Crunchyroll Alleged Data Breach: What Do Users Need to Know?
Reports of a possible Crunchyroll (A popular anime streaming platform) data breach have drawn attention after claims surfaced that a threat actor may have accessed user-related data and internal support information. Crunchyroll has not publicly confirmed the full scope of those claims, so the story remains a mix of allegations, shared evidence, and unanswered questions. What makes the situation notable is the type of data said to be involved, including email addresses, IP addresses, and possibly other customer-related records, along with claims that third-party access may have been part of the incident.
The issue matters because even a limited leak of emails and IP addresses can still lead to real follow-on risks. That information can be used in , account targeting, , and broader profiling, especially when combined with older leaked datasets. This blog examines what has surfaced so far, what remains unconfirmed, what data may be involved, why the third-party angle matters, and what users and security teams should do next.
What Started the Crunchyroll Breach Discussion?
The story appears to have gained traction after posts shared by described an alleged compromise connected to Crunchyroll and claimed that a threat actor had accessed user-related information for a limited period of time. Those posts also referred to a dataset said to include customer analytics information and IP address data. The claims spread quickly because they were accompanied by screenshots and specific timing details, which made the discussion feel more concrete even though the full incident had not been independently confirmed.
What pushed the story beyond social media was the appearance of a separate underground signal. SOCRadar observed an alleged post tied to Crunchyroll in which masked email addresses and masked IP addresses were shown as sample data. That does not prove the full breach narrative on its own, but it does show that Crunchyroll-related information was being circulated in a threat-actor environment rather than remaining only a rumor on social platforms.
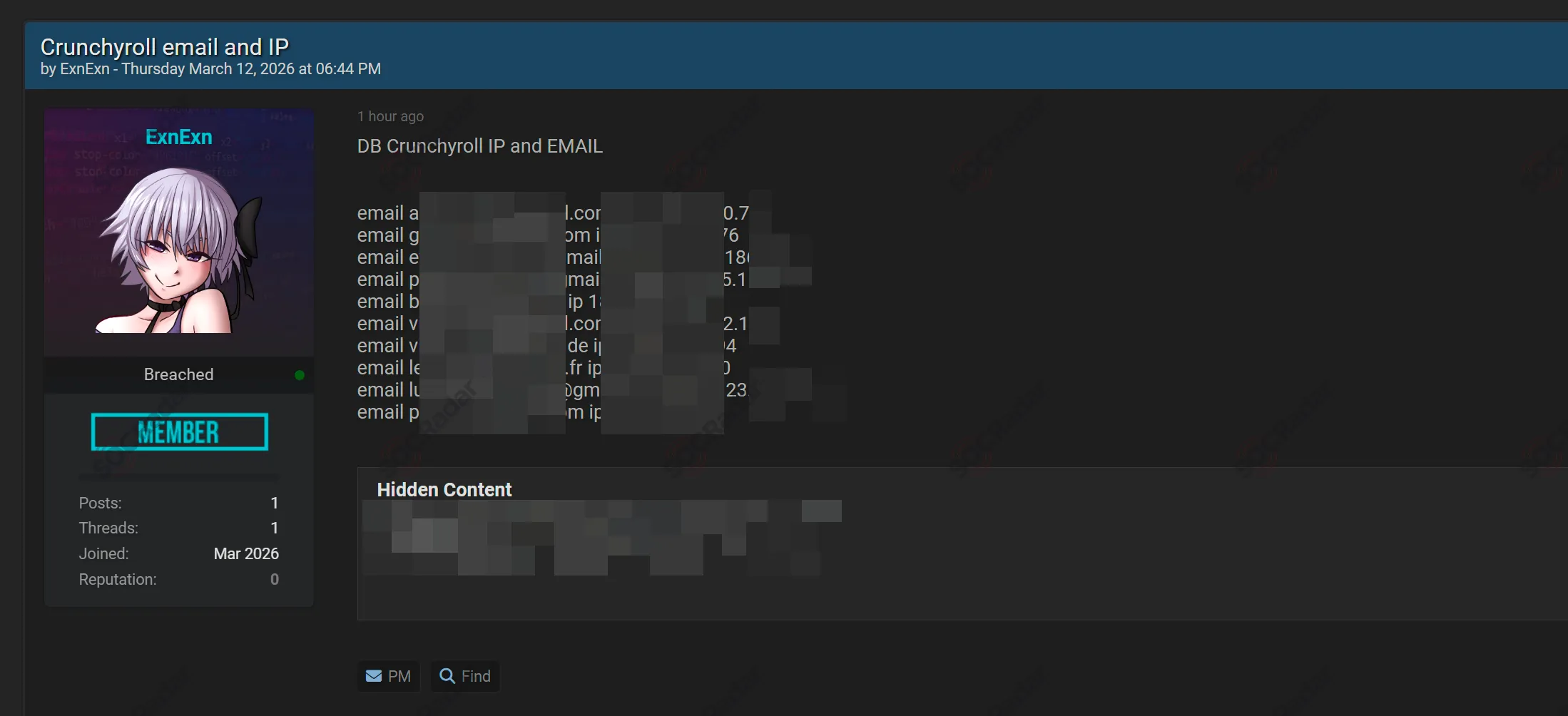
Detected hacker forum post advertising alleged Crunchyroll email and IP address data
Has Crunchyroll Confirmed the Incident?
So far, the main point of caution is simple: Crunchyroll has not publicly confirmed the full set of claims attached to this story. Public coverage has consistently framed the situation as an alleged or possible breach rather than a settled fact.
That difference matters more than it may seem. In early-stage security incidents, attacker claims, screenshots, and samples often travel faster than internal investigations. A company may still be validating whether data was actually accessed, copied, or exposed, and whether the systems shown in screenshots match production environments. Until Crunchyroll publishes a formal statement or another authoritative disclosure appears, the most accurate framing is that this is a reported incident under discussion, not a fully verified breach with confirmed scope.
What Data May Have Been Exposed?
The reports vary in scope. Some reports said the sample data source included IP addresses, email addresses, credit card details, and other information, while other coverage described the issue as involving customer analytics and ticketing data. Some articles also repeated a claim that about 100 GB of data may have been exfiltrated, but that figure remains based on reporting around attacker claims rather than a public company confirmation.
In addition to those public reports, monitoring from SOCRadar identified an alleged dark web post advertising Crunchyroll-related data. According to the monitored forum post, the exposed sample contained masked user email addresses paired with masked IP addresses.
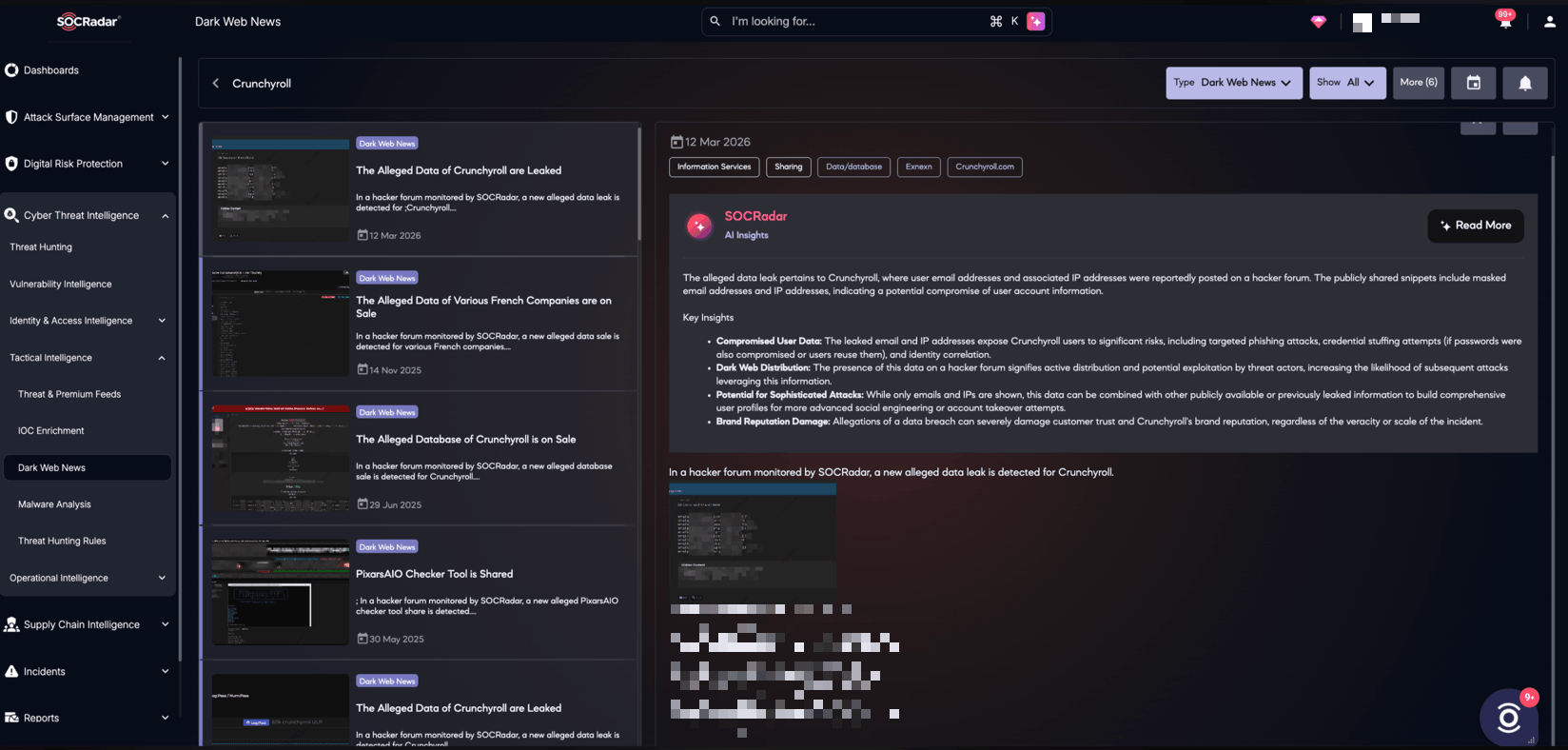
SOCRadar Dark Web News view showing the alleged Crunchyroll data leak and related risk insights..
Even if the visible sample is limited, that kind of data can still be valuable to threat actors because it can support targeted phishing, account enumeration, identity correlation, and follow-on credential attacks when combined with other leaked records.
Why Do Email Addresses and IPs Matter So Much?
It is easy to underestimate a leak when it does not immediately involve passwords or full payment card numbers. But emails and IP addresses are still actionable data. Email addresses give attackers a direct path for phishing or password-reset lures. IP information can add context about a user’s geography, provider, or usage pattern, making fake account alerts more convincing.
There is also a compounding effect. Threat actors regularly combine newer fragments with older breach data to build richer user profiles. A single dataset may not be enough for , but several partial datasets together can become far more useful. That is why even a seemingly limited leak can have a longer life after the original post appears.
Is There a Third-Party Risk Angle Here?
Yes, and that is one reason this story has drawn extra attention. The public claims tied the alleged exposure to Telus, which was described in outside reporting as part of Crunchyroll’s support or service environment. At the same time, Telus Digital has separately acknowledged that it is investigating unauthorized access involving a limited number of systems. That does not automatically validate every claim tied to Crunchyroll, but it does make the supplier angle relevant.
This is the part many companies should pay attention to. When support operations, analytics workflows, or ticketing systems are handled across company boundaries, the customer-facing risk no longer sits inside one environment. A weakness at a service provider can quickly become a problem for the brand its users actually recognize. In stories like this, the hardest question is often not “was one system breached?” but “which business relationships made the exposure possible?”
What Should Crunchyroll Users Do Right Now?
For users, the response should be practical rather than dramatic. Start by changing your Crunchyroll password, especially if it has been reused anywhere else. Watch for suspicious messages that mention billing, subscriptions, support tickets, password resets, or urgent account issues. Those are the kinds of themes attackers commonly use after alleged breaches become public.
It is also smart to review account activity and payment statements if you have stored billing details with the service. Even if the broader claims are never fully confirmed, attackers may still use the publicity around the incident to launch fake alerts and phishing campaigns that target anxious users.
What Should Security Teams Take Away From This?
For defenders, this case is a reminder that external visibility matters early. Social posts, underground forum chatter, and dark web monitoring can surface warning signs before a company has finished confirming what happened. In this case, the alleged forum post observed by SOCRadar gave an additional signal that the Crunchyroll claims were being discussed in threat-actor spaces, not only reposted by commentators.
The broader lesson is about shared risk. Brands that depend on outside for support, analytics, or customer operations need to treat third-party monitoring as part of everyday security, not just a compliance exercise. When a vendor-linked issue starts circulating publicly, quick validation, coordinated communication, and clear user guidance become just as important as the technical investigation itself.