Financial Crime in 2026: How Organized Threat Ecosystems Are Outsmarting AML Controls
Financial crime has changed dramatically over the last few years. Fraud is no longer driven primarily by isolated attackers or opportunistic scams. Instead, it has evolved into a coordinated ecosystem where identity theft, account takeover, money laundering, and infrastructure services operate as interconnected criminal markets, functioning with the efficiency and specialization of a legitimate industry.
Today’s financial fraud environment combines stolen credentials, automated tools, AI-assisted identity generation, and distributed money mule networks. These operations allow threat actors to move funds quickly, bypass monitoring systems, and exploit structural gaps between financial institutions. The challenge for banks, fintech platforms, and financial service providers is no longer detecting suspicious transactions in isolation. The real challenge lies in identifying coordinated activity that spans multiple systems, institutions, and digital channels.
The Rise of an Organized Financial Crime Ecosystem
Modern financial fraud follows a repeatable cycle. Criminal actors have structured their operations around four interconnected phases that allow different groups to specialize at each stage, making the overall ecosystem far more resilient and difficult to disrupt than traditional fraud models.
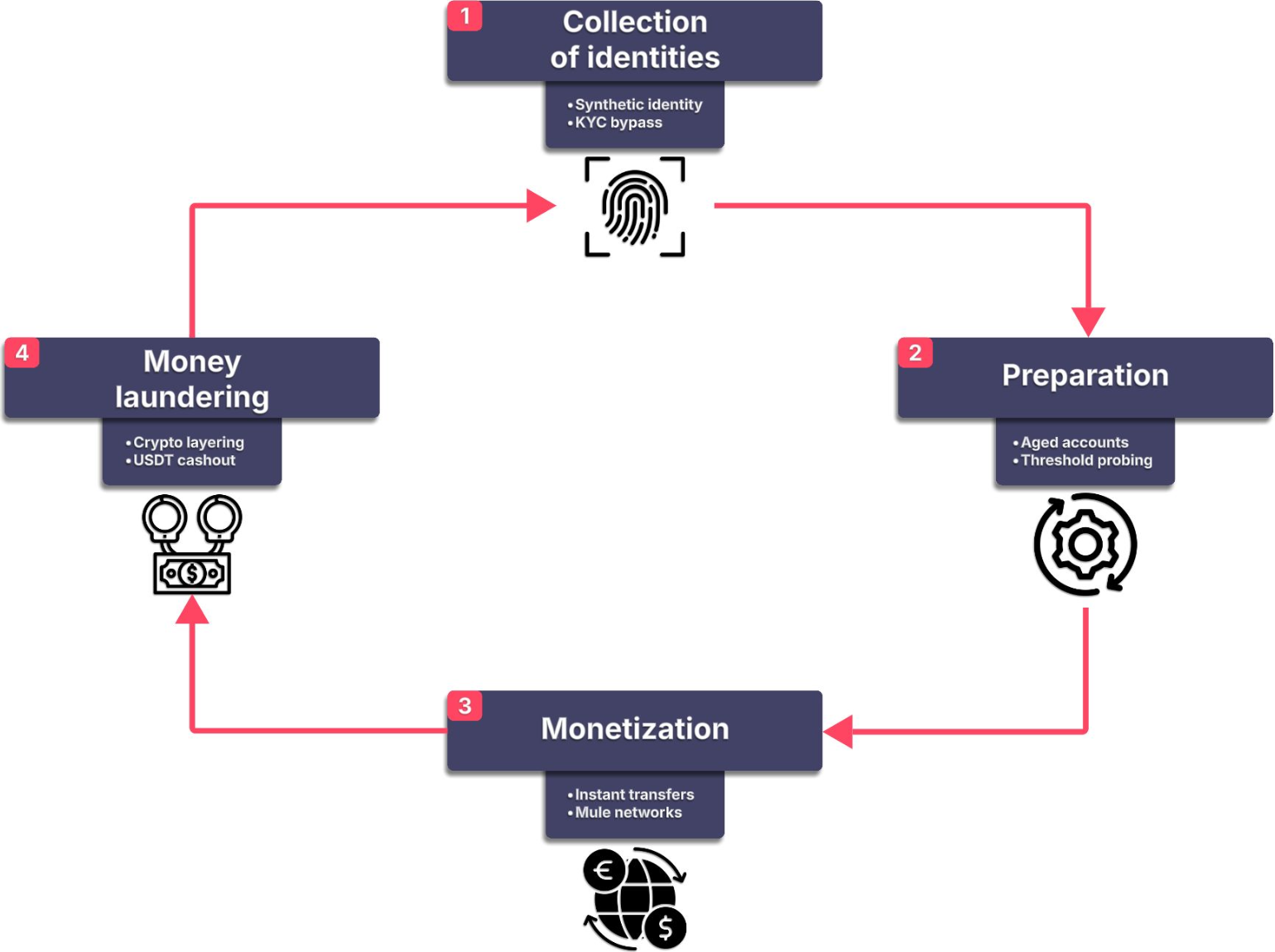
Example lifecycle of modern financial crime operations, where identity theft, account preparation, fraud execution, and laundering operate as an interconnected ecosystem.
- Collection of Identities: Threat actors harvest personal data through data breaches, stealer malware, and phishing campaigns. Synthetic identity creation and KYC bypass tools are also used to fabricate or augment stolen personas.
- Account Preparation: Aged accounts are acquired and “warmed”; built up with legitimate-looking transaction histories over weeks or months. Threshold probing tests alert limits before fraudulent activity begins.
- Monetization: Funds are extracted through instant payment rails and distributed across mule networks. High transaction velocity and irreversible transfers reduce the window for detection and recovery.
- Money Laundering: Proceeds are layered through crypto ecosystems, using mixers, chain-hopping, and stablecoins, before final cash-out via OTC brokers or shell companies and re-integration into the fiat banking system.
Because these roles are distributed, the ecosystem is more resilient than traditional fraud models. A law enforcement action against one node – say, a credential marketplace – does not disrupt the entire chain. Other actors simply adapt, and the cycle continues.
Instant Payment Rails: The Fraud Response Window Has Collapsed
The rapid adoption of instant payment systems has fundamentally changed the fraud detection landscape. Transactions now settle within seconds, leaving little room for manual review, delayed monitoring, or batch-based screening systems that were the backbone of AML compliance for decades.
The EU Instant Payments Regulation, in force since October 2025, mandates settlement in under 10 seconds, 24 hours a day, 365 days a year. The European Banking Authority has warned that fraud risk in instant payment environments is ten times higher than in traditional transfer channels. In the United States, FedNow adoption is projected to reach 80% of financial institutions by the end of 2026, making instant rails the dominant transaction channel, and the dominant fraud vector, in the near future.

Key figures illustrating the shrinking fraud response window in today’s instant payment environment.
Adversaries have fully adapted to this environment. They now execute complete cycles of fund fragmentation, movement, and consolidation before any batch-processing system records the first transaction. Detection models calibrated on transaction value or individual account frequency are becoming operationally obsolete. The effective intervention window is measured in seconds, not hours; and most smaller financial institutions are simply not equipped for that reality.
AML Evasion: From Technique to Industrialized Service
Criminal groups are not bypassing AML controls by luck. They are studying how detection systems behave and systematically adapting. What was once a technique has become a service. AML evasion is now sold as a product in underground marketplaces, accessible even to non-technical actors.
Threshold Probing
AML systems are rarely attacked directly; they are probed. Threat actors execute incremental test transactions to map the precise alert thresholds of a target institution. Once those limits are understood, fraudulent activity is structured to remain permanently below them. The alert threshold stops being a control and becomes an operational guideline for the attacker.
Behavioral Evasion
AML behavioral models detect deviations from a customer’s typical activity pattern. Sophisticated actors counter this by constructing legitimate-looking profiles before initiating fraud; building clean transactional histories over weeks or months, mimicking genuine customer behavior, and deliberately generating alert noise to cause fatigue in compliance teams so that genuine signals go undetected.
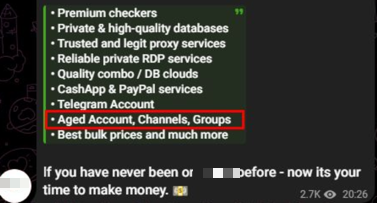
Telegram post offering aged accounts and tools used for fraud and evasion.
Transaction Fragmentation
Structuring has evolved through automation. It is no longer a manual process; it is programmatic and coordinated. Script-driven automation executes hundreds of microtransactions across multiple institutions simultaneously. Because no single institution has visibility over the full pattern, cross-institution fragmentation creates blind spots that organized crime actively exploits. A single bank may see nothing unusual. Across the network, a large laundering operation is fully underway.
Mule Network Coordination Across Institutions
Money mule operations have expanded from localized groups into distributed infrastructure running simultaneously across multiple financial institutions. Networks are organized hierarchically: first-level mules receive funds from fraudulent transactions, second-level mules transfer those funds across institutions, and third-level actors execute the final cash-out. Recruitment has been industrialized through social media platforms, such as Telegram, TikTok, and Discord, where mule roles are advertised as flexible remote work opportunities. Because activity is fragmented across many banks, no single institution sees the total volume needed to raise a flag.
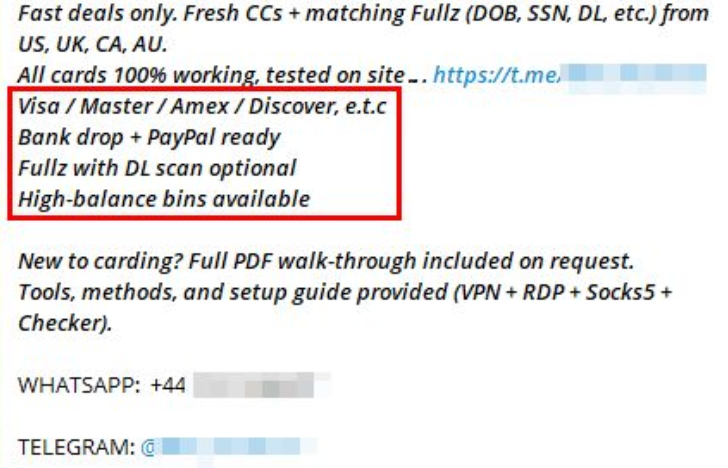
Telegram advertisement offering stolen card data, bank drops, and fraud-ready financial accounts.
Synthetic Identities and AI-Automated Fraud
Synthetic identity fraud has evolved from a niche technique into a systemic threat, accelerated by generative AI tools that can adapt in real time against verification systems. In 2025, one in five first-party fraud cases involved synthetic identities. AI-assisted document forgery doubled in a single year. By 2026, autonomous agent fleets are projected to saturate manual review processes at scale; a structural asymmetry, since criminal actors can deploy AI without any of the regulatory or explainability constraints that financial institutions face.
Two primary approaches are now in common use:
- Fully Synthetic Identity Fraud: Attackers generate entirely fabricated personas using AI-produced personal data, realistic portrait images, and forged identity documents, creating individuals who do not exist but can pass standard verification flows.
- Hybrid (Fullz-Based) Identity Fraud: Real stolen personal data from previous breaches is combined with AI-generated biometric material. Because the underlying PII is authentic, hybrid identities can often pass the cross-reference checks used by most financial institutions, making them significantly harder to detect than purely synthetic identities.
Deepfake-as-a-Service (DaaS) platforms have made these capabilities commercially available to non-technical criminals. Modern toolsets offer AI persona generation, biometric manipulation, KYC video bypass (AI-generated video mimicking real-time human movement during verification calls), and delivery via virtual cameras and mobile emulators injected directly into banking app verification flows. Notably, threat actors have shifted their preference toward authentic data over purely synthetic fabrications, recognizing that modern detection systems more easily flag information that fails cross-referencing checks.
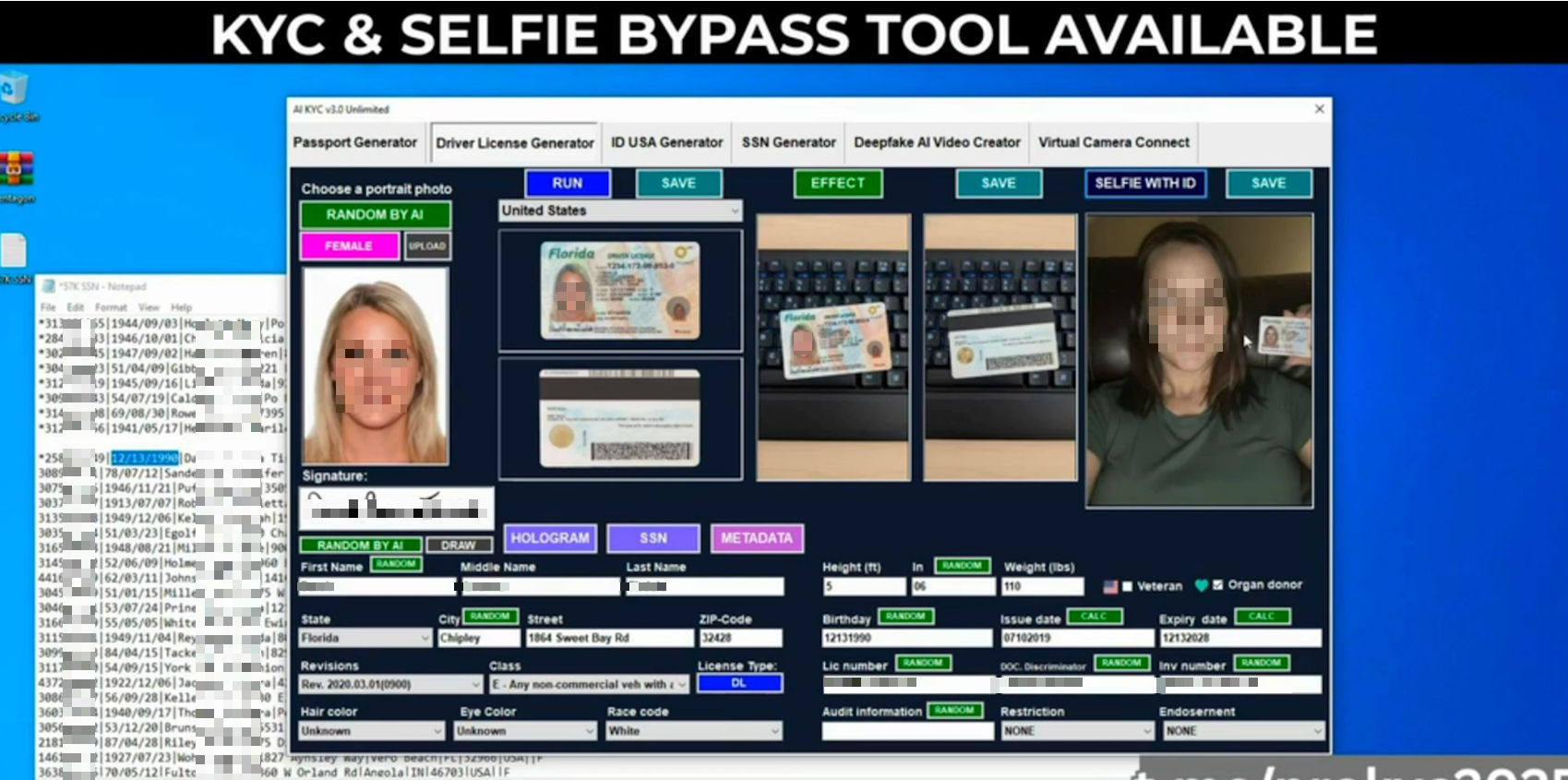
Example of a DaaS tool designed to generate identities and bypass KYC and selfie verification processes.
Telegram-based advertisement for a KYC bypass tool, highlighting targeted financial institutions and platforms.
Cryptocurrency and Modern Money Laundering
Cryptocurrency has become a cornerstone of modern laundering operations, not as an emerging channel, but as a mature, preferred infrastructure. In 2025, illicit addresses received approximately $154 billion in crypto assets, a 162% increase year-over-year. The composition of illicit crypto flows has also shifted dramatically: stablecoins now represent 84% of total illicit transaction volume, compared to just 7% for Bitcoin. Five years ago, that ratio was reversed.
USDT has consolidated as the dominant layering instrument due to its price stability, liquidity, and cross-border usability, making it ideal for moving value without exposure to cryptocurrency volatility during the laundering process.
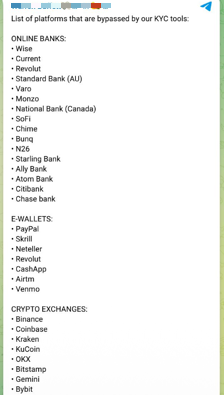
Modern cryptocurrency laundering follows a three-phase structure: placement, layering, and integration.
Smaller financial institutions lacking crypto-fiat transaction monitoring are particularly exposed. A regional bank or credit union without on-chain detection capability effectively acts as an open entry point for funds completing their layering cycle in blockchain before integrating into fiat, and the bank may have no visibility into the origin of those funds at all.
Credential Theft, Account Takeover, and Brand Abuse
Compromised credentials remain among the most valuable commodities in the underground economy. Threat actors gather them from stealer logs, phishing campaigns, data breaches, and credential-stuffing operations, then resell or reuse them long after the initial compromise. Credentials are sold, resold, and leaked via combolists and hacker forums, extending their operational lifespan well beyond a single breach event.
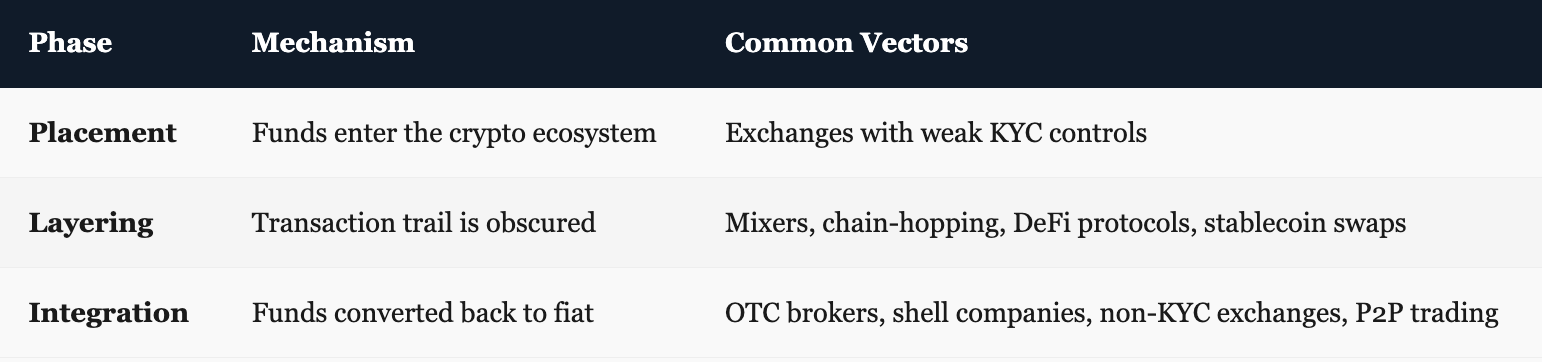
A stolen username and password may seem minor in isolation. In the hands of an organized actor, it can become the starting point for account takeover, internal reconnaissance, fraudulent transfers, or even ransomware-related access to corporate networks. Initial Access Brokers (IABs) specialize in establishing footholds inside target organizations, then selling that access to ransomware groups and fraud syndicates, who leverage it to harvest internal customer data, fuel account takeover operations, and study institution-specific detection logic to make future AML bypasses progressively more effective.
Underground marketplaces frequently sell stolen credentials, banking logs, and personal data used in financial fraud operations.
Brand Abuse as a Fraud Enabler
Fraudsters build infrastructure that mimics legitimate financial brands in order to steal trust before they steal money. This infrastructure includes lookalike login pages designed for credential harvesting, fake mobile applications distributed through unofficial app stores, impersonation accounts and paid advertisements on social media platforms, and lookalike domains using patterns across multiple TLDs to mimic mobile login flows. Because this infrastructure can be recreated quickly across new domains, platforms, and app stores, the exposure is not limited to a single phishing page; it is an ongoing, scalable campaign that requires continuous monitoring and fast takedown response to contain.
Example of phishing infrastructure used to mimic legitimate financial login portals and harvest user credentials.
The Weakest Link: Why Smaller Institutions Bear the Greatest Risk
Large financial institutions typically maintain advanced compliance teams, mature monitoring infrastructure, and significant detection budgets. Smaller institutions (regional banks, credit unions, and community financial organizations) operate with more limited resources and often rely on legacy systems that were not designed for today’s real-time fraud environment. This structural asymmetry is not an incidental vulnerability. Organized criminal groups actively exploit it.
Criminals prioritize institutions with permissive alert thresholds and low manual review capacity. A credit union with basic monitoring is the ideal entry point for a mule network needing clean accounts. Cross-institution fragmentation exploits the absence of shared visibility among smaller institutions; and because modern laundering schemes frequently span multiple organizations, a single compromised institution can expose detection patterns that affect the entire network it is connected to.
Strategic Risk Statements
- AML evasion has ceased to be a technique; it is now a service offered within fraud marketplaces.
- Mule networks operate as distributed infrastructure specifically designed to fragment the visibility of monitoring systems.
- Static rule-based systems cannot match the speed or adaptability of attackers deploying AI without regulatory constraints.
- False positive saturation is not merely an operational inconvenience; it is a deliberate evasion tactic.
- A single compromised smaller institution can expose detection patterns across the entire network it belongs to.
For platforms that serve regional banks and credit unions, the risk is not only defined by direct organizational exposure. It is equally defined by the security posture of the weakest client in the ecosystem. A compromised regional bank is not just a client at risk; it is an entry vector for the entire network.
The Strategic Outlook: Simultaneous Acceleration Across Multiple Dimensions
The threat horizon for 2026 does not point to gradual evolution. It points to simultaneous acceleration across automation, artificial intelligence, and cross-institution coordination. Most criminal actors engaged in financial fraud are already using AI, and those who are not will integrate it into their operations in the near term, making it one of the primary risk multipliers for any institution that fails to adapt.
AI-Powered Fraud
AI systems are moving from pilot phase to core AML defense across major institutions. But the same shift is occurring on the adversarial side, and criminal actors operate without regulatory constraints, explainability requirements, or audit obligations. Adversarial autonomous agents capable of adapting in real time to detection systems represent the next frontier of financial crime. For smaller institutions still operating with legacy rule-based monitoring, this is not a future strategic challenge. It is an active capability gap today.
Multiplatform Money Laundering
Institutions without crypto-fiat monitoring capability are becoming preferred entry points for the integration phase of laundering schemes. Blockchain forensics capabilities – real-time wallet cluster monitoring and transaction flow analysis – remain concentrated in large institutions, while most regional banks and credit unions lack access entirely. As a result, the weakest client in any AML network defines the exposure of the entire network.
Convergence of Compliance Functions
Large institutions are breaking internal silos, aligning AML, sanctions, fraud detection, and cybersecurity into integrated risk functions. Smaller institutions continue operating in silos, and organized crime actively exploits this asymmetry. The convergence of KYC, AML, fraud, and sanctions into unified cross-functional compliance is rapidly becoming the new industry standard. Institutions and the vendors serving them that fall short of this standard face growing exposure as criminal actors refine their targeting of the weakest link.
The Path Forward
Financial crime is accelerating faster than traditional monitoring systems can adapt. Static rules and delayed analysis were designed for a slower threat landscape, and they are increasingly ineffective against attackers using automated tools, AI-assisted identity fraud, distributed mule networks, and cross-institution fragmentation strategies.
The institutions best positioned to close this gap are those moving toward connected, intelligence-driven detection capabilities. This means shifting from reactive transaction monitoring to proactive threat intelligence; identifying fraud before it enters the institution rather than flagging it after the transfer has settled.
Effective modern detection requires a combination of real-time transaction monitoring that can operate within the settlement window of instant payment rails; cross-channel fraud intelligence that connects patterns across accounts, devices, and institutions; integrated AML and cybersecurity detection that eliminates siloed visibility; and behavior-based anomaly detection that can distinguish legitimate customers from adversaries who have deliberately constructed legitimate-looking profiles.
Beyond internal monitoring, visibility into the external environments where fraud operations begin is equally critical. Early indicators of attack – credential exposure, phishing infrastructure deployment, impersonation campaigns, initial access sales – surface in underground channels before they are operationalized against a target. Organizations that monitor those channels gain the early warning time needed to act before damage occurs.
Stay Ahead of Financial Threats with SOCRadar
In addition to strengthening internal monitoring systems, organizations benefit from visibility into the external environments where fraud operations often begin. SOCRadar provides Cyber Threat Intelligence, Dark Web Monitoring, and Brand Protection, helping financial institutions detect exposed credentials, phishing infrastructure, and impersonation campaigns targeting their employees and customers before they are weaponized.
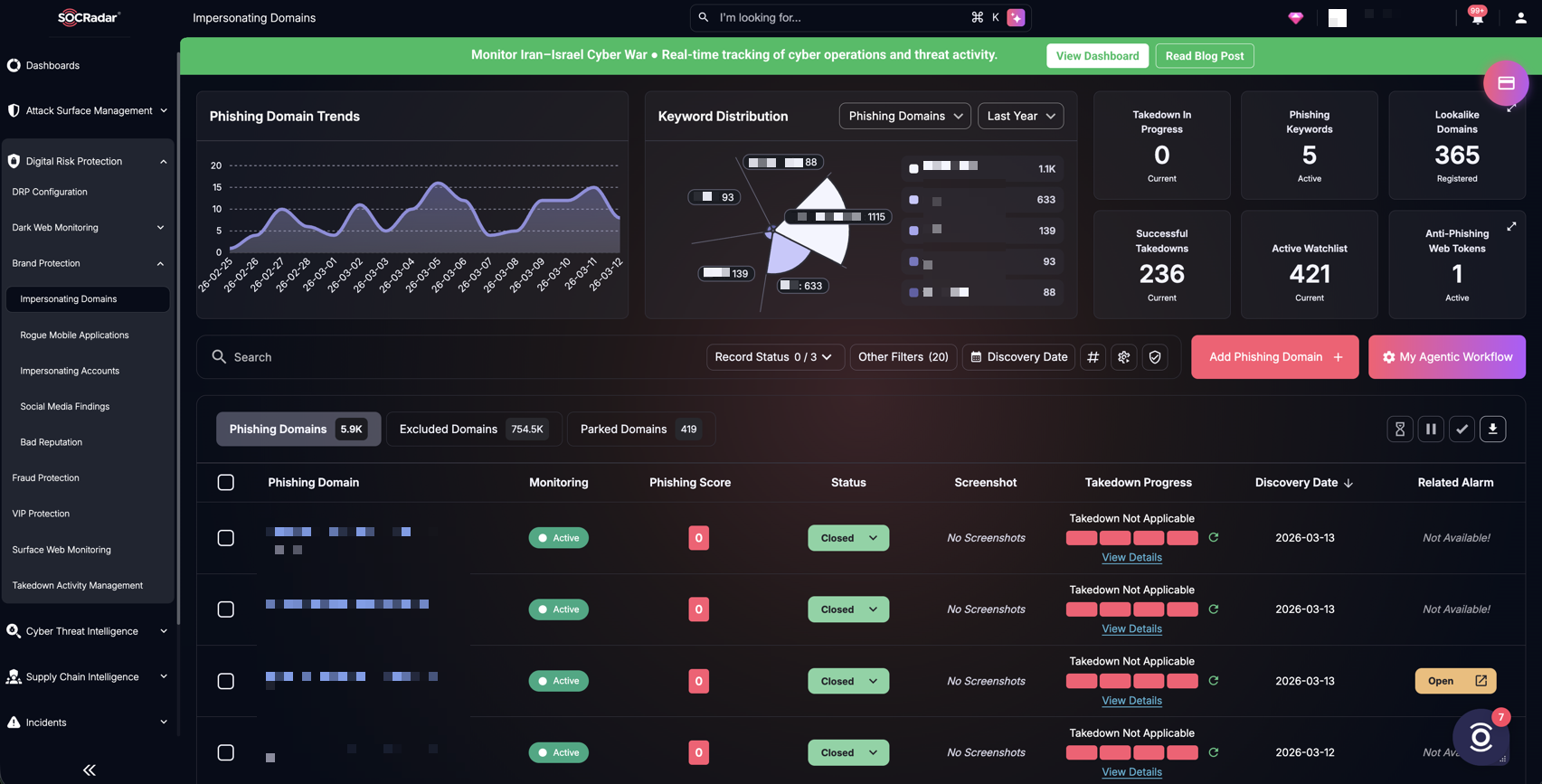
SOCRadar’s Brand Protection, Impersonating Domains
By combining internal detection with external threat intelligence, financial institutions can identify coordinated fraud activity earlier and reduce the risk of large-scale financial losses.