CVE-2025-32975: Quest KACE SMA SSO Authentication Bypass Enables Admin Takeover
Quest KACE Systems Management Appliance (SMA) has a maximum-severity vulnerability, CVE-2025-32975, that allows an attacker to bypass authentication in the product’s SSO authentication handling. An unauthenticated attacker can potentially impersonate legitimate users and work toward full administrative takeover. Reporting in March 2026 tied suspicious, real-world activity to exploitation of internet-exposed, unpatched KACE SMA systems.
This post covers what the vulnerability is, which versions are affected, what we know about exploitation and PoC availability, and what defenders should do immediately.
What Is CVE-2025-32975?
CVE-2025-32975 is an authentication bypass affecting Quest KACE SMA, specifically in the way the appliance handles Single Sign-On (SSO) authentication. The weakness maps to CWE-287 (Improper Authentication) and is rated CVSS 10.0, reflecting network reachability, no required privileges, and high impact on confidentiality, integrity, and availability.
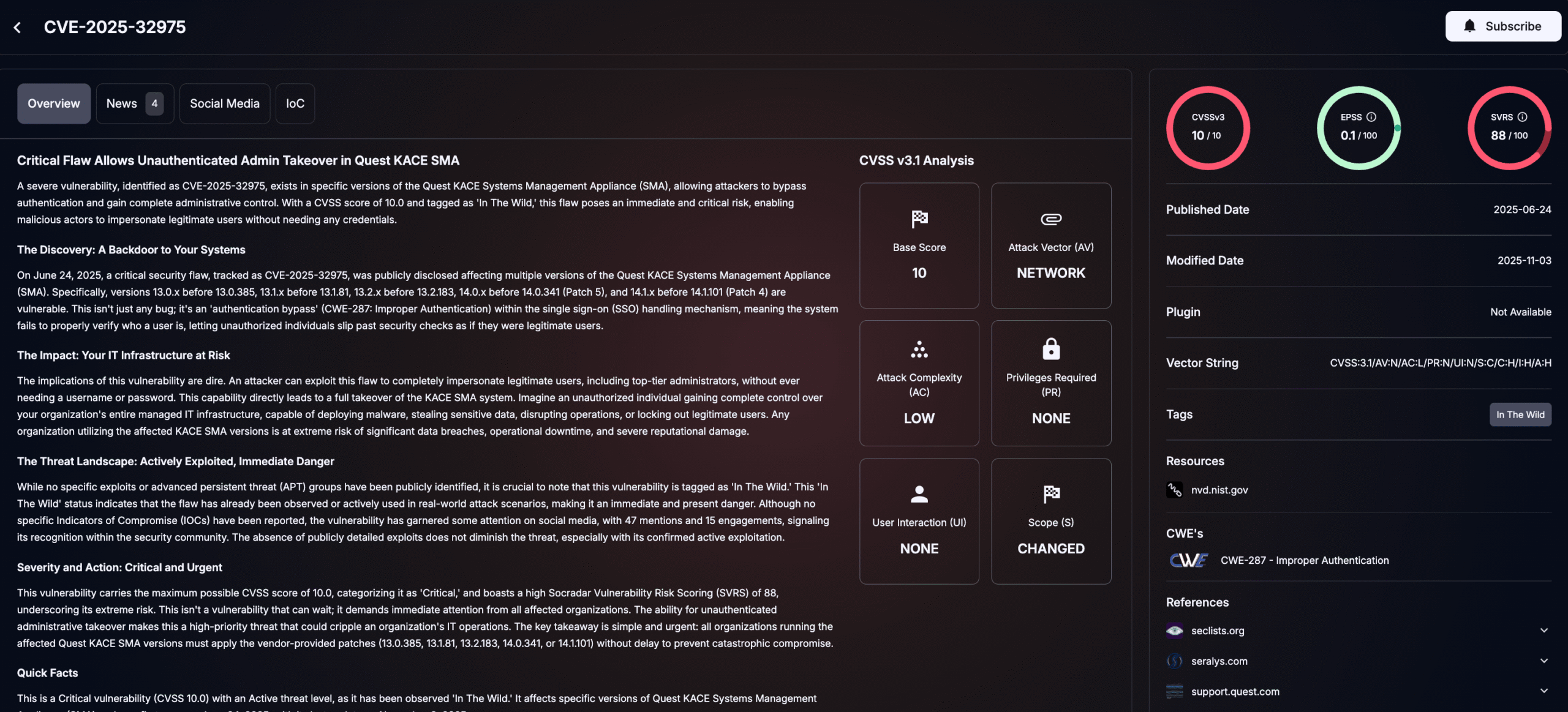
Details of CVE-2025-32975 (SOCRadar Vulnerability Intelligence)
In practical terms, the vulnerability can allow an attacker to impersonate a valid user without credentials. Because KACE SMA often holds high-value administrative functions for endpoint and systems management, the outcome can escalate quickly from unauthorized access to complete administrative control of the appliance.
Which Quest KACE SMA Versions Are Affected?
If you run KACE SMA in any of the below lines and you are below the fixed builds, treat the system as exposed until proven otherwise:
- 13.0.x before 13.0.385
- 13.1.x before 13.1.81
- 13.2.x before 13.2.183
- 14.0.x before 14.0.341 (Patch 5)
- 14.1.x before 14.1.101 (Patch 4)
Quest’s published remediation guidance centers on applying the relevant hotfix/patch to reach these fixed versions and then planning upgrades to supported releases as part of normal lifecycle management.
What Is the 13.x Hotfix Caveat Defenders Miss?
Quest also calls out a key operational detail for 13.x: the 13.x security hotfix must be re-applied after any full 13.x upgrade. If your process includes routine upgrades inside the 13.x family, build a control that verifies the hotfix remains present after maintenance windows.
How Does Exploitation Work At a High Level?
Public descriptions characterize the issue as an SSO authentication handling bypass, but detailed root-cause mechanics were intentionally not fully published in early public materials. That means defenders should not expect a clean, step-by-step technical explanation of the vulnerable code path from public disclosure alone.
Even without deep public exploit detail, the risk profile stays clear:
- The vulnerability is pre-auth and network reachable.
- It enables user impersonation without credentials.
- It can plausibly lead to administrative takeover, depending on role mapping and how the platform is used in your environment.
Is There Active Exploitation in the Wild?
Timeline matters for prioritization:
- June 2025: Early advisories and bulletins reported no evidence of active exploitation and no open-source PoC at that time.
- March 2026: Researchers reported observing malicious activity starting the week of March 9, 2026, potentially linked to exploitation of internet-exposed, unpatched KACE SMA appliances, with suspected initial access via CVE-2025-32975.
Researchers’ reporting also described post-compromise patterns consistent with an attacker trying to turn initial access into durable control, including using KACE functionality for command execution, creating admin accounts, credential theft tooling (including Mimikatz), discovery, and lateral movement.
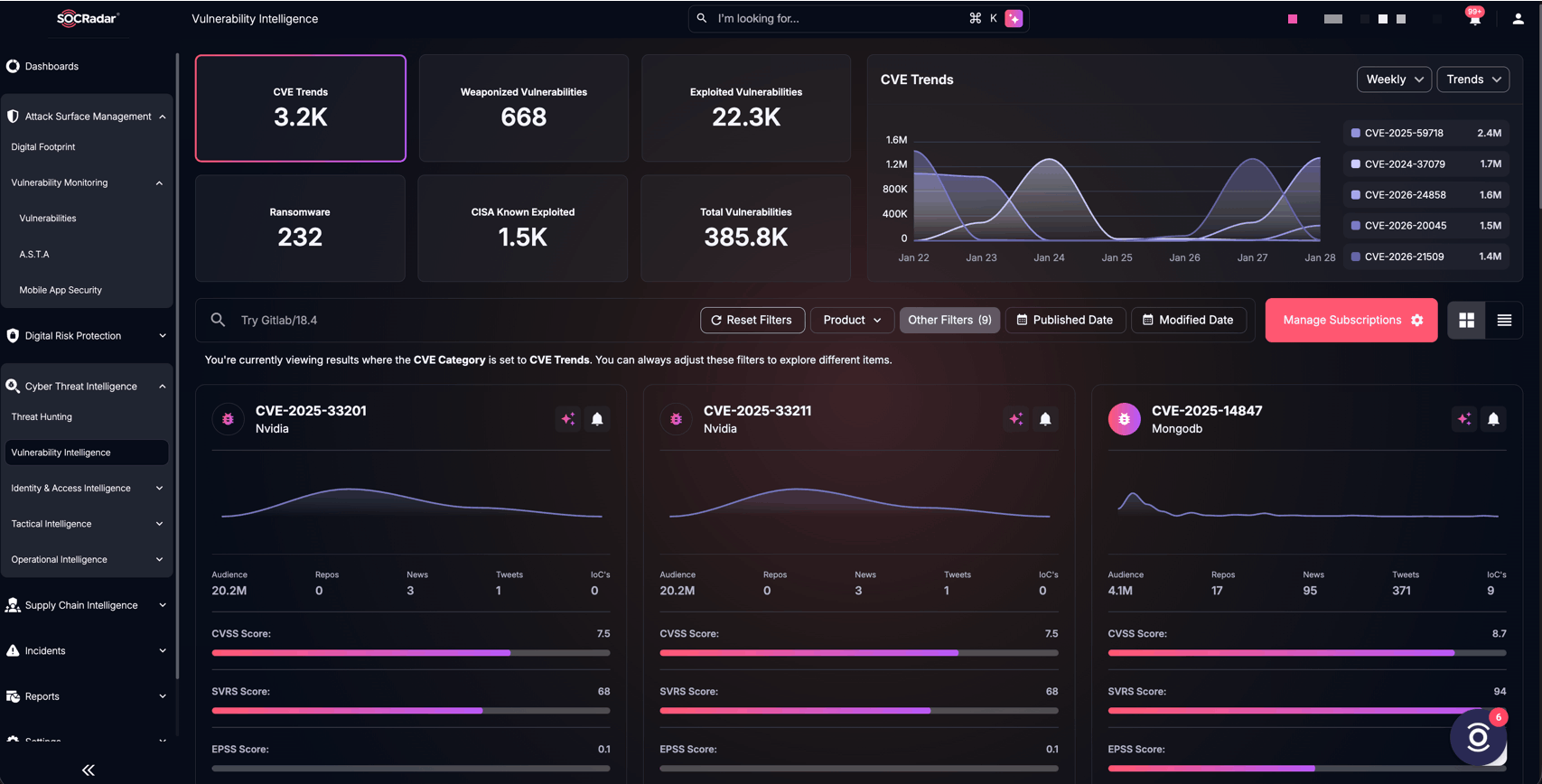
SOCRadar’s Vulnerability Intelligence
Critical vulnerabilities become real threats when they intersect with exposed assets. SOCRadar Cyber Threat Intelligence delivers early insight into active exploitation, emerging attack trends, and vulnerability weaponization, while Attack Surface Management (ASM) continuously maps your internet-facing assets to highlight what is actually exposed.
By connecting threat intelligence with your real attack surface, you can quickly identify which risks matter most and act before attackers do.
What Should Defenders Do Now?
- Patch and Verify the Fixed Build
Prioritize getting to one of the fixed versions immediately:
- 13.0.385
- 13.1.81
- 13.2.183
- 14.0.341 Patch 5
- 14.1.101 Patch 4
For 13.x, ensure your upgrade workflow includes a step to re-apply the security hotfix after full upgrades and confirm the appliance remains at the secure state post-change.
- Remove Internet Exposure
If your KACE SMA is reachable from the public internet, treat that as a high-risk condition. If remote administration is required, restrict access through VPN and tight firewall rules (allowlisted management IPs, geofencing where appropriate, and strong administrative access controls).
- Hunt for Post-Compromise Behavior
If you suspect exposure prior to patching, hunt for signs consistent with the observed behaviors reported in March 2026, including:
- Unusual KACE activity tied to remote command execution through KACE features
- Log artifacts showing Base64-encoded payloads
- New admin account creation or unexpected privilege changes
- Signs of credential theft tooling (including Mimikatz, potentially under deceptive filenames)
- Discovery and lateral movement patterns, including RDP activity into sensitive infrastructure like backups and domain controllers
