How MSSPs Can Turn Supply Chain Security into New Revenue Streams
Supply chain attacks have become the fastest-growing threat vector in enterprise security. Here is what the data shows, and how MSSPs can build a profitable practice around it.
The Attack Surface Your Clients Cannot See
Every enterprise runs on third parties. Cloud platforms, SaaS tools, logistics vendors, payment processors, and IT outsourcers. Each one is a potential entry point into your client’s environment. And most of those vendors never get a security review.
The scale of the problem is hard to ignore. Last year, supply chain breaches doubled year over year, accounting for roughly 30% of all data breaches. A single compromise in a shared vendor can hit dozens or hundreds of downstream organizations at once.
The cost picture is just as stark. Supply chain attacks cost 17 times more to remediate than direct first-party breaches. For large enterprises, losses from major incidents reached an estimated $20 to $80 billion in just 15 months. And the blast radius keeps growing. A single compromised SaaS integration last year hit over 700 organizations in one campaign, including some of the most recognized names in cybersecurity. No vulnerability in those companies. Just one trusted vendor with a stolen token.
This is the core problem for your clients. They are exposed through relationships they trust but never monitor. The attack surface is invisible to them, which is exactly where you come in.
By the numbers:
- 30% of all data breaches last year linked to third parties or supply chain issues
- 2x year-over-year increase in supply chain breach frequency
- 17x more costly to remediate than a direct first-party breach
- 700+ organizations hit in a single SaaS supply chain attack last year
- 60% of underground forum posts directly reference cybersecurity and CTI companies
- 25% of those posts are focused specifically on bypass and evasion techniques
Why This Moment Is Different for MSSPs
Supply chain risk is not a new concept. What has changed is the regulatory pressure forcing enterprises to act on it, and the volume of real incidents making boardrooms pay attention.
The SEC now requires public companies to disclose material cyber incidents, creating clear regulatory accountability. Frameworks like NIST 800-161 define comprehensive supply chain risk management practices, and CISA provides detailed guidance for critical infrastructure sectors. While not all of these are binding on their own, they collectively shape regulatory expectations, contractual obligations, and audit standards, meaning organizations must demonstrate due diligence or face legal, financial, and reputational consequences.
Most enterprises do not have the internal resources, tooling, or expertise to meet these requirements on their own. They need a partner who can provide continuous visibility into their supplier ecosystem, generate audit-ready reports, and flag risks before they become incidents. That is a service description, not a product.
What the Underground Market Tells Us About Your Clients’ Risk
We mapped activity across elite technical forums, data leak platforms, ransomware extortion blogs, and illicit Telegram channels. The picture it paints is not abstract. It is specific and operational.
Participants in these communities operate like a structured supply chain. Initial access brokers sell VPN, RDP, and cloud access to corporate environments. Malware developers test loaders and stealers against common security stacks. Ransomware affiliates seek verified access for deployment. Data brokers monetize stolen credentials. Each actor plays a specialized role, and transactions run on structured trust systems, with ratings, escrow services, and proof of access requirements, much like a legitimate marketplace.
What this means for your clients is that their exposure is visible before an attack begins. Stolen credentials and advertised access appear in underground markets days before incidents. A compromised Accenture supply chain reportedly exposed more than 32,000 employees. Alleged breaches at Deloitte, Capgemini, and KPMG circulated in leak forums, with claimed data including source code, internal credentials, and operational security data.
Supply chain driven monitoring across Dark Web forums, leak platforms, ransomware blogs, and illicit Telegram channels, as delivered through SOCRadar Supply Chain Intelligence, extends visibility well beyond your direct perimeter. By continuously tracking third party exposure, tied to your ecosystem, it allows you to detect risk signals earlier, often days before an attack is executed.
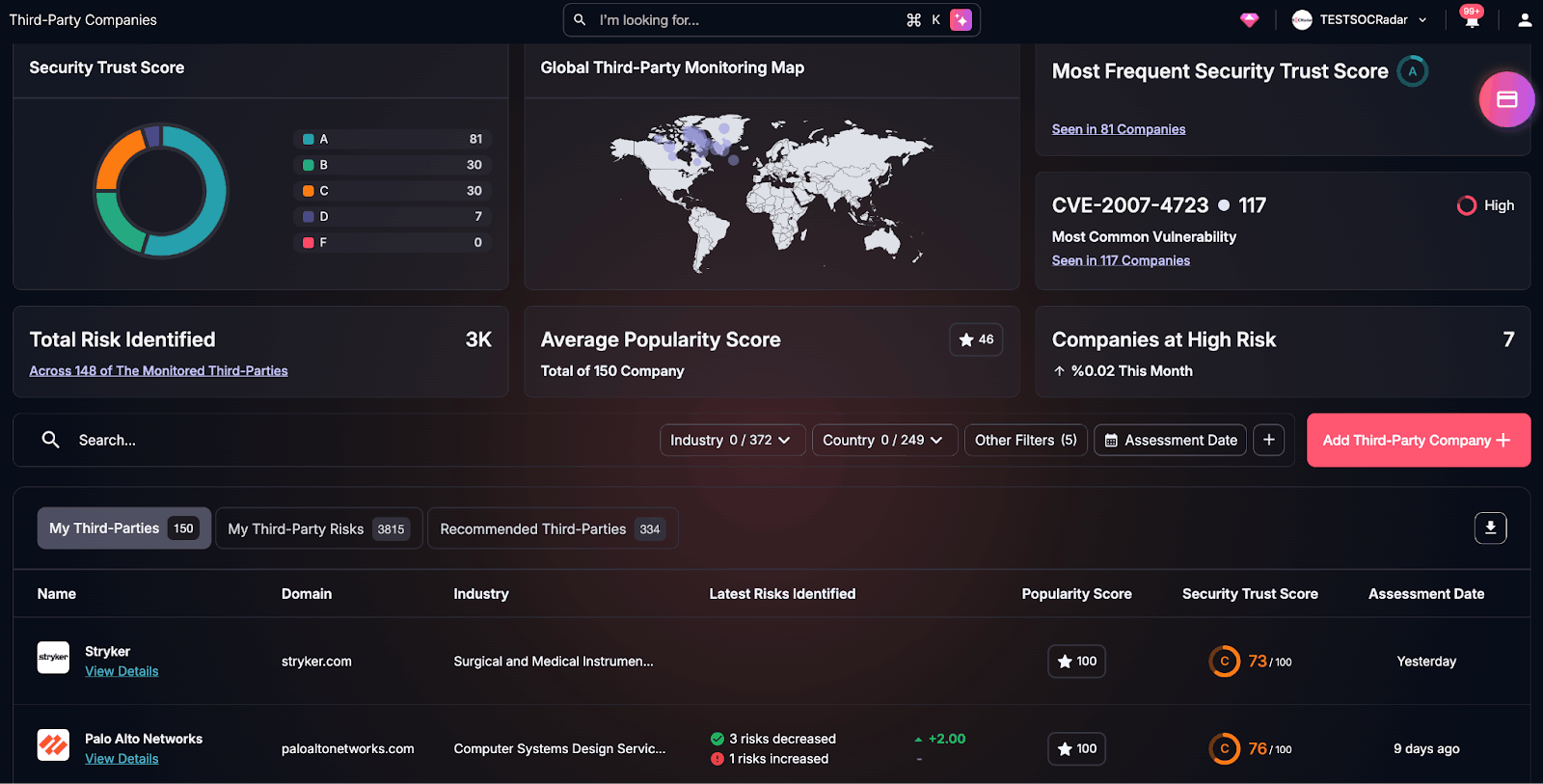
SOCRadar Supply Chain Intelligence, 3rd Party Companies
These are the intelligence gap that a well-structured MSSP service closes. Your clients do not have visibility into these channels. You can.
What a Supply Chain Security Service Actually Looks Like
You do not have to build this capability from scratch. The Supply Chain Intelligence module gives MSSPs the data infrastructure to deliver this as a managed service, backed by a database of over 50 million monitored companies.
Continuous vendor risk monitoring
Each vendor in your client’s supply chain gets a dynamic risk score based on 133 technical assessment checkpoints spanning attack surface, Dark Web exposure, and threat intelligence signals. Risk scores update continuously, not once a year at audit time.
Dark Web and credential exposure detection
If a supplier has credentials circulating on Dark Web forums or data appearing in stealer logs, that is a risk to your client too. Dark web monitoring surfaces these exposures across the entire supply chain, not just for the primary organization. Given that stolen credentials and access listings appear in underground markets days before incidents, this is the early warning layer that prevents downstream compromise.
Tiered supplier prioritization
Not all vendors carry equal risk. Suppliers are grouped into tiers based on business criticality with separate alert thresholds for each tier. Your team focuses effort where exposure is highest. Clients understand the logic and trust the prioritization.
Compliance-mapped reporting
Findings map across 23 frameworks including NIST, ISO/IEC, and CIS. When your client needs to demonstrate supply chain due diligence for an audit or a regulatory review, you generate a structured report in minutes rather than hours.
Co-branded external threat assessment reports
The platform supports fully co-branded, client-facing reports covering threat actors, attack vectors, vulnerability exposure, and supply chain risk. MSSPs use these during the sales process to demonstrate risk, during onboarding to establish a baseline, and in regular reviews to show progress. More on how this works in practice is in this guide to scaling with threat intelligence. The layout is executive-ready and built for board-level presentations.
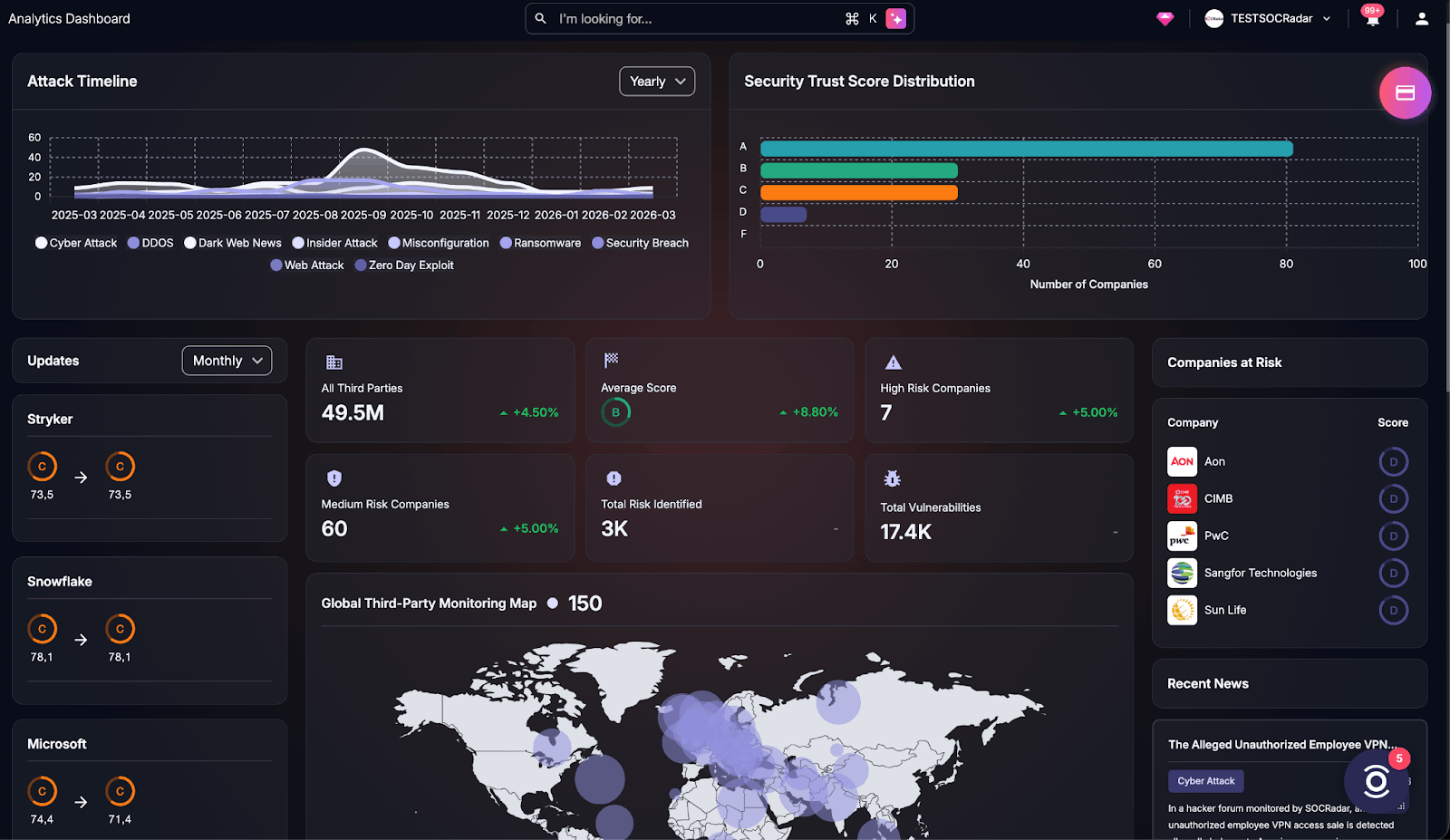
SOCRadar Supply Chain Intelligence, Analytics Dashboard
What the Partner Program Brings
The MSSP program is built around a multi-tenant architecture that lets you manage all client environments from a single console without switching between portals or duplicating workflows.
What is included:
- Multi-tenant management console with role-based access and client-level dashboards
- AI Agents that automate threat triage, enrichment, and alert correlation across client tenants, reducing analyst workload without adding headcount
- AI Agent and Automation Training, platform-agnostic, so your SOC team can build AI-powered workflows regardless of your existing stack
- Modular pricing so you pay for what you use and scale as your client base grows
- Co-brandable reports and ready-to-deploy marketing kits built for MSSP lead generation
- Joint go-to-market planning and business development support
For most MSSPs, the constraint is not demand. It is capacity. AI-driven automation addresses the capacity problem without growing the cost base, which is exactly the operational shift the threat landscape demands.
The Window Is Open Now
Most MSSPs offer threat detection, SIEM management, and incident response. Those are table stakes. Supply chain security is not yet fairly utilized, and demand is rising fast driven by both the volume of real incidents and the weight of new compliance requirements.
MSSPs who build this capability now will have a real differentiator for the next two to three years. They will be positioned for enterprise and mid-market clients who are feeling compliance pressure most acutely. And they will have recurring revenue streams that do not depend on incident volume to generate value.
Next Step
Join the network of MSSPs who are building intelligence-led supply chain security practices. The partner program provides the platform, training, co-marketing support, and go-to-market collaboration to help you get there fast.
Further Reading:

