AstraZeneca Data Breach: What You Need to Know
A newly surfaced Dark Web post is drawing attention to an alleged AstraZeneca data breach linked to the threat group. Based on the materials reviewed, the claim goes beyond a routine leak post and suggests possible exposure of internal code repositories, access-related data, cloud and infrastructure references, and employee-linked records.
If the claims are verified, this could become one of the more serious cyber events to hit the healthcare sector this year. This article breaks down what was claimed, what types of data may be involved, why the healthcare sector should pay attention, and what security teams should watch next.
What Happened?
An alleged breach involving AstraZeneca was advertised on a and also appeared on a data leak site associated with LAPSUS$. The listing claims the attackers obtained a large archive containing internal data, including source code, infrastructure-related material, and access-linked information.
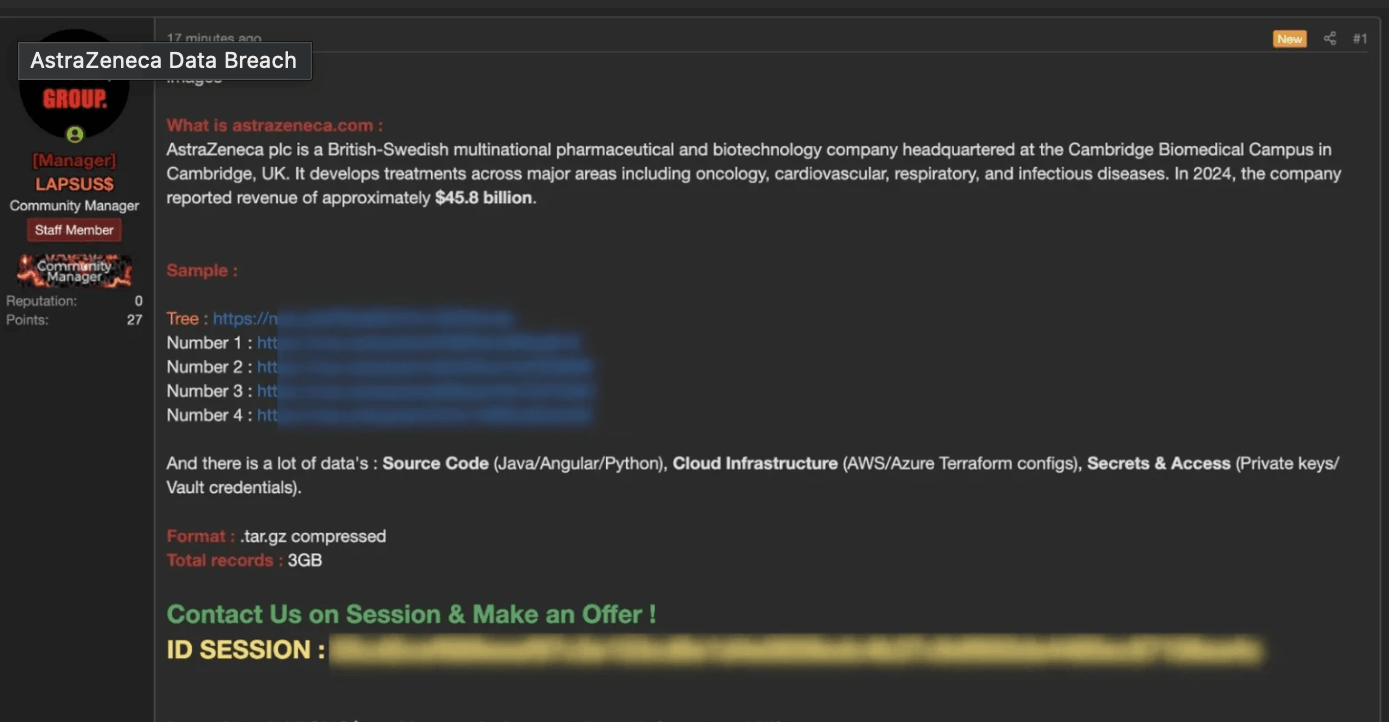
Dark Web post advertising an alleged AstraZeneca breach
The Dark Web post describes the victim as AstraZeneca and claims the exposed package includes source code in Java, Angular, and Python, as well as cloud infrastructure references tied to AWS, Azure, and Terraform. It also claims the archive contains secrets and access material, including references to private keys and vault credentials, and lists the leaked package as a compressed archive totaling roughly 3 GB.
What Data Was Allegedly Exposed?
The alleged breach appears to include several categories of potentially sensitive enterprise data.
Source Code & Application Components
File tree related to the alleged breach suggests the archive includes Java-based application code, including controllers, repositories, services, schedulers, configuration files, and Spring Boot resources. It also references internal project paths such as als-sc-portal-internal, database scripts, and environment-specific application files. That strongly suggests the leak may include software development assets rather than only business documents.
Cloud & Infrastructure references
The Dark Web claim mentions AWS, Azure, and Terraform-related materials. Even when infrastructure files do not contain live secrets, they can still give attackers useful insight into architecture, naming conventions, deployment logic, and service dependencies.
User & Access Management Data
Sample records indicate the alleged breach may include GitHub Enterprise-related user information, access roles, account status fields, and identity-linked records. One of the samples appear to map internal identifiers to corporate email addresses, while a separate file structure suggests permission and wiki access workflows may also be included.
This matters because identity and access information can be operationally valuable to attackers even when passwords are not directly exposed. It can help with phishing, privilege mapping, , and targeting internal systems.
Internal Databases & Operational records
The file tree also points to large numbers of SQL scripts, table definitions, views, sequence files, batch processes, and inventory or order-management components. In practical terms, that suggests the alleged breach may touch internal business operations, supply chain workflows, and system administration data, not just developer artifacts.
Why This Incident Matters for the Healthcare Sector
AstraZeneca is not just another enterprise target. It is one of the world’s largest pharmaceutical companies, and any credible claim of internal data exposure carries implications beyond one corporate environment.
Healthcare and life sciences organizations hold a mix of high-value assets, including:
- research and intellectual property
- sensitive employee and partner information
- regulated operational data
- supply chain and manufacturing records
- identity and access infrastructure
That combination makes the sector especially attractive to financially motivated and extortion-driven threat actors. Even if a leak does not include patient records, the exposure of internal systems, code, credentials, or infrastructure logic can still create material security risk.
This is also why the incident fits the broader pattern seen across recent healthcare cyber activity. Attackers increasingly look for leverage points that disrupt operations, create reputational pressure, or enable follow-on intrusion.
Is LAPSUS$ Really Behind the Alleged AstraZeneca Breach?
At this stage, the safest framing is that the breach was claimed by LAPSUS$ through Dark Web-related channels and a breach listing attributed to the group. The listing on the threat actors’ data leak site appears to advertise AstraZeneca data for sale.
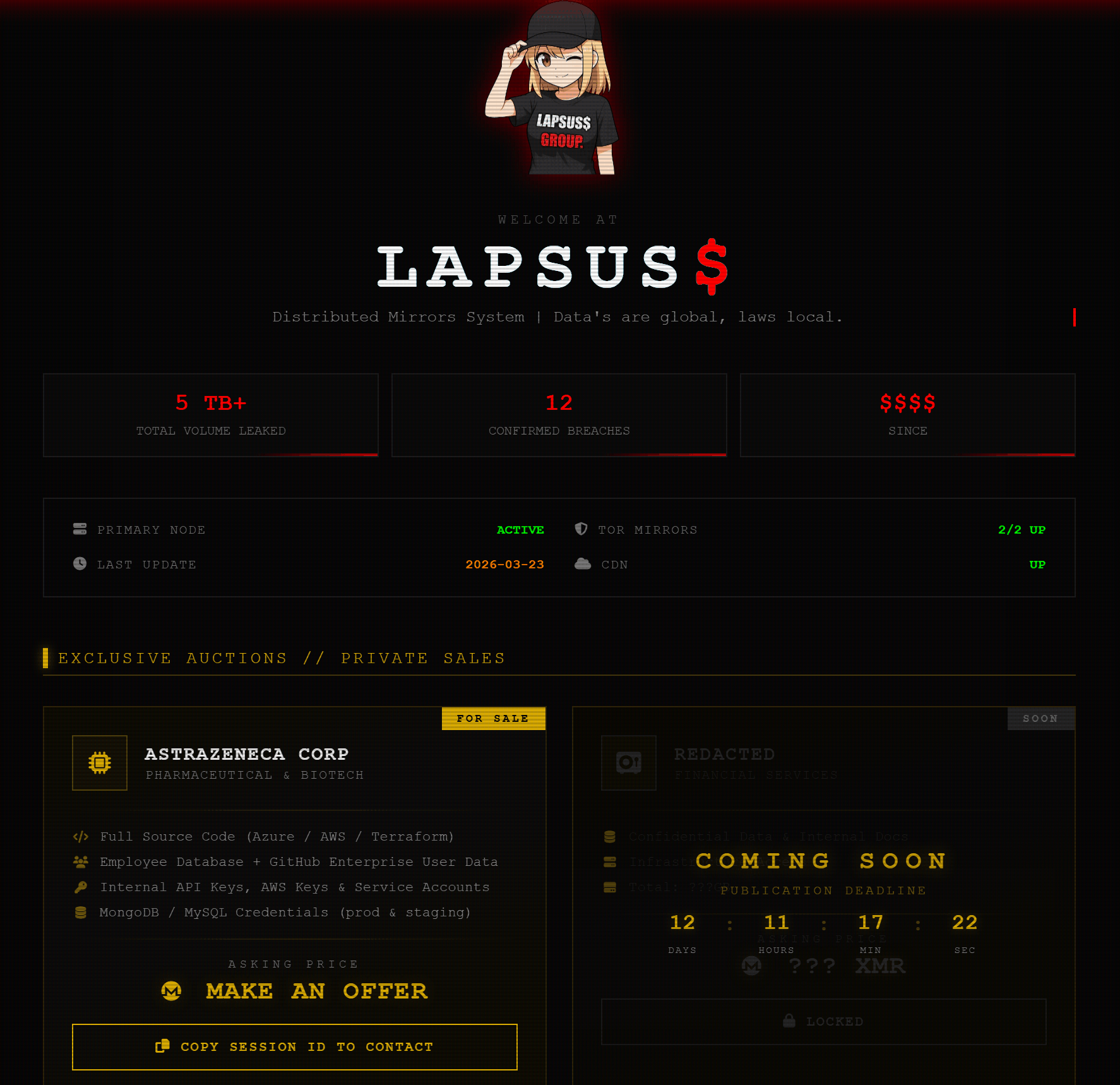
LAPSUS$ sale listing for alleged AstraZeneca data. Seemingly, there is no set price and the threat actor is taking offers.
For a broader look at the threat group behind this claim, readers can explore our , where we examine the group’s background, tactics, and targeting patterns in more detail.
Another Recent LAPSUS$ Activity Potentially Points to Mapfre
Another post by LAPSUS$, recently shared through their Telegram is shown below. It may indicate nearby activity or interest involving another organization, Mapfre, though it does not confirm a direct operational link between the two cases.
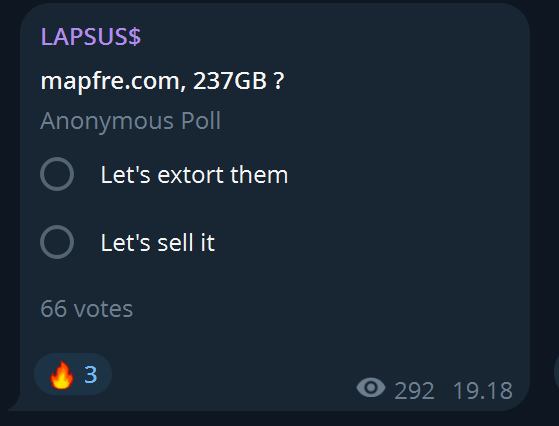
Recent Telegram activity from a LAPSUS$ channel referencing another possible target; relevance to the AstraZeneca claim remains unconfirmed
What Does the File Tree Suggest About the Leak?
The file tree is one of the more important pieces of context because it adds technical weight to the claim. Rather than showing random files, it appears to reflect a coherent internal project structure.
Several points stand out:
- AstraZeneca-branded Java package paths appear throughout the archive.
- The tree includes database scripts, table definitions, procedures, and views.
- Environment configuration files such as application-production.yml, application-sso.yml, and related deployment resources are visible.
- There are directories that suggest internal data handling, scheduling, inventory, forecasting, supplier, and order-management logic.
- The archive structure appears large and organized, reportedly spanning 1,486 directories and 5,892 files based on your team’s summary.
Taken together, that points to a potentially meaningful internal code and operations exposure rather than a small credential-only leak.
What Are the Immediate Risks?
If the claims are accurate, the short-term risks go beyond reputational damage.
- Follow-on intrusion risk: Exposure of source code, configuration files, and access-related records can help attackers identify weak points, understand application architecture, and plan additional intrusion attempts.
- Credential and identity abuse: Even partial account data can support , impersonation, MFA fatigue attempts, and privilege targeting. Threat actors do not always need passwords to turn identity data into access opportunities.
- Supply chain and partner impact: AstraZeneca operates in a large partner ecosystem. If the exposed materials include supplier, logistics, or collaboration data, the blast radius could extend to third parties.
- Extortion pressure: The auction-style language in the images suggests a monetization path through sale, selective release, or extortion. That can raise the risk even when immediate technical exploitation is not visible.
What Should Security Teams Watch Next?
For defenders in healthcare, pharma, and insurance, this incident is a reminder to monitor both initial access signals and Dark Web monetization activity at the same time.
Security teams should pay close attention to:
- Mentions of internal projects, domains, or repositories in Dark Web channels
- Suspicious login activity tied to developer, SSO, or GitHub Enterprise accounts
- Exposed secrets, service account misuse, or unusual cloud control-plane behavior
- Phishing campaigns that use leaked organizational context
- Third-party exposure involving partners, suppliers, or collaboration environments
This is also the kind of incident where continuous , credential exposure tracking, and can help teams detect whether a leak is escalating into a wider compromise.
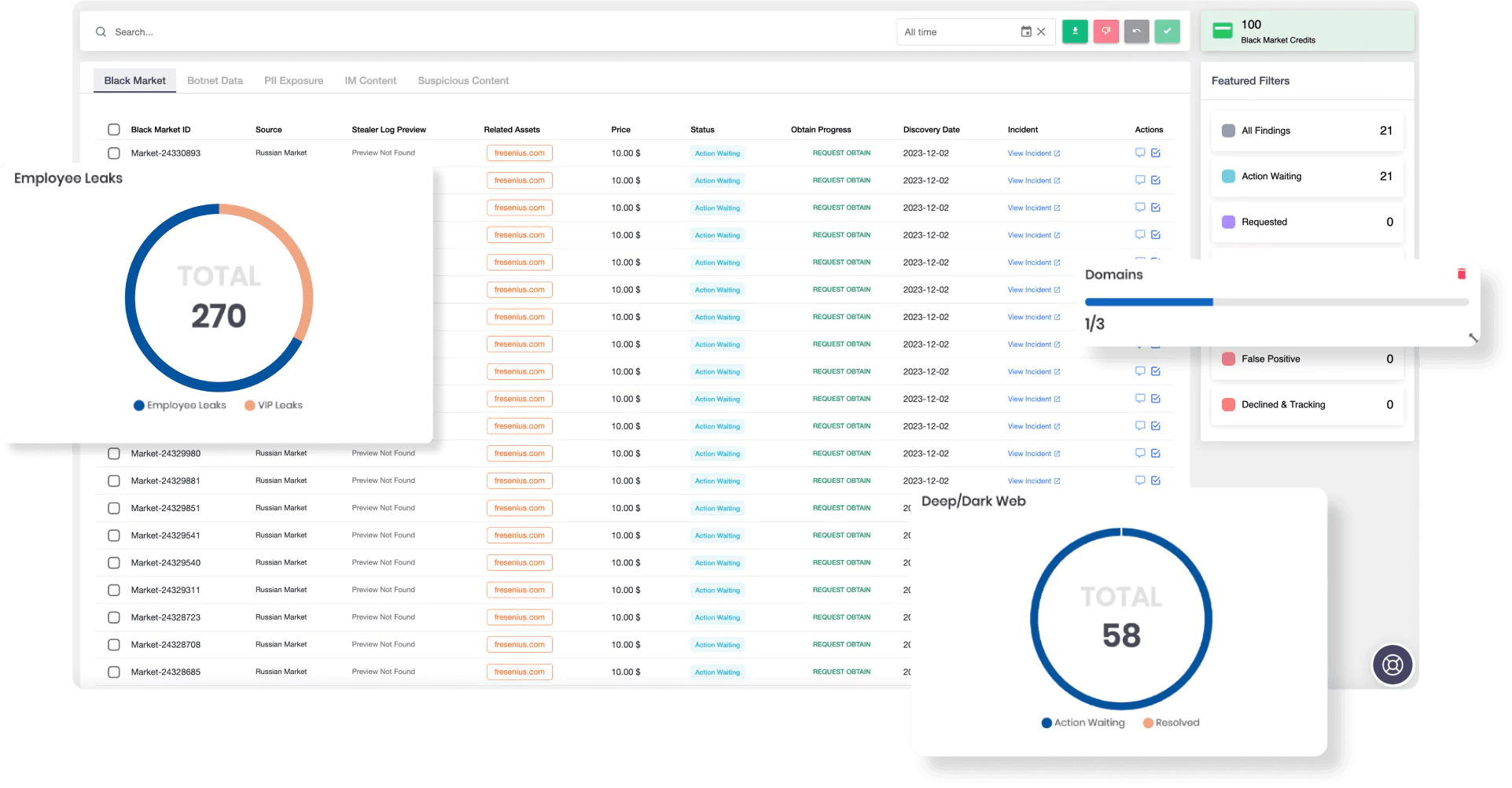
SOCRadar’s Dark Web Monitoring
Conclusion
The alleged AstraZeneca data breach deserves attention because it appears to combine several high-impact elements at once: a known extortion brand, claims of source code and cloud-related exposure, identity-linked sample data, and a file structure that looks consistent with real internal development and operational assets.
For the healthcare sector, the bigger lesson is clear. Breaches do not need to involve patient records alone to become major events. When attackers claim access to source code, access control data, and infrastructure-related material, the consequences can affect operations, partners, and long-term security posture alike.
As this story develops, the key question will be whether the leaked material proves authentic at scale and whether the incident expands into broader extortion, disclosure, or follow-on compromise activity.