model capability and policy compliance that currently constrains the most capable models from full autonomous deployment in real attacks. Execution reliability also varies by environment — exfiltration payloads succeeded only 65% of the time in testing, compared to 95% for destructive payloads. Real-world deployment still requires an initial access foothold, which remains the most operationally challenging phase for attackers without human involvement.
What’s Coming: Ransomware 4.0
The threat trajectory points toward a fourth generation emerging within two to three years. Key characteristics anticipated in Ransomware 4.0 include quantum-resistant encryption that renders decryption permanently impossible even with law enforcement intervention; AI-versus-AI offensive and defensive warfare in which attack and defense capabilities co-evolve in real time; and fully autonomous malware that learns adaptively from every failed detection attempt, progressively refining its evasion across campaigns.
How SOCRadar Helps Organizations Defend Against Ransomware 3.0
Ransomware 3.0 introduces autonomous, polymorphic, and multi-vector attacks that exceed the limits of traditional reactive defenses. SOCRadar’s Extended Threat Intelligence (XTI) platform addresses this with a proactive, layered approach built for modern ransomware threats.
Ransomware and Threat Actor Intelligence
SOCRadar provides real-time tracking of ransomware groups, MITRE ATT&CK-based TTP mapping, and detailed threat actor profiles with IoCs. Its unified intelligence module prioritizes threats based on industry and geography, delivering targeted insights. The platform has helped organizations detect ransomware activity early and avoid major financial losses.
Dark Web Monitoring: Intercepting Initial Access
Many attacks begin with stolen credentials traded on the Dark Web. SOCRadar continuously monitors forums, marketplaces, and messaging platforms for exposed credentials and sensitive data. Its Identity and Access Intelligence correlates stealer logs with active threats, enabling early response before access is abused.
External Attack Surface Management (EASM)
Attackers scan internet-facing assets for weaknesses such as misconfigurations and unpatched services. SOCRadar continuously discovers and monitors these assets, identifies vulnerabilities, and prioritizes risks using real-time threat context rather than static scores.
Supply chain compromises are a growing ransomware vector. SOCRadar monitors vendor risks, detects breaches, extracts IoCs, and provides automated response workflows. This reduces the delay between vendor compromise and customer awareness.
Vulnerability Intelligence
Ransomware groups exploit known vulnerabilities for initial access. SOCRadar delivers real-time alerts on critical CVEs relevant to an organization’s stack, with context on active exploitation. As a CISA CNA, it also contributes directly to CVE identification and disclosure.
Agentic Threat Intelligence: Fighting AI with AI
SOCRadar uses autonomous AI agents to detect and respond to threats with minimal human input. These agents handle areas like phishing, credential leaks, and brand abuse, while integrating with SOAR platforms to automate investigation and response.
Strategic Recommendations for Organizations
The Ransomware 3.0 threat demands a defense posture that mirrors the attacker’s architecture: proactive, intelligence-led, and automated. The following priorities are essential for organizations seeking to meaningfully reduce their exposure.
Zero Trust Architecture
Strict identity verification for every user and device, combined with micro-segmentation to contain lateral movement, directly counters Ransomware 3.0’s reliance on credential abuse and internal pivoting. Organizations that have not yet implemented zero trust principles are structurally exposed to the initial access and lateral movement phases that precede encryption.
AI-Aware Behavioral Detection
Signature-based detection is ineffective against polymorphic, LLM-synthesized payloads. Investment in behavioral monitoring tools capable of detecting anomalous LLM API calls, in-memory script execution, sensitive file access patterns, and rapid automation is now essential — not optional.
Immutable Backups
With Ransomware 3.0 prioritizing backup destruction as an early attack objective, immutable snapshot technology that cannot be modified or deleted by compromised credentials is a foundational requirement. Traditional backup strategies that rely on network-accessible repositories are insufficient.
Credential Hygiene and Continuous Dark Web Monitoring
Infostealer logs represent the most prevalent initial access vector in the current threat landscape. Organizations must monitor Dark Web exposure continuously, enforce multi-factor authentication universally, and treat credential compromise notifications as security incidents requiring immediate response rather than routine IT events.
Supply Chain Visibility
Third-party vendor compromise is now the fastest-growing ransomware vector. Continuous monitoring of the supply chain — with automated alerting, IoC extraction, and pre-built incident response playbooks — is mandatory for any organization with meaningful third-party digital dependencies.
Incident Response for Triple Extortion
Incident response plans built around encryption recovery are insufficient for the Ransomware 3.0 threat model. Plans must extend to include data-leak legal response (including regulatory notification obligations), DDoS countermeasures, and stakeholder communication protocols for customer and partner notification scenarios — all of which may be triggered simultaneously in a triple extortion campaign.
The landscape is unambiguous, Ransomware 3.0 is not a future concern, it is the operational reality of 2025 and 2026. Organizations that treat it as a conventional IT problem will remain systemically vulnerable. Those that invest in intelligence-led, AI-augmented, proactively threat-informed defenses stand the best chance of detection, disruption, and recovery before a ransomware campaign completes its autonomous lifecycle.