Cyprus and Israel Under DDoS Siege: Weekly DDoS Threat Intelligence Analysis
Analysis Period: March 9 – 16, 2026
Between March 9 and 16, 2026, SOCRadar identified an extensive coordinated DDoS campaign conducted by the pro-Russian threat actor NoName057(16) using their DDoSia attack tool. The campaign resulted in 5,828 recorded attack entries, targeting 143 unique domains and 131 unique IP addresses across multiple countries, with a multi-national focus demonstrating the group’s expanding operational geography into the Eastern Mediterranean and the Middle East.
This campaign marks a significant geographic expansion for NoName057(16), with Cyprus accounting for 52.5% of all attacks (3,059 targets), complemented by substantial operations against Israel (12.7%), Romania (8.9%), and a broad range of internationally registered commercial domains (21.6%). The campaign reveals systematic targeting of government institutions at every administrative level, critical transportation infrastructure, financial services, defense-industrial entities, and independent media, all simultaneously, within a 7-day window.
The campaign’s 28 distinct target-list updates over seven days, with up to 10 file updates recorded on a single date (March 10) indicates highly automated command-and-control infrastructure and sustained operational commitment characteristic of a well-resourced, organized threat actor. The simultaneous appearance of Israeli defense contractors Elbit Systems and Israel Aerospace Industries (IAI) on target lists represents a notable escalation, signaling that NoName057(16) is now explicitly targeting the defense supply chain of nations perceived as supporting Ukraine’s military effort.
| Metric | Value |
| Analysis Period | March 9 – 16, 2026 |
| Total Attack Entries | 5,828 |
| Unique Domains Targeted | 143 |
| Unique IP Addresses | 131 |
| Primary Countries | Cyprus (52.5%), International/.com (21.6%), Israel (12.7%), Romania (8.9%), European Union (3.1%), Ukraine (1.3%) |
| Most Targeted Port | 443 (HTTPS) — 97.5% of all attacks |
| Threat Actor | NoName057(16) |
| Attack Tool / Project | DDoSia |
| Threat Classification | Critical ≥ 40 attacks · High ≥ 20 attacks · Medium < 20 attacks |
For comprehensive, real-time DDoS threat intelligence covering ongoing campaigns, explore SOCRadar’s free DDoS intelligence dashboard where we continuously analyze and publish actionable threat data sourced directly from DDoSia Telegram channels.
1. Campaign Analysis
Attack Volume and Scope
During the seven-day analysis period, the campaign demonstrated consistent, high-tempo operational intensity with daily target-list updates distributed through Telegram channels. A total of 28 JSON target files were recovered spanning March 9 through March 16, with several days showing multiple update cycles within hours — indicating the DDoSia C2 infrastructure maintains a near-continuous target refresh cadence designed to keep participating volunteer nodes persistently tasked without interruption.
The campaign’s multi-national scope encompasses four countries plus EU-registered entities, representing simultaneous pressure across the Eastern Mediterranean, the Middle East, and Eastern Europe:
- Cyprus accounted for 52.5% of all attack entries (3,059 attacks) across 44 unique targets
- International / Commercial domains (primarily .com entities with Cypriot, Israeli, or Romanian organizational ties) comprised 21.6% (1,257 attacks) across 31 unique targets
- Israel received 12.7% of attacks (739 attacks) across 40 unique targets — the highest number of distinct targets of any single country in this campaign
- Romania received 8.9% of attacks (518 attacks) across 20 unique targets
- European Union (.eu TLD entities) received 3.1% (178 attacks) across 2 unique targets
- Ukraine received 1.3% (77 attacks) across 3 unique targets
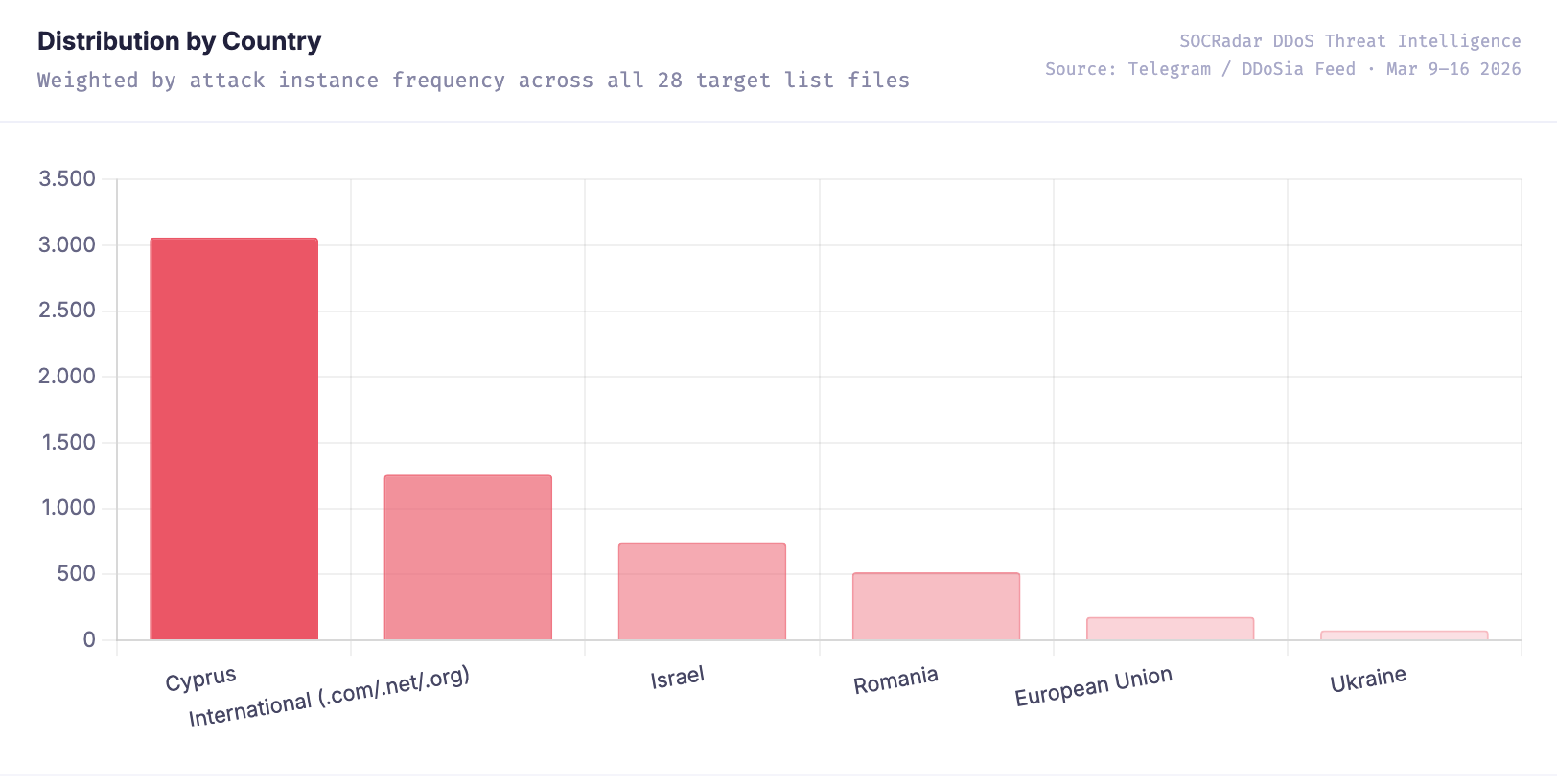
Distribution by Country (SOCRadar DDoS Threat Intelligence)
This distribution reflects a Cyprus-primary targeting strategy combined with coordinated secondary pressure across Israel, Romania, and Ukraine. The concentration on Cypriot infrastructure (52.5%) establishes it as the campaign’s primary objective, while simultaneous operations against Israeli municipalities and defense entities and Romania’s government and transportation networks prevent any single national response team from concentrating defensive resources effectively.
The sustained nature of attacks over seven consecutive days with 28 distinct target-list updates indicates highly coordinated operational planning and substantial C2 infrastructure. The timing of this campaign — coinciding with ongoing geopolitical discussions around Cyprus’s strategic role as a financial hub, and the broader context of the Iran-Israel-U.S. conflict in which Israel’s defense posture is under international scrutiny — suggests deliberate coordination with active geopolitical flashpoints, which we examine in detail below.
Targeted Sectors
The campaign demonstrated a comprehensive multi-sector targeting strategy affecting government institutions, critical transportation infrastructure, financial services, media, and defense-industrial entities simultaneously across all targeted countries.
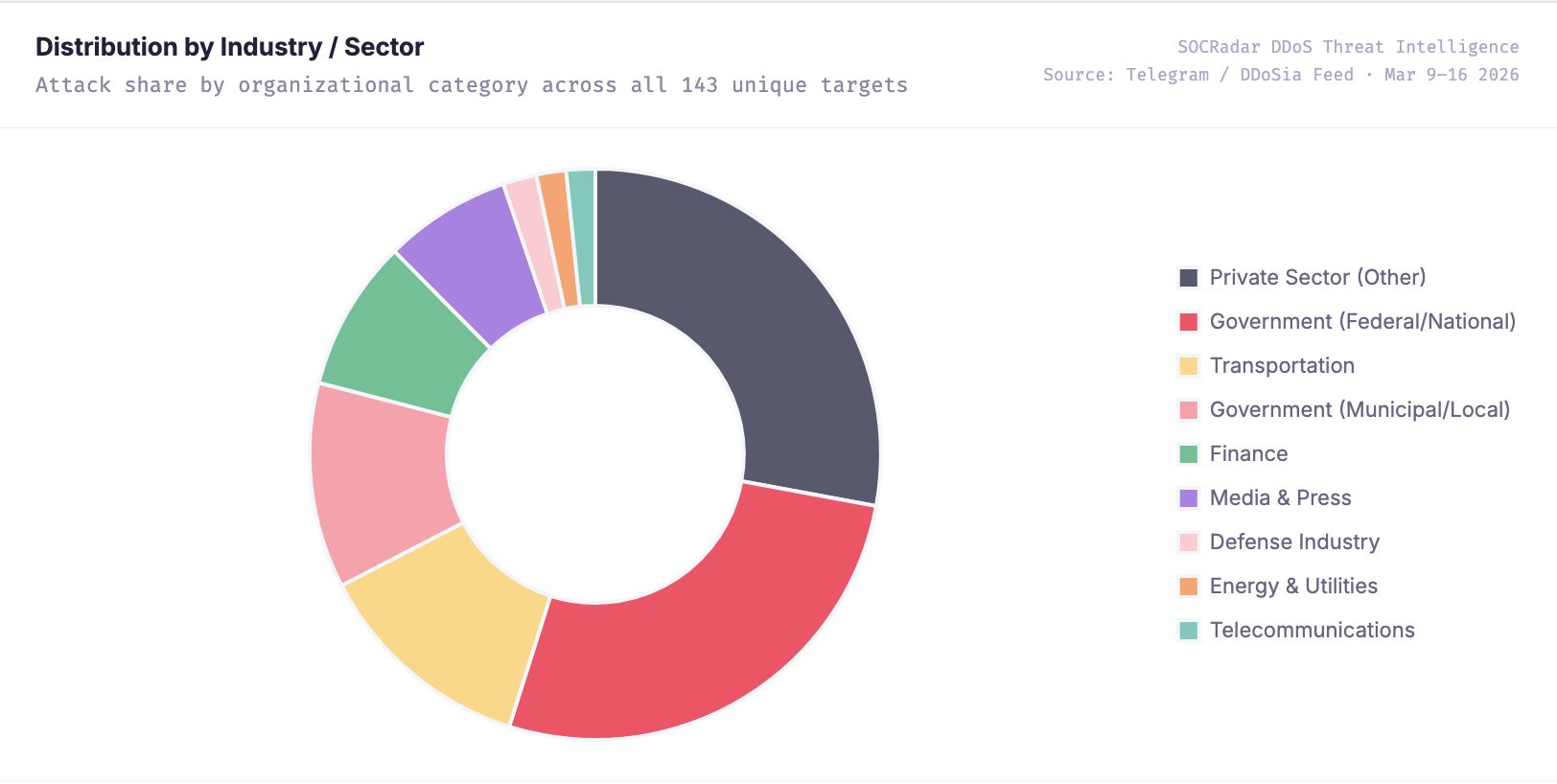
Distribution by Industry (SOCRadar DDoS Threat Intelligence)
Key targeted sectors included:
- Private Sector — Other (35.9%) — Commercial organizations, regional businesses, civil society entities, and general private sector companies across Cyprus and Israel
- Government Federal / National (27.0%) — Central government portals, ministries, national judiciary, police, electoral commissions, financial regulators
- Critical Infrastructure — Transportation (12.5%) — Airport express services, intercity bus operators, real-time transit platforms, rail cargo, and metro systems across Cyprus, Romania, and Israel
- Government Municipal / Local (11.6%) — City and municipality portals across Cyprus (Nicosia, Limassol, Pafos, Morphou, Agianapa) and Israel (Eilat, Modiin, Ariel, Rosh HaAyin, Lod, Abu Ghosh, Arraba)
- Private Sector — Finance (8.6%) — Major banks, national stock exchanges, insurance providers, and payment processors
- Private Sector — Media (7.2%) — Independent newspapers and broadcast news platforms in Cyprus and Israel
- Private Sector — Defense Industry (1.9%) — Defense contractors directly linked to weapons systems exported to Ukraine (Elbit Systems, IAI, Magam Safety)
- Critical Infrastructure — Energy (1.7%) — Electricity authority and chemical manufacturers
- Critical Infrastructure — Telecommunications (1.6%) — National telecom operator and ISP services
The combined government targeting at federal and municipal levels (38.6%) reflects a deliberate strategy to maximize symbolic political messaging while simultaneously disrupting citizen-facing services. The inclusion of defense-industrial entities — Elbit Systems and Israel Aerospace Industries — marks a significant escalatory step, moving beyond soft civilian targets to organizations directly embedded in the weapons supply pipeline to Ukraine.
Attack Techniques and Methods
NoName057(16) employed a strong application-layer-dominant attack strategy through the DDoSia framework, combining HTTP-layer resource exhaustion with transport-layer volumetric flooding. The technique distribution in this campaign diverges notably from previous NoName057(16) operations, which typically maintained a TCP-layer majority — reflecting deliberate adaptation to the specific server infrastructure profiles of Cypriot and Israeli government targets.
Most common methods observed:
- HTTP GET Flood attacks (52.3% — 3,049 attacks)
- HTTP POST-based attacks (30.1% — 1,757 attacks)
- TCP SYN Flood attacks (16.7% — 973 attacks)
- UDP Flood attacks (0.8% — 49 attacks)
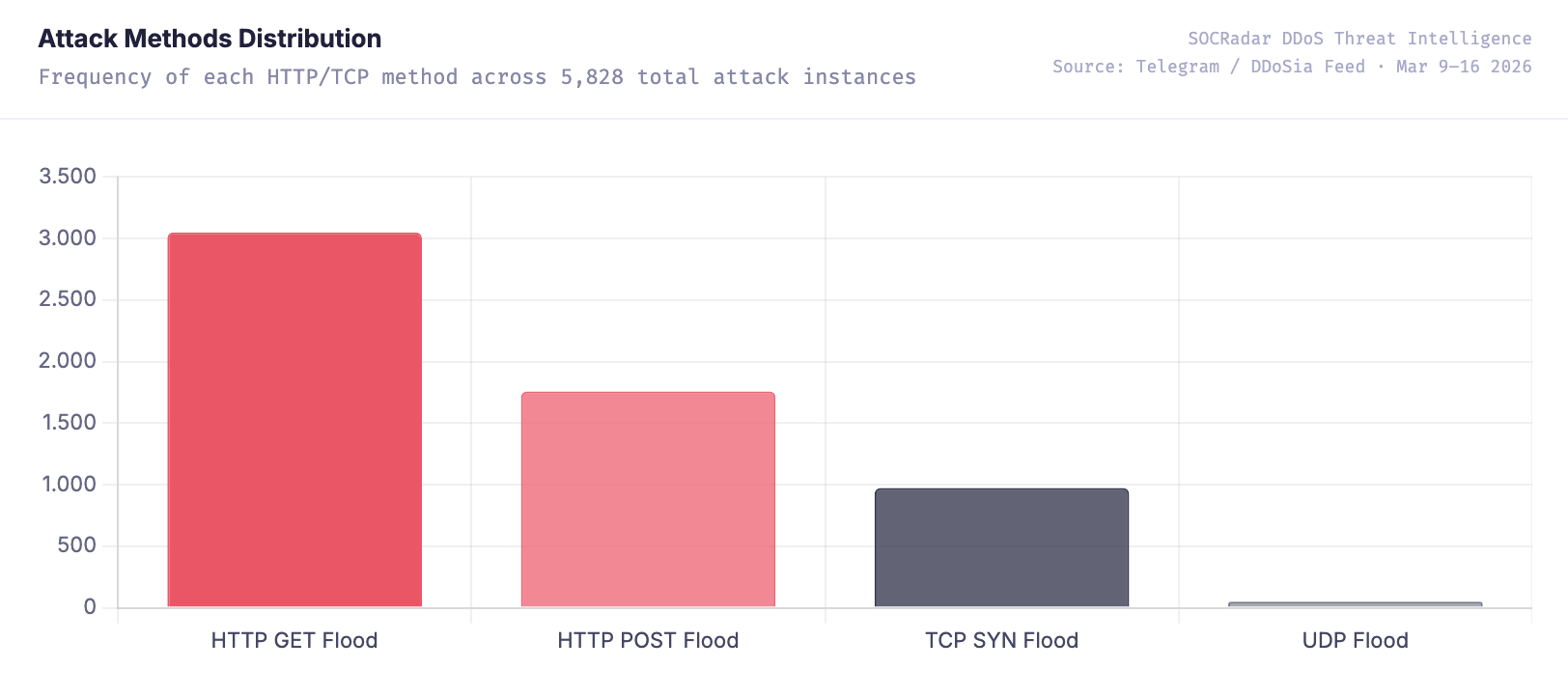
Attack Methods Distribution (SOCRadar DDoS Threat Intelligence)
The dominant use of HTTP GET floods (52.3%) combined with HTTP POST floods (30.1%) demonstrates a near-exclusive application-layer (L7) preference — together comprising 82.4% of all attack methods. This represents the group’s highest-ever recorded HTTP-layer proportion in a single campaign, significantly exceeding the 41.8% HTTP share observed in the Spain campaign (February 16–23, 2026) and the 35.7% observed in the UK campaign (January 26 – February 1, 2026).
This shift toward L7 dominance likely reflects intentional adaptation: many Cypriot and Israeli government services rely on CDN providers that effectively absorb TCP SYN floods, forcing the DDoSia tool to pivot toward authenticated HTTPS request flooding that consumes server-side processing resources directly. TCP SYN floods (16.7%) are still deployed against hardened targets, but function primarily as a complementary stressor rather than the primary attack vector.
Port targeting is highly concentrated: Port 443 (HTTPS) received 5,685 attacks — 97.5% of all traffic — a significantly higher HTTPS concentration than previous campaigns (UK: 65.1%, Japan: 67.2%, Spain: 69.8%). Port 80 (HTTP) received 143 attacks (2.5%), targeting primarily smaller municipal sites with incomplete TLS migration.
Attack types distribution:
- HTTP/1.1 application-layer attacks: 2,609 attacks (44.8%)
- HTTP/2 application-layer attacks: 1,973 attacks (33.8%)
- TCP-layer attacks: 973 attacks (16.7%)
- HTTP/3 application-layer attacks: 268 attacks (4.6%)
- Application-layer (nginx_loris): 5 attacks (0.1%)
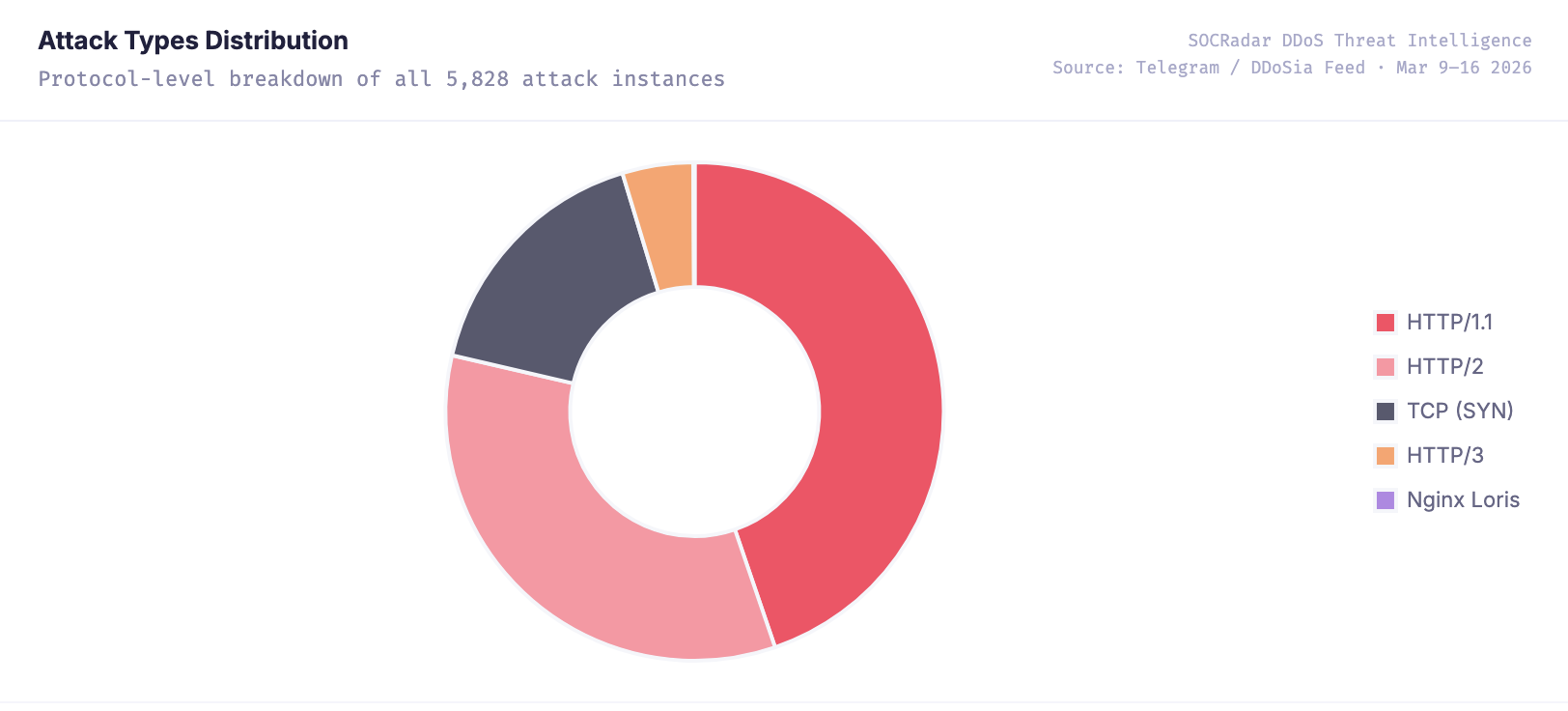
Attack Types Distribution (SOCRadar DDoS Threat Intelligence)
HTTP/1.1 (44.8%) and HTTP/2 (33.8%) together account for 78.6% of all attack traffic, reflecting a heavily layered application-layer methodology. The presence of HTTP/3 attacks (4.6%), while a minor share, demonstrates DDoSia’s capability to exploit QUIC-based protocols — an emerging attack surface that most enterprise DDoS mitigation platforms are not yet fully equipped to inspect and filter at scale.
2. Most Targeted Organizations
The campaign targeted a strategically curated mix of government services, critical infrastructure, defense-industrial entities, financial institutions, and independent media across Cyprus, Israel, Romania, and Ukraine. The selection demonstrates deliberate intelligence-driven planning: each organization’s presence on the target list reflects a calculated combination of geopolitical messaging value, civilian disruption potential, and symbolic significance.
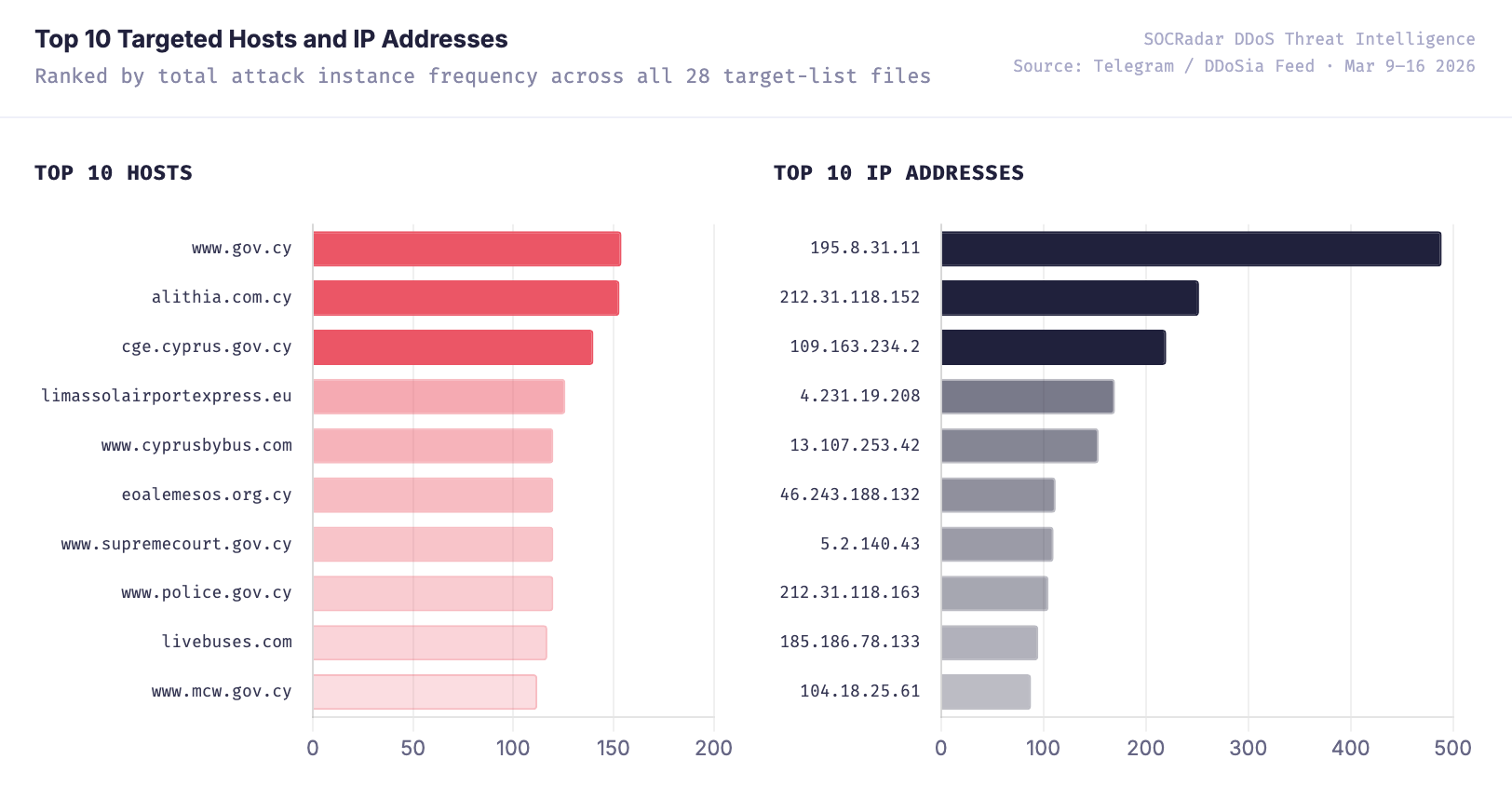
Top Targeted Hosts and IP Addresses (SOCRadar DDoS Threat Intelligence)
Cyprus — Primary Target (52.5%)
Cyprus dominated the campaign with 3,059 attack instances across 44 unique targets. The targeting profile reflects three simultaneous objectives: disrupting national government digital services, paralyzing public transportation, and suppressing independent pro-Western media.
Israel — Secondary Target (12.7%)
Israel received 739 attack instances across 40 unique targets — the highest target diversity of any country in this campaign, indicating a broad-sweep approach covering municipalities, private sector entities, media, finance, and defense-industrial companies. The breadth suggests intelligence-driven target selection rather than bulk-opportunistic listing.
The most significant entries in the Israeli target list are the defense contractors: Elbit Systems (30 attacks) and Israel Aerospace Industries — IAI (12 attacks). Both companies have faced government-level debates over arms exports to Ukraine, yet their inclusion on the DDoSia target list serves as an explicit political warning to the Israeli defense establishment. This targeting decision is directly linked to the escalating Iran-Israel-U.S. conflict dynamic, analyzed in detail in Section 3.
Israeli municipal portals received sustained attention across the country: Abu Ghosh (23 attacks), Eilat (22), Modiin (22), Ariel (20), Rosh HaAyin (17), Lod (11), and Arraba (13) were all targeted — spanning cities of varying sizes across Israel’s geographic spread. This breadth indicates a deliberate strategy to achieve nationwide coverage at the local governance layer, where cybersecurity resources are typically limited, generating the widest possible public awareness of the campaign’s reach.
Romania — Tertiary Target (8.9%)
Romania received 518 attack instances across 20 unique targets, with a distinct profile emphasizing government and transportation infrastructure. Romania’s geographic role as a NATO member bordering Ukraine — serving as a critical logistics corridor for Western military aid — makes it an inherently significant messaging target.
Key targets included the Romanian Parliament’s Chamber of Deputies (www.cdep.ro, 36 attacks), the Ministry of National Defence (www.mapn.ro, 34 attacks), and a coordinated cluster of transportation entities: Baneasa Airport (36 attacks), Tim Rail Cargo (34 attacks), Bucharest Metro Metrorex (24 attacks), and the national rail operator CFR (24 attacks).
The concurrent targeting of Romania’s air, rail, freight, and metro infrastructure within the same campaign window follows the same coordinated transportation cluster strategy observed in Cyprus — designed to simultaneously degrade the digital presence of all major transport mode operators, creating a compounding public awareness effect about the campaign’s reach into Romanian daily life.
3. Geopolitical Context: The Iran-Israel-U.S. Conflict and NoName057(16)’s Role
Why Israel Is Now a Primary DDoS Target
The inclusion of Israel in this campaign — and particularly the appearance of Elbit Systems and Israel Aerospace Industries (IAI) on DDoSia target lists — cannot be analyzed in isolation from the broader geopolitical context of the Iran-Israel-United States conflict that has intensified throughout late 2025 and into 2026.

SOCRadar’s live Iran-Israel Cyber War Dashboard tracks the cyber dimensions of Operation Epic Fury in real time.
In the months preceding this campaign, Israel conducted a series of strikes on Iranian nuclear infrastructure, triggering retaliatory Iranian ballistic missile and drone attacks against Israeli territory. The United States maintained active military positioning in the region in support of Israel, while simultaneously managing diplomatic pressure on NATO allies over continued Ukraine support. This tripartite tension — the Israel-Iran direct conflict, U.S. regional military engagement, and the ongoing Ukraine war — created a geopolitical environment in which pro-Russian hacktivist groups found multiple, concurrent rationales to target Israeli infrastructure.
The Russian-Iranian Strategic Alignment
Russia and Iran have maintained deepening strategic cooperation throughout the Ukraine conflict, with Iran supplying Shahed-series drones that Russian forces have used extensively against Ukrainian civilian infrastructure. This alignment creates a shared adversarial interest: both Russia and Iran view Israeli military capability — particularly Israeli defense exports — as a threat to their respective regional objectives.
NoName057(16), operating as a pro-Kremlin information warfare instrument, has thus absorbed anti-Israel targeting objectives that align with both Russian and Iranian strategic interests. The group’s Telegram messaging during the campaign period explicitly framed Israeli targets through the lens of the Iran-Israel conflict, characterizing Israel as an aggressive Western-aligned actor — a framing that broadens the ideological coalition from which DDoSia draws volunteer participants beyond the traditional pro-Russian base to include pro-Iranian sentiment as well.
Elbit Systems and IAI: Targeting the Defense Supply Chain
The targeting of Elbit Systems (Israel’s largest publicly traded defense electronics company) and Israel Aerospace Industries (IAI, a state-owned manufacturer of missile defense systems and UAVs) represents a qualitative escalation in NoName057(16)’s targeting doctrine. Both companies have been subjects of Israeli government debate over drone, electronic warfare, and missile defense exports to Ukraine.
By placing Elbit and IAI on DDoSia target lists, NoName057(16) transmits a dual message: first, a direct political warning to the Israeli defense establishment that continued weapons supply discussions with Ukraine will attract cyber harassment campaigns; and second, a signal to Iran and pro-Iranian proxy groups that Russian-aligned hacktivist infrastructure is actively targeting Israeli strategic assets — a form of cyber solidarity that reinforces the Moscow-Tehran axis in digital operations.
Cyprus as a Regional Flashpoint Proxy
Cyprus’s dominant campaign share (52.5%) must also be understood within the context of the broader regional conflict dynamic. Cyprus sits at a strategic junction of Eastern Mediterranean security — it hosts British Sovereign Base Areas that have been operationally active during regional escalations, serves as a financial and logistics hub with significant historical exposure to Russian capital flows, and has been a point of diplomatic friction regarding sanctions enforcement against Russian entities.
During the Iran-Israel escalation in 2025, Cyprus’s waters and airspace became operationally significant as regional military traffic increased. NoName057(16)’s campaign targeting Cypriot government portals, transportation infrastructure, and financial institutions thus functions simultaneously as anti-NATO messaging, pro-Russian geopolitical signaling, and a demonstration of hacktivist capability in a region of active great-power competition.
NoName057(16)’s Expanding Geographic Mandate
Historically, NoName057(16) concentrated its operations on continental Europe — targeting Poland, Baltic states, Germany, France, the UK, and Nordic countries in sequential weekly campaigns. The March 2026 campaign extending to Cyprus, Israel, and Romania simultaneously represents a documented geographic expansion of the group’s operational mandate.
The group’s targeting now encompasses the full arc of states that collectively represent Western support for Ukraine: NATO’s eastern European members (Romania), NATO’s Mediterranean members (Cyprus), G7-aligned Middle Eastern partners (Israel), and transatlantic commercial infrastructure. This expansion is consistent with a broader evolution in Russian-aligned cyber operations: as direct kinetic conflict in Ukraine has entered a prolonged phase, information warfare and hacktivist harassment campaigns are being scaled geographically to sustain political pressure across an ever-wider coalition of Ukraine’s supporters.
The Iran-Israel conflict provided a timely opportunity for NoName057(16) to justify Israeli targeting to its volunteer base — but the underlying strategic logic reflects a Kremlin-aligned campaign to harass, destabilize, and signal capability to every nation that has chosen to stand against Russian objectives in Ukraine and the broader reshaping of the post-Cold War security order.
SOCRadar Assessment: Organizations in Israel, Cyprus, Romania, and other nations maintaining active Ukraine support positions should treat this campaign as indicative of a sustained, escalating harassment campaign rather than a transient tactical operation. The convergence of the Ukraine conflict, the Iran-Israel flashpoint, and Russia-Iran strategic alignment creates structural conditions for continued and intensifying DDoS activity against a growing range of targets across multiple continents throughout 2026.
4. Threat Actor Overview: NoName057(16)
NoName057(16) is a pro-Russian hacktivist collective that emerged in March 2022 following Russia’s full-scale invasion of Ukraine. The group has established itself as the most persistent and prolific hacktivist actor conducting sustained DDoS campaigns against NATO member states, EU countries, and nations perceived as supporting Ukraine — operating continuously since its founding with no documented pause exceeding two weeks.

Threat actor card of NoName057(16)
The group operates through a crowdsourced, volunteer-driven model using the custom DDoSia botnet framework distributed via Telegram. This model provides distributed attack infrastructure resistant to attribution and disruption, plausible deniability for state-level involvement, and the ability to mobilize thousands of volunteer participants through gamification, per-block cryptocurrency reward distribution, and ideological motivation.
NoName057(16) operations consistently align with Russian geopolitical objectives. Prior major campaigns have targeted Poland, Baltic states, Germany, France, Netherlands, UK, Japan, Denmark, Sweden, Czech Republic, and Spain before this March 2026 Mediterranean and Middle Eastern expansion.
DDoSia Framework
The technical infrastructure supporting NoName057(16) centers on the DDoSia crowdsourced attack tool. The framework provides a user-friendly interface for non-technical participants, receives centralized target lists updated multiple times daily via Telegram, and implements multiple attack vectors including TCP SYN floods, HTTP/1.1 GET and POST floods, HTTP/2, and HTTP/3 application-layer attacks. The tool reports attack metrics back to central infrastructure for performance tracking, enabling per-participant volume calculations for cryptocurrency reward distribution.
In this campaign, 28 JSON target files were distributed over 7 days — an average of 4 updates per day, with March 10 recording 10 separate file updates. The 85%+ overlap between consecutive target list files confirms persistent multi-day tasking rather than daily strategic pivots — each organization on the list is targeted for the duration of the campaign, not just briefly sampled.
5. Mitigation and Recommendations
Organizations in the affected sectors — government institutions, transportation operators, financial services, media, defense-industrial entities, and telecommunications providers across Cyprus, Israel, Romania, and Ukraine — should implement the following protective measures:
- Deploy Layer 7 DDoS Mitigation Immediately. Given the campaign’s 82.4% application-layer HTTP attack composition — the highest proportion ever recorded in a NoName057(16) campaign — traditional volumetric scrubbing is insufficient as a primary defense. Organizations must activate WAF rate limiting, bot detection, CAPTCHA challenge mechanisms, and behavioral analysis at application ingress points. CDN-backed L7 DDoS protection with rules tuned for high-volume GET and POST request rates is strongly recommended for all exposed government and financial portals.
- Prioritize HTTPS Traffic Inspection (Port 443). With 97.5% of attacks targeting port 443, SSL termination at the CDN or load-balancer layer is essential to enable inspection of encrypted attack traffic before it reaches origin servers. DDoS mitigation platforms that cannot inspect decrypted HTTPS traffic in real time are effectively blind to the dominant attack vector in this campaign.
- Implement Rate Limiting and IP Reputation Blocking. DDoSia volunteer nodes are distributed across residential and commercial IP ranges globally. Configure per-IP and per-subnet request rate thresholds on all public-facing services. Subscribe to threat intelligence feeds providing continuously updated DDoSia node IP indicators — SOCRadar maintains active DDoSia node telemetry based on direct Telegram channel monitoring.
- Prepare for Sustained Multi-Day Campaign Duration. NoName057(16) campaigns consistently run 7 days or longer with no voluntary de-escalation. Organizations should not stand down defenses after the first day. Incident response plans must be designed for sustained operational posture over 7–14 days minimum, with pre-positioned escalation contacts to upstream ISPs and DDoS scrubbing providers.
- Alert Municipal and Regional Authorities with Limited IT Resources. This campaign targets 12 or more municipal and city-level portals across Cyprus and Israel — organizations that typically operate with constrained cybersecurity budgets and minimal DDoS-specific tooling. National CERTs (CSIRT-CY, CERT-IL, CERT-RO) should issue active alerts to municipal IT administrators with specific low-cost mitigation guidance and contact information for emergency assistance.
- Defense-Industrial Entities Should Elevate to Enhanced Alert Posture. The inclusion of Elbit Systems and IAI on DDoSia target lists signals that NoName057(16) is now explicitly targeting defense supply chain entities. Defense contractors in Israel and their European counterparts should treat this as a confirmed indicator of intent and review DDoS resilience for customer-facing and partner-facing web services.
6. Conclusion
Between March 9 and 16, 2026, NoName057(16) conducted a sustained, multi-country DDoS campaign via the DDoSia crowdsourced attack tool, generating 5,828 attack instances across 143 unique targets and 131 unique IP addresses spanning Cyprus, Israel, Romania, Ukraine, and EU-registered entities. The campaign’s primary focus on Cyprus (52.5%) combined with broad Israeli targeting across 40 organizations — including the explicit inclusion of defense contractors Elbit Systems and Israel Aerospace Industries — marks a geographic and strategic escalation that extends the group’s operational footprint from Western and Northern Europe into the Eastern Mediterranean and Middle East.
The campaign’s technical signature — 82.4% application-layer (L7) HTTP attacks, near-exclusive HTTPS targeting (97.5%), and a marked departure from the TCP-layer volumetric approach dominant in previous campaigns — reflects deliberate adaptation to the infrastructure characteristics of Cypriot and Israeli government targets. This is not tactical opportunism; it is evidence of an evolving, technically adaptive operation.
The Iran-Israel-U.S. conflict context provides critical explanatory framing for the Israeli targeting dimension of this campaign. The deepening Russia-Iran strategic alignment, Iran’s interest in degrading Israeli defense industrial capacity, and NoName057(16)’s documented pattern of absorbing geopolitically convenient targeting narratives collectively explain why a group nominally focused on Ukraine’s NATO supporters is now directing attack resources against Israeli infrastructure. Defense contractors Elbit Systems and IAI are the clearest evidence of this convergence — their presence on a DDoSia target list represents a fusion of pro-Russian and pro-Iranian hacktivist targeting logic that is likely to persist and intensify as the Iran-Israel-U.S. conflict remains unresolved.
SOCRadar continues our commitment to protecting organizations with enhanced DDoS threat intelligence capabilities. We are continuously analyzing and showcasing free DDoS threat intelligence through SOCRadar Labs, providing real-time visibility into ongoing campaigns.