CVE-2026-3055: NetScaler Memory Disclosure Puts SAML-Enabled Edge Devices at Risk
Citrix has released fixes for two NetScaler vulnerabilities that security teams should review right away: CVE-2026-3055 and CVE-2026-4368. The first is a critical memory overread issue while the second is a race condition that can cause user session mix-ups. Both matter because NetScaler ADC and NetScaler Gateway often sit at the network edge and handle sensitive authentication traffic.
Organizations should verify whether affected appliances are internet-facing, confirm whether the vulnerable features are enabled, and move patching to the top of the queue. Public details are still limited, so defenders should separate what the vendor has confirmed from what remains informed analysis.
What Is CVE-2026-3055?
CVE-2026-3055 (CVSS 9.3) is a critical out-of-bounds read vulnerability. Citrix describes it as insufficient input validation that can lead to memory overread in NetScaler ADC and NetScaler Gateway when the appliance is configured as a SAML Identity Provider (IdP).
In practical terms, a memory overread can expose sensitive data that should never leave the appliance. Public reporting does not yet confirm exactly which artifacts can be leaked in successful attacks, but defenders should assume that any sensitive data resident in memory could increase operational risk until patched.
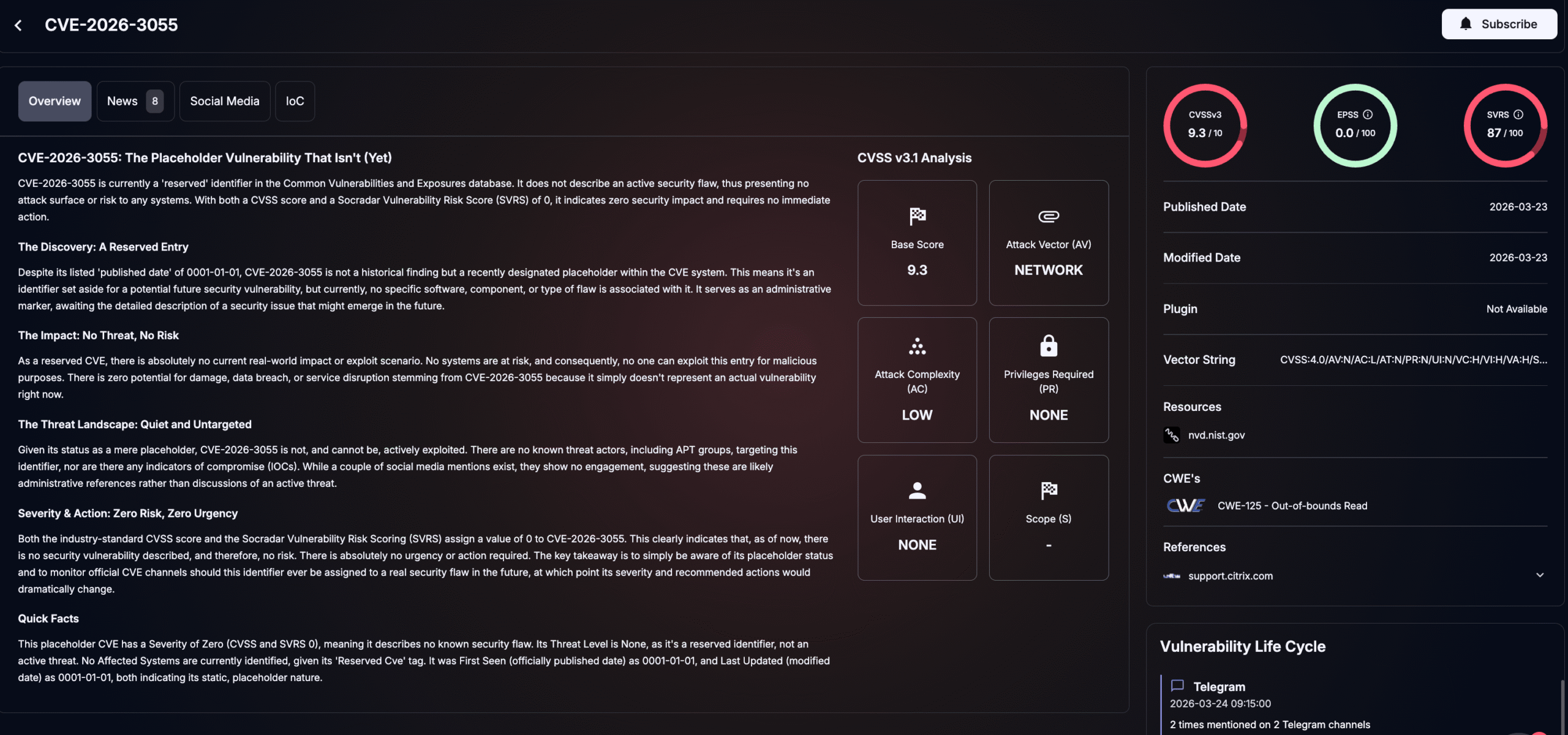
Details of CVE-2026-3055 (SOCRadar Vulnerability Intelligence)
What Is CVE-2026-4368?
CVE-2026-4368 (CVSS 7.7) is described as a race condition that can lead to user session mix-up. Citrix and downstream advisories say this issue affects systems configured as a Gateway, including SSL VPN, ICA Proxy, CVPN, and RDP Proxy, or as an AAA virtual server.
Session mix-up flaws can create serious access-control problems. Even without remote code execution, they may allow one user to interact with another user’s session under the wrong conditions. That makes the issue especially important in environments where NetScaler handles remote access and identity workflows.
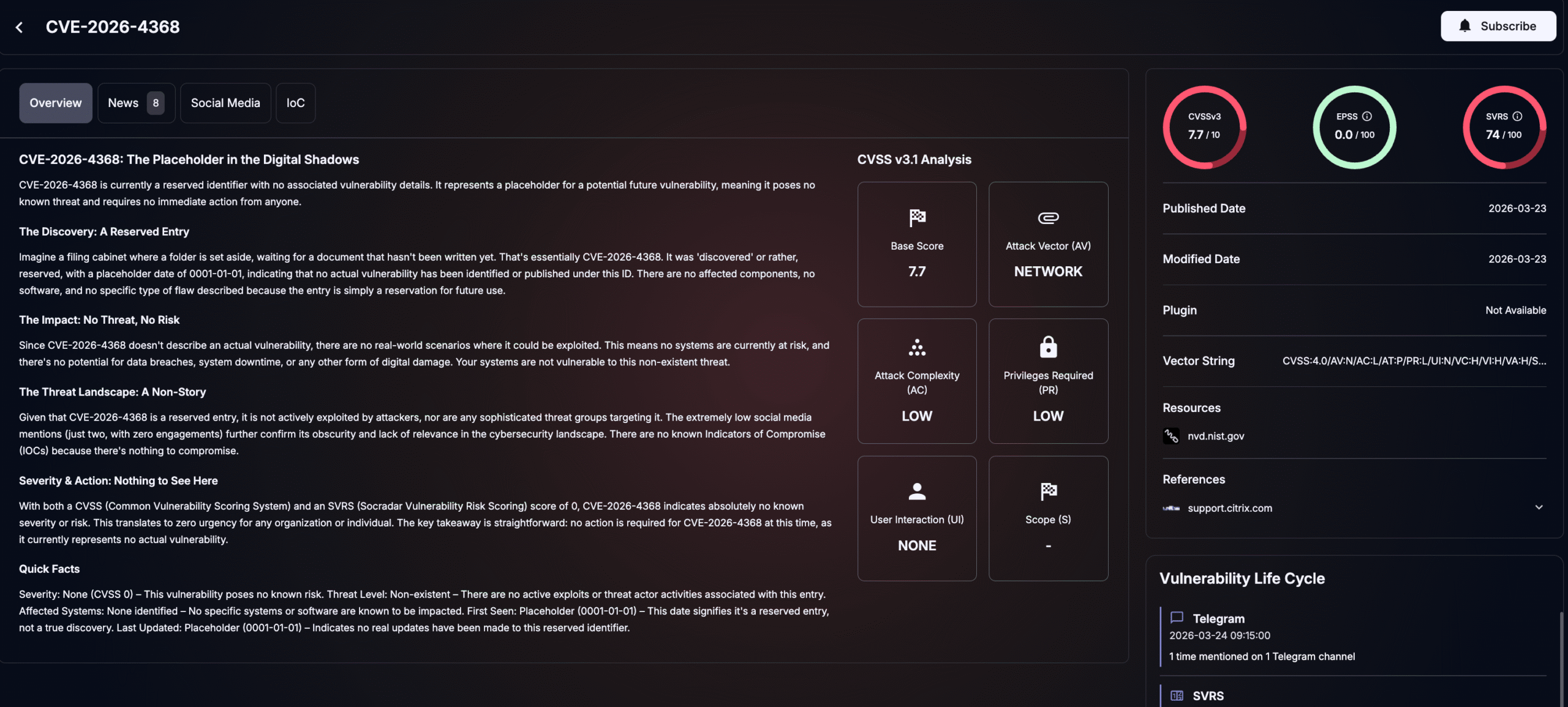
Details of CVE-2026-4368 (SOCRadar Vulnerability Intelligence
Which NetScaler Versions Are Affected Right Now?
At the time of writing, public reporting and Citrix-linked advisories identify these affected versions:
CVE-2026-3055
- NetScaler ADC and NetScaler Gateway 14.1 before 14.1-66.59
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-62.23
- NetScaler ADC FIPS and NDcPP before 13.1-37.262
CVE-2026-4368
- NetScaler ADC and NetScaler Gateway 14.1-66.54 when configured as Gateway or AAA virtual server, according to current public reporting on the Citrix bulletin.
Teams should treat the vendor bulletin and release notes as the source of truth during upgrade planning.
How Could Exploitation Work in Real Environments?
For CVE-2026-3055, the confirmed issue is unauthenticated memory disclosure on SAML IdP deployments. The most immediate concern is not just data leakage in isolation, but what that data might enable afterward if it includes security-sensitive material. That follow-on impact is still an inference, but it is a reasonable one for an internet-facing authentication appliance.
For CVE-2026-4368, exploitation may be harder to spot because race conditions can be intermittent. The operational risk is that session handling breaks in a way that associates one user with another user’s authenticated context. In gateway deployments, that can translate into unauthorized visibility or actions.
Is There Confirmed Exploitation in the Wild or a Public PoC?
At the time of writing, there is no public vendor confirmation that either vulnerability is being actively exploited in the wild, nor has a public proof-of-concept (PoC) emerged as of March 24, 2026. That said, the disclosure is very recent, and NetScaler edge flaws have historically drawn fast attention from attackers and researchers.
That means defenders should not wait for exploitation headlines before acting. In practice, exposure, feature configuration, and internet reachability matter more than whether public exploit code has appeared yet.
What Should Defenders Do Now to Reduce Risk?
- Patch affected systems first
Use the Citrix bulletin and release notes to validate the right fixed build for each deployment. Teams running internet-facing NetScaler devices should treat this as a priority patching event.
- Triage based on feature exposure
Move these appliances to the front of the line if they are:
- Configured as SAML IdP for CVE-2026-3055
- Configured as Gateway or AAA virtual server for CVE-2026-4368
- Exposed to the public internet
- Review post-patch hygiene
For a memory disclosure issue, a conservative response can be justified even when exploitation is unconfirmed. Depending on the environment, that may include restarting appliances after upgrade, expiring active sessions, and rotating secrets that may have been present in memory. This is defensive best practice rather than vendor-confirmed remediation guidance.
- Use normal HA upgrade discipline
Where high-availability pairs are involved, follow the standard staged upgrade process and align each step with internal change controls and the vendor’s release guidance.
- Monitor external exposure continuously
This is also a good example of why continuous edge visibility matters. Internet-facing appliances often become urgent patch candidates with little notice.
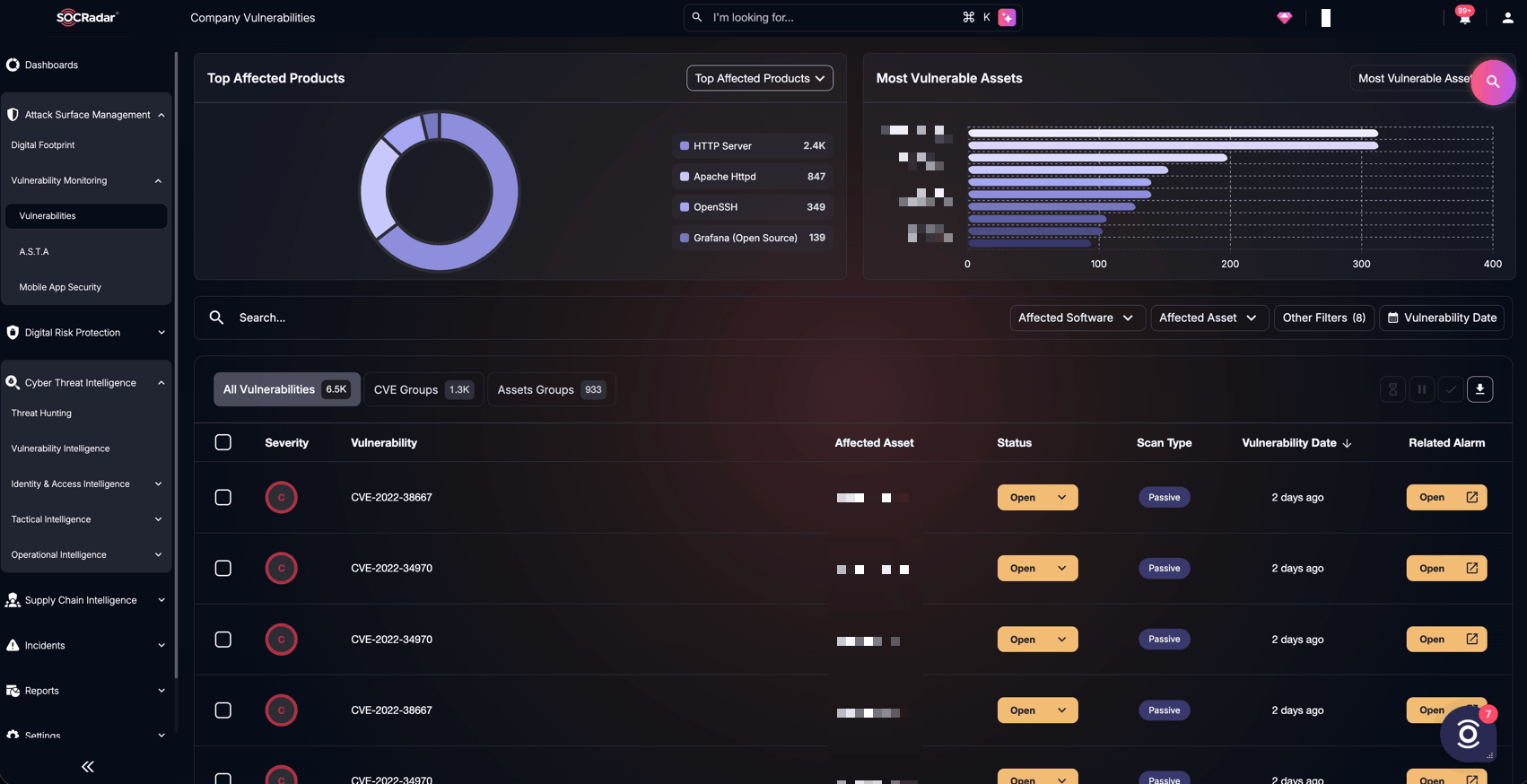
SOCRadar’s Attack Surface Management, Company Vulnerabilities
Security teams using External Attack Surface Management and Vulnerability Intelligence can identify exposed NetScaler assets faster, prioritize risky configurations, and reduce the gap between disclosure and remediation.
