Dark Web Profile: DieNet
Every kinetic spike in the confrontation is now mirrored by a surge of cyber activity. In this environment, DieNet has emerged as the single most prolific disruptive force on the pro-Iranian side.
First announced on Telegram in March 2025, the group claimed over 60 DDoS attacks in its opening months. By early 2026, as the U.S.-Israeli campaign against Iran escalated, DieNet recorded 59 distinct attack claims in just two days (March 2-3, 2026), topping a field of 15 pro-Iranian and anti-Israel groups and accounting for a major share of 149 hacktivist DDoS claims across 110 organizations in 16 countries. Its rapid rise illustrates a defining trend: the commoditization of DDoS-as-a-service infrastructure now allows ideologically motivated actors to launch high-volume campaigns overnight, without building their own botnets.
Who Is DieNet?
DieNet first appeared on March 7, 2025, when it announced its presence via a Telegram channel with an opening strike claimed against Meta.ai in the United States. This was both a technical exercise and a symbolic declaration of intent, signaling the group’s focus on high-visibility Western targets from day one.
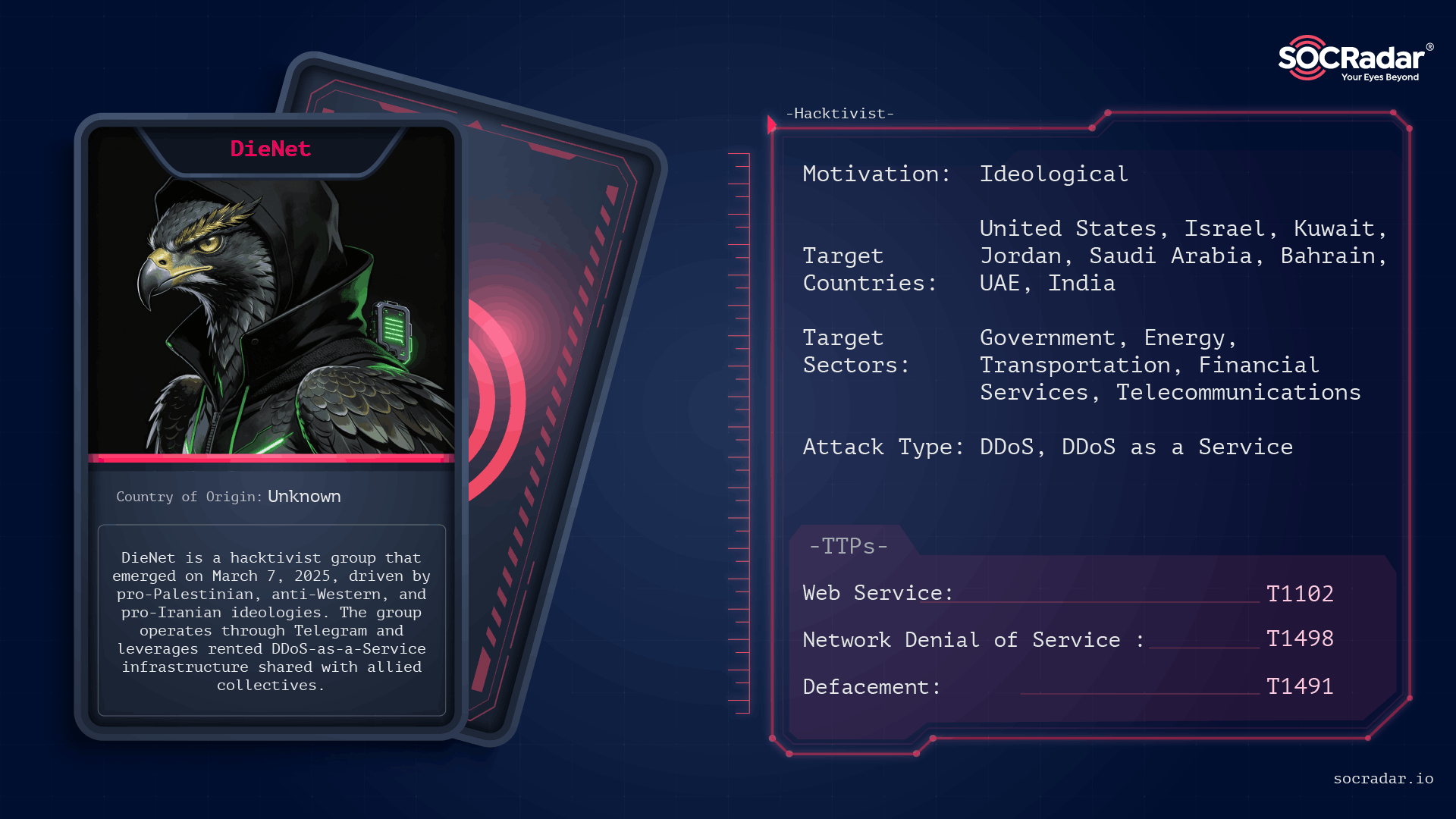
Threat actor card of DieNet
The group’s activity surged within days, particularly after the arrest of Columbia University activist Mahmoud Khalil, which served as an ideological catalyst. By March 12, banned DieNet’s primary channel. Rather than dissolving, the group rebranded as DieNet-v2, adopting a more decentralized structure designed to withstand platform moderation. Posts reference iterations up to DieNet-v5, each claiming expanded capabilities and growing membership.
Structurally, DieNet looks more like a franchise than a classic :
- A core inner circle managing brand, messaging, and strategic direction
- A wider ring of opportunistic operators running DDoS attacks, defacements, and leaks under the DieNet label
DieNet is not merely a DDoS collective but also a propaganda operation. Its campaigns prioritize spectacle over impact, built around a deliberately constructed counter-cultural identity designed to facilitate recruitment. This image is sustained through:
- Strategic timing of operations around geopolitical events
- Symbolic targeting of critical infrastructure to erode public confidence
- Media staging via Telegram posts and AI-generated imagery
- Emotionally charged messaging that frames opponents as “Zionist allies” or “imperialist tools”
The group’s exact origins remain unclear, though its activity suggests probable ties to Middle Eastern and Eastern European ecosystems, with links to pro-Palestinian, pro-Russian, and pro-Iranian collectives. Multiple 2026 analyses describe it as broadly pro-Iranian in orientation. Its integration into a unified cyber command known as the “Electronic Operations Room” during the 2026 Iran conflict suggests strategic alignment, if not direct coordination, with state-level interests.
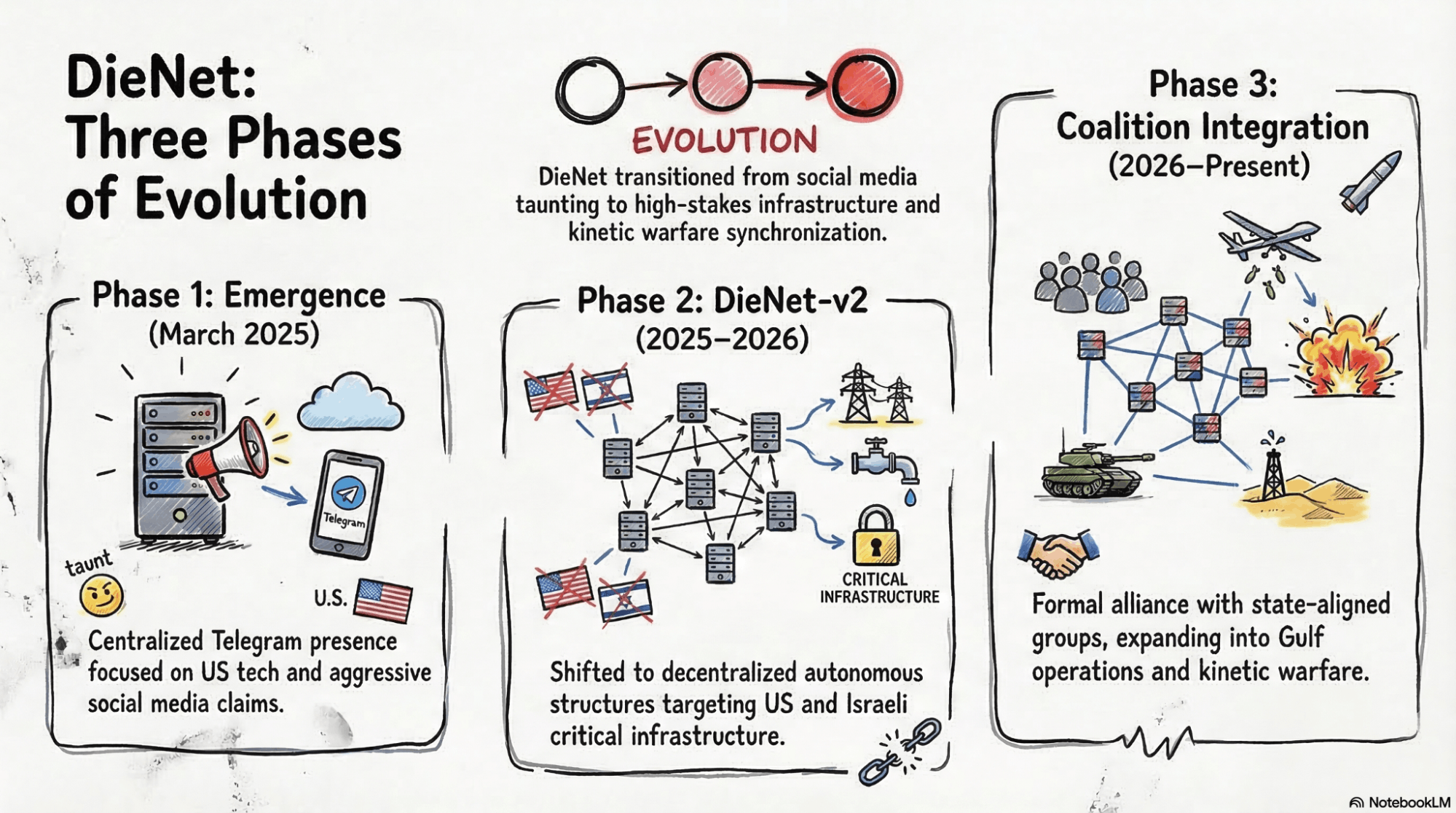
Organizational Evolution of DieNet
What Are DieNet’s Targets?
DieNet’s targeting is shaped by geopolitical events and designed to maximize symbolic disruption. The group focuses overwhelmingly on critical infrastructure and government-facing services, choosing targets that generate media attention and project an image of power. Its target selection mirrors the political map around Iran and Israel: government portals and ministries in Israel and Israel-aligned states, financial institutions and telecoms across the U.S. and the Gulf, and critical infrastructure sectors in countries that feature in the .
United States
The U.S. has been DieNet’s primary target since its inception. During its most prolific early campaign (March 11-17, 2025), the group claimed 61 attacks against 19 separate U.S. organizations. Targets spanned transportation (Port of Los Angeles, Chicago Transit Authority, LA Metro), energy (North American Electric Reliability Corporation, PJM Interconnection), finance (NASDAQ, Amazon Pay, The Clearing House), healthcare (Epic Systems, MediTech), and digital platforms (X, Internet Archive, SpaceX, TikTok, Meta).
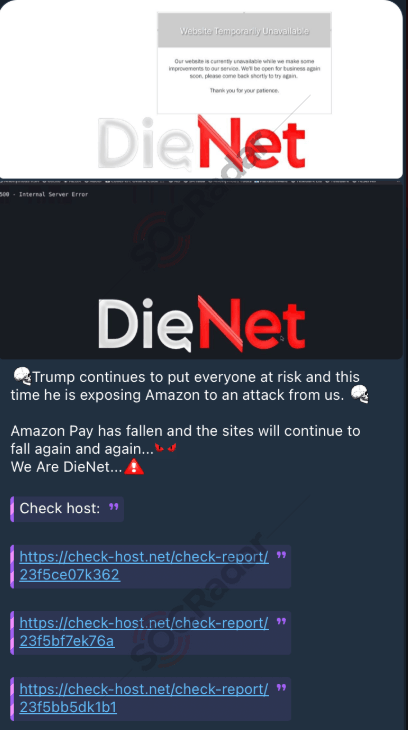
DieNet’s DDoS attack claim on Amazon Pay
A distinctive feature of this campaign was a personalized vendetta against Trump-affiliated businesses, including Trump Winery, Trump International Beach Resort, and various golf courses. Analysts note that DieNet has targeted Trump-related websites for at least a year, predating the group’s official Telegram debut – suggesting the actors behind DieNet may have been active under different banners before the March 2025 launch.
The 2026 Middle East Escalation
The most dramatic expansion came during the February-March 2026 escalation following the U.S.-Israeli military campaigns against Iran. DieNet framed its attacks as retaliation against countries that hosted U.S. military bases or opened their airspace for strikes on Iranian targets. In a systematic multi-day campaign, the group launched attacks across the Gulf and broader Middle East.
DieNet’s Telegram post
Based on tracked attack data from this period, DieNet recorded 59 distinct attack claims across two days (March 2-3, 2026), making it the most active pro-Iranian hacktivist group during the escalation – ahead of Keymous Plus (51), 313 Team (42), Conquerors Electronic Army (36), and (32).
DieNet’s Attack Distribution During the March 2026 Escalation (by Target Country):
| Target Country | Attack Count | Primary Sectors Targeted |
| Kuwait | 21 | Government (Defense, Public Admin, Energy, Healthcare, IT, Telecom), Financial Services, Aviation, Transportation |
| Bahrain | 15 | Government (multiple portals) |
| Israel | 14 | Financial Services, NGO, Telecommunications, Legal, Aviation & Aerospace |
| United Arab Emirates | 4 | Government, Public Service & Administration, Media & Entertainment |
| Jordan | 2 | Government, Information Technology |
| United States | 1 | Defense |
| United Kingdom | 1 | NGO |
| Turkey, Poland, Saudi Arabia, Oman, Qatar | 1 | Infrastructure (multi-country OT/ICS claim) |
Key named targets during this period included Kuwait’s Armed Forces website, Ministry of Defense, Ministry of Electricity and Water, Kuwait Airport, Kuwait Finance House, National Bank of Kuwait, and Gulf Bank; Bahrain Airport, Batelco, and General Organization for Social Insurance; Abu Dhabi Digital Authority, Sharjah Airport, and Ras Al Khaimah Airport; Qatar’s e-Government Portal, Ministry of Foreign Affairs, and Ministry of Education; Saudi Arabia’s National Commercial Bank, Riyadh Bank, and Al Rajhi Bank; and Jordan’s Petra News Agency, National Cyber Security Center, and King Hussein International Airport.
According to Radware, across all hacktivist groups during the late February – early March 2026 window, a total of 149 DDoS claims were recorded against 110 organizations in 16 countries. Within the Middle East, attacks were heavily concentrated in Kuwait (28%), Israel (27.1%), and Jordan (21.5%). Nearly 47.8% of all targeted organizations globally belonged to the government sector, followed by finance (11.9%) and telecommunications (6.7%).
Beyond the Gulf: Israel, India, and New Frontiers
Israel remains a persistent target beyond the Gulf campaigns. In March 2026, DieNet attacked the website of NSO Group Technologies – the Israeli firm behind the Pegasus spyware – demonstrating a preference for symbolically charged targets. The group also claimed attacks on Israel’s Ministry of Tourism and the Hadassah Zedek Medical Center in Jerusalem, with the latter accompanied by a data breach claim.
In May 2025, DieNet expanded into South Asia during the India-Pakistan standoff following the Pahalgam crisis, collaborating with Sylhet Gang-SG and Team Azrael to target Indian government portals. The group claimed a 247 GB data exfiltration from India’s National Informatics Centre (NIC), though forensic analysis by CloudSEK revealed the data consisted almost entirely of publicly available marketing materials – a textbook case of volume inflation for psychological effect.
DieNet has also signaled intent to target Cyprus due to its hosting of British military bases, and has referenced Azerbaijan for its perceived ties to Israel and the U.S., expanding its targeting logic to any nation perceived as facilitating Western military operations, regardless of whether those nations are directly involved in active hostilities. Egyptian telecommunications and payment providers have also been targeted, accused of collaborating with Israel.
This pattern shows how DieNet and aligned actors frame European territories that host Western infrastructure as extensions of the Middle East battlefield, implicitly linking their targeting logic to Iran’s strategic worldview.
What Are DieNet’s Techniques?
DieNet’s core competency today is disruption, not stealth. Its technical operations are defined by the efficient use of rented -as-a-Service (DaaS) infrastructure rather than the development of bespoke malware. This model allows the group to launch high-volume campaigns with minimal investment, shifting targets at a speed that often outpaces traditional perimeter defenses.
What Attack Vectors Does DieNet Use?
DieNet’s technical signatures involve a rotation of network-layer and application-layer vectors, varied between targets to bypass automated mitigation.
- TCP RST Floods: Forged reset packets that prematurely terminate legitimate connections on the target server.
- DNS Amplification: Exploits misconfigured open DNS resolvers to reflect massive traffic volumes toward the target, with amplification factors of up to 50x.
- TCP SYN Floods: Classic half-open connection attacks that exhaust server resources and render systems unresponsive.
- NTP Amplification: Small monlist requests to NTP servers produce disproportionately large response packets directed at the victim.
- Layer 7 Targeting: Application-layer attacks against government portals, dashboards, and APIs across finance, transport, and government sectors.
The group claims to have developed new methods specifically designed to disrupt target server memory and processor functions, alongside Layer 4 improvements. While these claims warrant skepticism, they reflect DieNet’s ongoing effort to project escalating technical sophistication.
What Capabilities Beyond DDoS Does DieNet Claim?
While DDoS remains DieNet’s primary tool, the group has made several claims suggesting broader ambitions. These should be evaluated carefully, as DieNet has a documented history of presenting open-source data as proprietary breaches.
- Locknet Ransomware DieNet announced “Locknet” as its own , allegedly used against UTLX, a Marmon Rail Company subsidiary in Chicago. The group shared employee images and threatened to release company documents, framing the attack in ideological terms. However, given DieNet’s track record of inflating claims, most notably repackaging publicly available materials as a 247 GB breach in the NIC India incident, the Locknet claim remains unverified.
- TOIPOI Intelligence Platform In January 2026, DieNet announced a “secret intelligence project” described as an integrated platform with automated data collection and real-time processing. No independent verification has emerged.
- OT/ICS Signaling During the March 2026 campaign, DieNet-affiliated channels shared screenshots allegedly showing access to Industrial Control Systems and PLC interfaces, such as VeroPoint systems used in power plants and grain silos. The group’s attack data includes one OT/ICS intrusion claim spanning 10 countries. While likely exaggerated for psychological effect, this signals an intent to target physical infrastructure, a significant escalation from purely digital disruptions.
These announcements follow a consistent pattern where DieNet uses capability claims as a psychological amplification tool, projecting sophistication to attract recruits, intimidate targets, and maintain media relevance regardless of whether the underlying capabilities are real.
Who Are DieNet’s Allies and What Ecosystem Does It Operate In?
DieNet sits inside a sprawling pro-palestinian hacktivist ecosystem that, as of March 2026, includes at least 60 identified groups aligned against Israel, the U.S., and their perceived regional partners. This ecosystem spans pro-Palestinian collectives, Shiite-aligned Iraqi groups, pro-Russian hacktivists, Southeast Asian operators, and North African crews, all loosely coordinated through Telegram and unified by shared targeting logic rather than a single command structure.
On its launch day (March 7, 2025), DieNet was promoted by established actors including and Sylhet Gang-SG, granting the new group immediate visibility and credibility. It also shares DDoS-as-a-service infrastructure with OverFlame and DenBots Proof, confirmed through attack source analysis.
- The Electronic Operations Room: On March 1, 2026, the Cyber Islamic Resistance announced the formation of a joint “Electronic Operations Room” (EOR) and launched a general cyber mobilization campaign. Teams including RipperSec and Cyb3r Drag0nz declared integration into this unified command. DieNet served as a high-volume DDoS engine for synchronized strikes, designed to sustain operations even as Iran’s connectivity collapsed to 1-4% of normal following kinetic strikes.
- DieNet as an Arsenal Provider: DieNet functions as a DDoS arsenal for smaller hacktivist groups. During the March 2026 campaign, groups like Mad Ghost launched attacks using DieNet’s infrastructure, while Sylhet Gang-SG forwarded its attack claims through their own channels. This force multiplier role extends DieNet’s impact well beyond its own operators.
- Pro-Russian Convergence: From March 3, 2026, pro-Russian groups began formally joining the pro-Iran coalition. NoName057(16) re-engaged Israeli targets while hitting European infrastructure; Server Killers entered citing U.S.-Israel strikes; Z-Pentest Alliance published OT/ICS access claims against Israeli water infrastructure; RuskiNet began daily DDoS attacks on Israeli industrial targets. The cyber front is no longer regional.
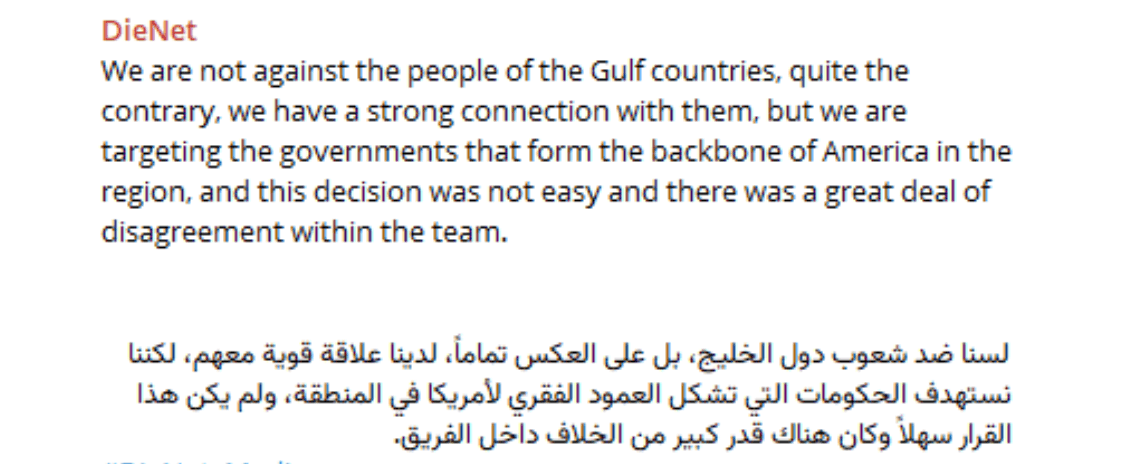
- Internal Tensions: DieNet clarified in a rare public statement that its targeting was directed at governments, not people. The group admitted the decision to target Gulf states followed significant internal disagreement. Analysts describe DieNet and its allies as an “outrage cluster” that is broadly pro-Palestinian but willing to criticize all parties, making its targeting unpredictable.
Why DieNet Matters for Defenders
DDoS-driven groups are often dismissed as low-tier, but in a hybrid conflict their regional impact goes beyond temporary downtime:
- Public confidence: Outages of government, banking, or telecom portals in Israel, the Gulf, or exposed European territories during crises can deepen distrust and panic among civilian populations.
- Operational disruption: Even simple attacks can slow emergency coordination, cross-border trade, and diplomacy if critical dashboards and services go offline at the wrong moment.
- Hybrid signaling: DDoS waves timed with strikes on Iran or Israeli operations become part of Iran-aligned pressure on regional governments, signaling capability and resolve.
- Noise for cover: The noisier DieNet is on the front end, the easier it is for quieter Iran-linked APT groups to operate in the background with less scrutiny. DDoS as a distraction layer is a well-documented tactic in hybrid conflict.
What Are the Mitigation Tactics Against DieNet?
Defending against DieNet requires a layered approach addressing both the volumetric DDoS threat and the group’s evolving ambitions toward data exploitation and OT signaling.
- DDoS Mitigation Infrastructure: Work with your ISP to apply upstream traffic filtering or blackhole routing during volumetric surges. Deploy cloud-based scrubbing services and CDNs to absorb attack traffic before it reaches your infrastructure. Implement DNS protection services that rate-limit resolver queries to prevent amplification attacks, and leverage cloud provider shields with auto-scaling and traffic distribution capabilities.
- Perimeter and Application Controls: Deploy tuned to detect bot-like patterns such as header spoofing, path fuzzing, and abnormal query counts. Implement rate limiting and behavioral anomaly detection to identify Layer 7 floods that mimic legitimate traffic, and apply dynamic IP blocking when robotic traffic patterns emerge.
- Credential and Identity Hardening: Enforce phishing-resistant MFA across all remote access points, VPNs, and email systems. Audit and restrict external access to employee HR and payroll systems, particularly in organizations operating in targeted sectors and regions.
- OT/ICS Hardening: Disconnect internet-facing industrial control systems and audit PLCs for unauthorized logic changes. Ensure proper segmentation between IT and OT networks and validate isolation of IoT devices.
- Threat Intelligence and Monitoring: Monitor DieNet’s Telegram channels for early warning on declared targets and campaign timing. Anticipate escalation during geopolitical flashpoints, as DieNet’s operations consistently spike in response to military actions. Update threat intelligence signatures to reflect DieNet’s rotating attack vectors.
How Can SOCRadar Help?
SOCRadar provides layered visibility to help organizations move from reactive defense to proactive threat management against hacktivist collectives like DieNet.
Threat Actor Intelligence: Real-time tracking of DieNet and associated groups, including their declared campaigns, evolving TTPs, alliance shifts, and infrastructure changes.
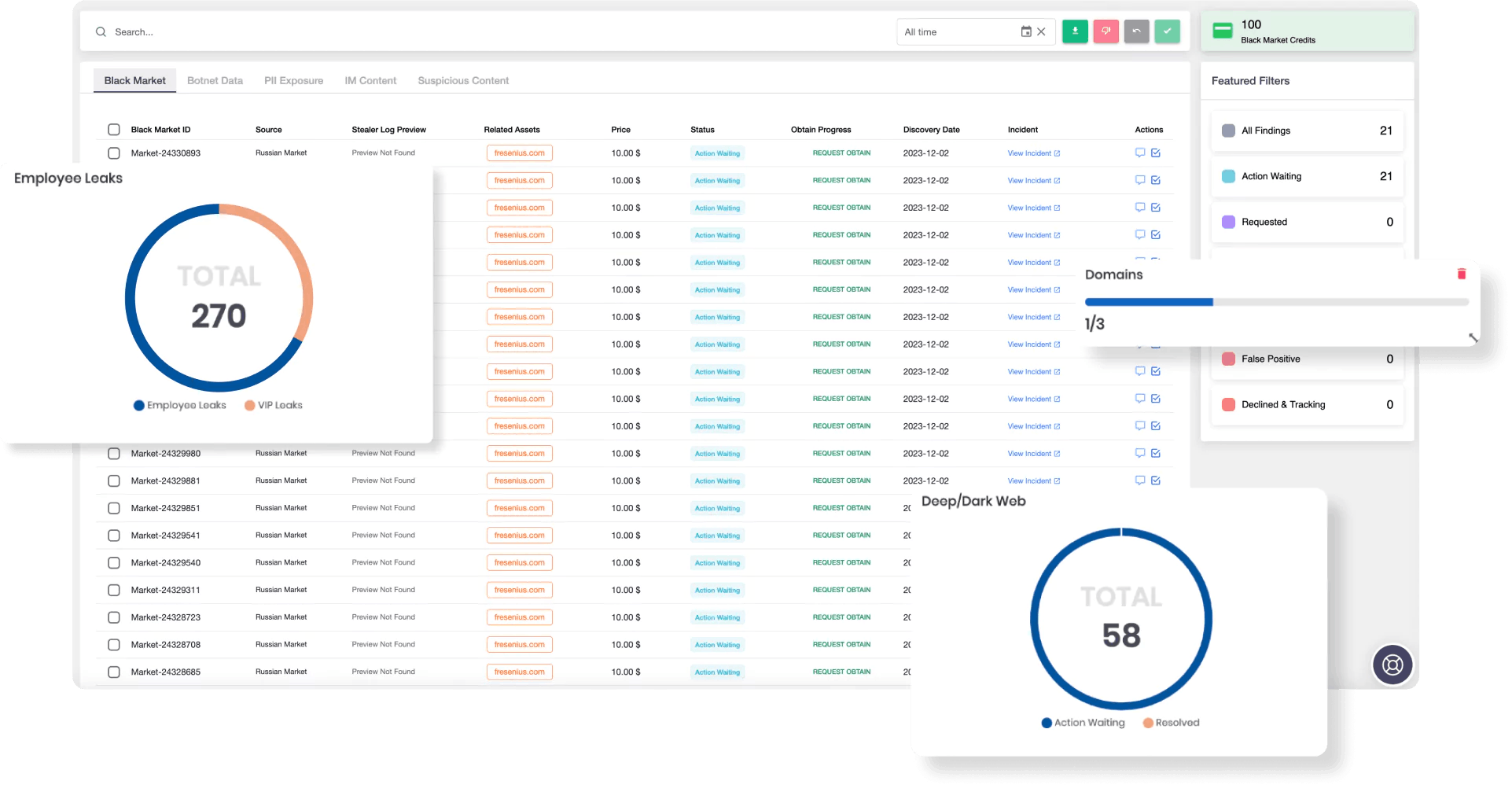
SOCRadar Dark Web Monitoring
: Continuous surveillance of DieNet related Telegram channels (DieNet Main, DieNet API Information, DieNet Hack, DieNet Media) and affiliated underground platforms. SOCRadar surfaces declared attack targets, breach claims, and recruitment activity, providing early warning before campaigns reach your perimeter.
: Identifies exposed internet-facing services, DNS configurations vulnerable to amplification abuse, and external assets that DDoS-focused actors commonly exploit.
: For organizations tracking the broader cyber dimension of the Iran-Israel confrontation, SOCRadar’s dedicated conflict dashboard provides a consolidated view of APT group activity, hacktivist operations, DDoS campaigns, data leaks, defacements, and Telegram channel signaling – all tied directly to this conflict. The dashboard covers groups including DieNet, Keymous+, NoName057(16), Handala, and others with analyst-vetted assessments, separating verified intelligence from the noise of hundreds of daily claims.
SOCRadar Labs DoS Resilience
: As an immediate first step, organizations can use SOCRadar’s free DoS Resilience service to assess their domain’s or subnet’s resilience against various denial-of-service attack types.
MITRE ATT&CK TTPs Associated with DieNet
| Tactic | Technique ID | Technique Name |
| Reconnaissance | T1592 | Gather Victim Host Information |
| Reconnaissance | T1590 | Gather Victim Network Information |
| Resource Development | T1583.005 | Acquire Infrastructure: Botnet |
| Resource Development | T1584.005 | Compromise Infrastructure: Botnet |
| Initial Access | T1190 | Exploit Public-Facing Application (defacements, admin panel takeover) |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols |
| Command and Control | T1090 | Proxy (hiding origin, controlling DDoS infrastructure) |
| Impact | T1498 | Network Denial of Service |
| Impact | T1498.001 | Network DoS: Direct Network Flood |
| Impact | T1498.002 | Network DoS: Reflection Amplification |
| Impact | T1499 | Endpoint Denial of Service |
| Impact | T1491.001 | Defacement: External Defacement |
| Impact | T1565 | Data Manipulation (staged “leaks”) |
DieNet’s primary confirmed TTP is Network Denial of Service (T1498). Claims of defacement, intrusion, OT/ICS access, and data manipulation remain largely unverified or exaggerated. The MITRE mappings above reflect both confirmed techniques and those claimed by the group for completeness.